[ad_1]

A massive ad fraud operation dubbed “Vastflux” that spoofed more than 1,700 apps from 120 vendors, mostly for iOS, has been halted by security researchers from cybersecurity firm HUMAN.
The name of the operation is derived from the VAST ad serving model and the “fast flux” evasion technique used to conceal malicious code by rapidly modifying large numbers of IP addresses and DNS records associated with a single domain.
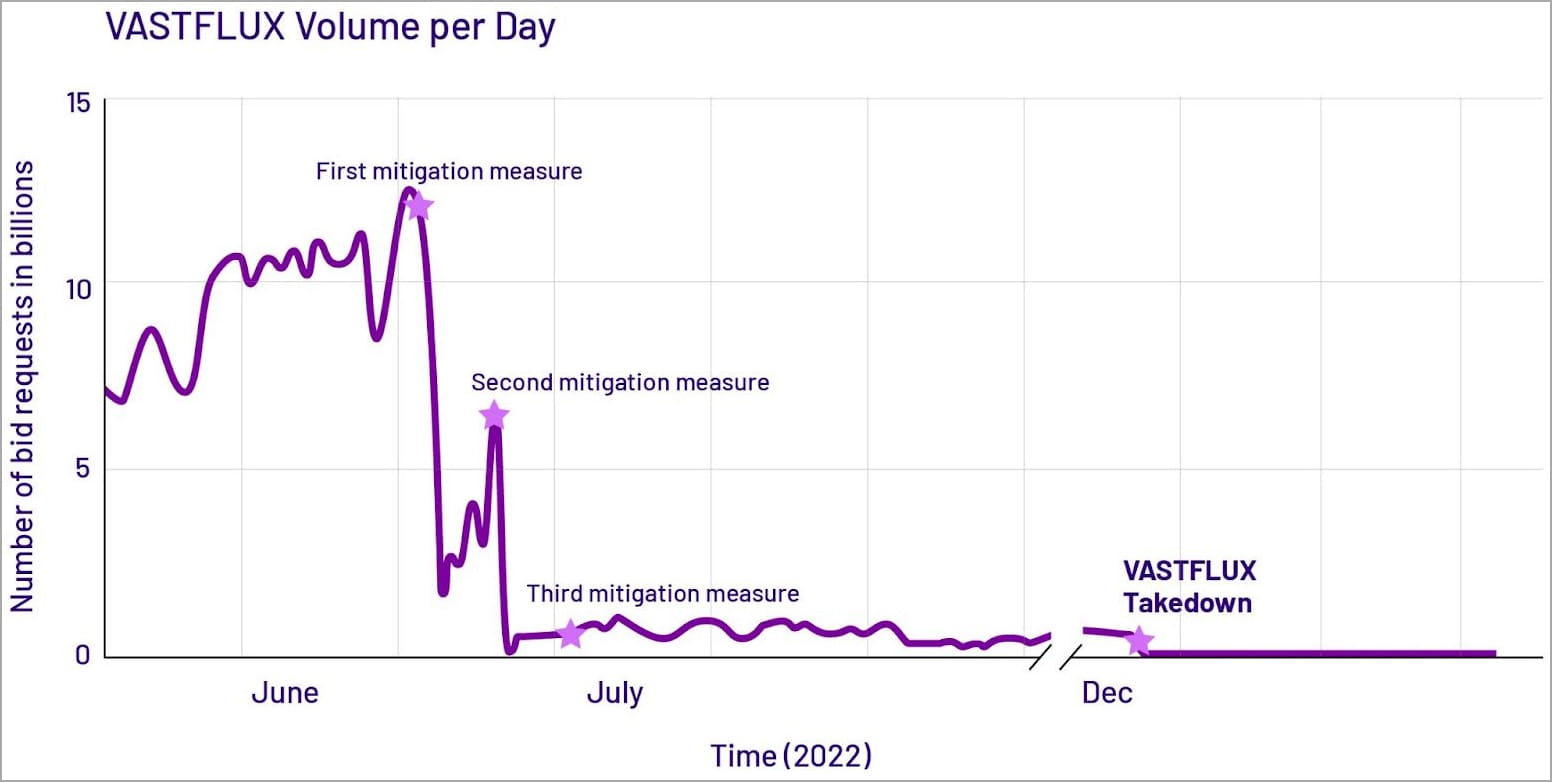
According to HUMAN’s report, Vastflux generated more than 12 billion bid requests per day at its peak and impacted nearly 11 million devices, many of them in Apple’s iOS ecosystem.
Vastflux Details
The HUMAN (Satori) research team discovered Vastflux while investigating a separate ad fraud scheme. They noticed that an app was generating an unusually high number of requests using different app IDs.
By reverse-engineering the obfuscated JavaScript that worked in the app, the Satori team discovered the IP address of the command-and-control (C2) server it was communicating with and the ad-generating commands it sent.
Vastflux generated bids for displaying in-app banner ads. If it won, it would place a static banner image and inject obfuscated JavaScript into it.
The injected scripts contacted the C2 server to receive an encrypted configuration payload, which included instructions on the position, size, and type of ads to display, as well as data to spoof the real app and app IDs. ‘editor.
Vastflux stacked up to 25 video ads on top of each other, all generating revenue from ad views, but none of them were visible to the user because they were rendered behind the active window.
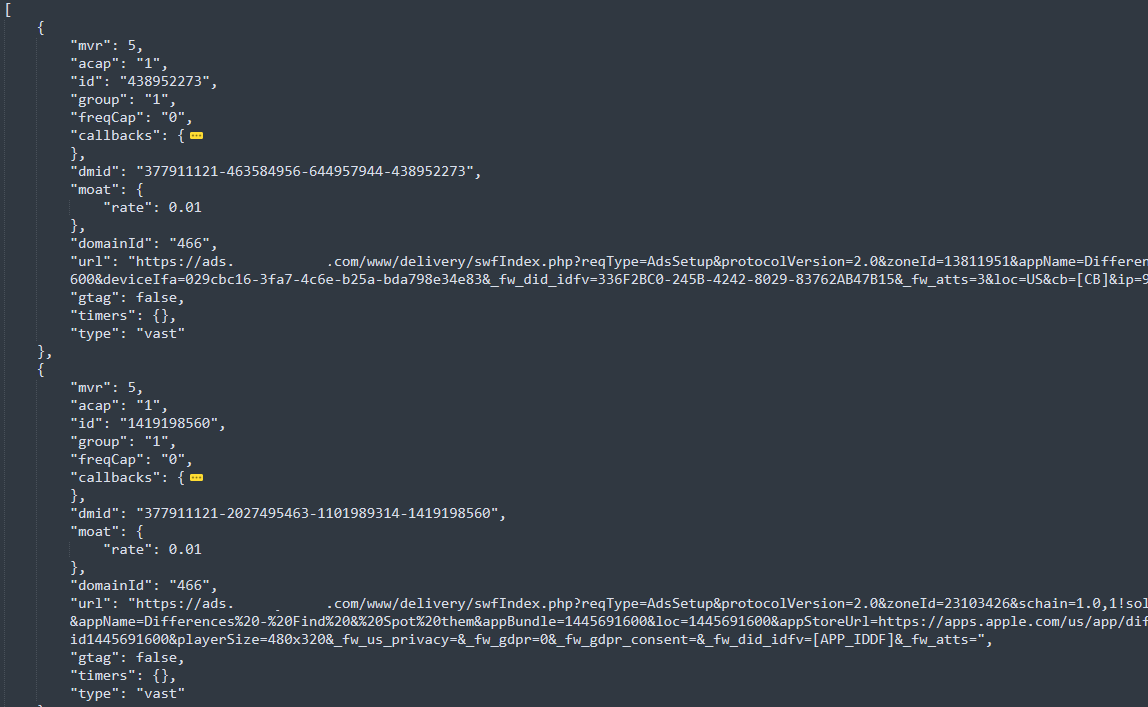
To evade detection, Vastflux omitted the use of ad verification tags, which allows marketers to generate performance metrics. By avoiding them, the system has been made invisible to most third-party advertising performance trackers.
Removal of Vastflux
After mapping the infrastructure of Operation Vasstflux, HUMAN launched three waves of targeted actions between June and July 2022, involving customers, partners and impersonated brands, each dealing a blow to fraudulent activity.
Eventually, Vastflux took its C2 servers offline for a while and scaled down operations, and on December 6, 2022, ad bidding fell to zero for the first time.
Although Ad Fraud does not have any malicious impact on the app users, it does cause the device to drop in performance, increase battery and internet data usage and may even lead to overheating of the app. the device.
The above items are common signs of adware infections or ad fraud in the device, and users should treat them with suspicion and try to identify the app(s) that is accounting for the bulk of the device consumption. resources.
Video ads consume much more power than static ads, and several hidden video players are not easy to hide from performance monitors, so it’s crucial to always keep an eye on running processes and research signs of trouble.
[ad_2]
Source link
