[ad_1]

Google has removed 32 malicious extensions from the Chrome Web Store that may alter search results and deliver spam or unwanted ads. Collectively, they come with a download count of 75 million.
The extensions had legitimate features to keep users unaware of the malicious behavior that came in the obfuscated code to deliver the payloads.
Cybersecurity researcher Wladimir Palant analyzed the PDF Toolbox extension (2 million downloads) available on Chrome Web Store and found that it included code disguised as a legitimate extension API wrapper.
In a writing mid-May, the researcher explains that the code allowed the “serasearchtop[.]com” to inject arbitrary JavaScript code into any website visited by the user.
The potential for abuse ranges from inserting advertisements into web pages to stealing sensitive information. However, Palant did not observe any malicious activity, so the purpose of the code remained unclear.
The researcher also noticed that the code was configured to activate 24 hours after installing the extension, a behavior usually associated with malicious intent.
A few days ago, Palant published a monitoring station on the case to alert that he had discovered the same suspicious code in 18 other Chrome extensions with a total number of downloads of 55 million. Here are some examples :
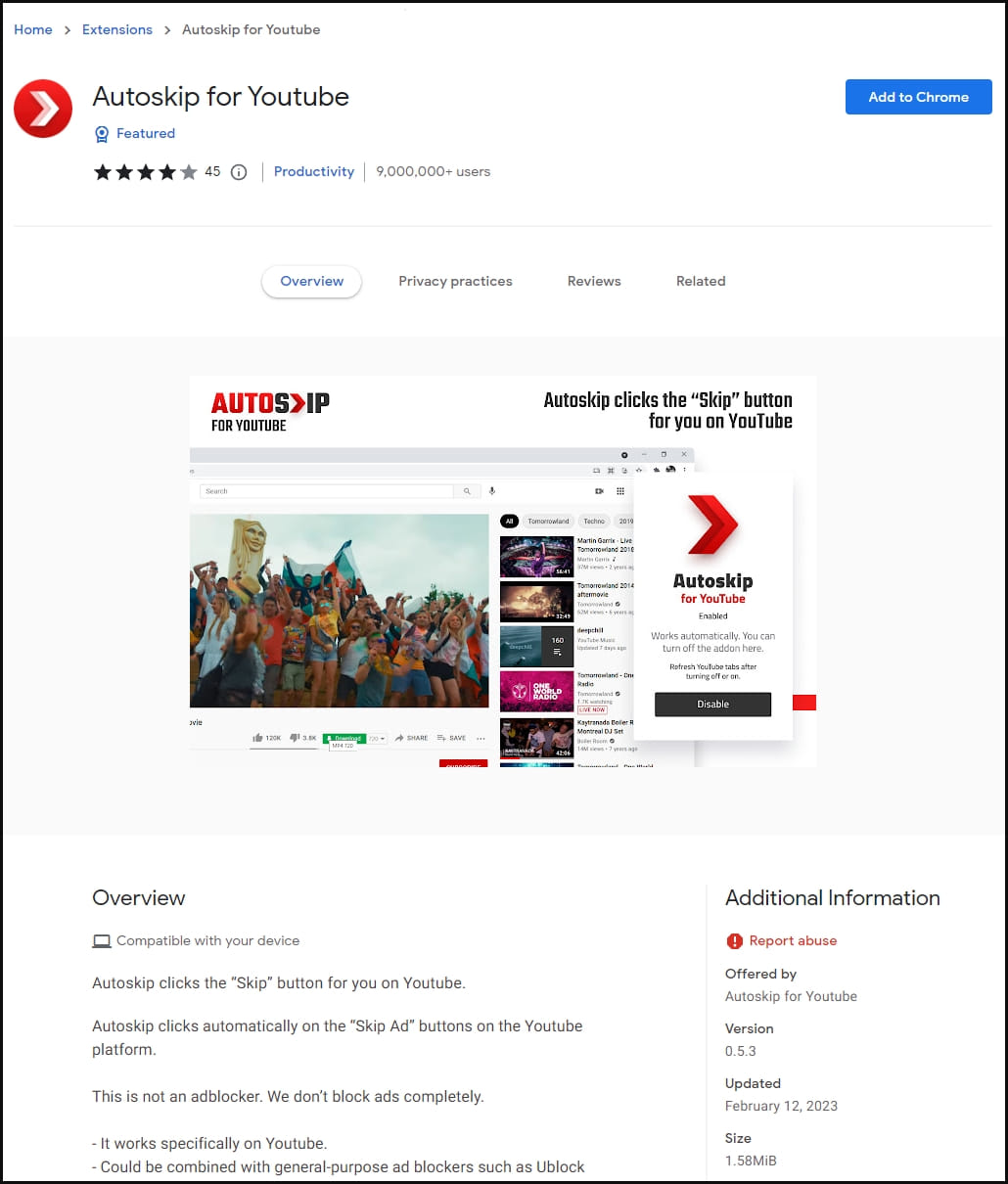
- Autoskip for Youtube – 9 million active users
- Soundboost – 6.9 million active users
- Block Crystal Ad – 6.8 million active users
- Dynamic VPN – 5.6 million active users
- Clipboard Helper – 3.5 million active users
- Maxi Refresher – 3.5 million active users
At the time Palant published the second article, all extensions were still available in the Chrome Web Store.
Continuing its investigation, Palant found two variants of the code: one impersonating the Polyfill API of Mozilla’s WebExtension browser, and another impersonating the Day.js library.
However, both versions had the same mechanism for injecting arbitrary JS code involving serasearchtop[.]com.
Although the researcher did not observe any clear malicious activity, he noted that there are numerous reports and user reviews on the Web Store indicating that the extensions perform redirects and hijack search results.
Despite its attempts to report the suspicious extensions to Google, they remained available to Chrom Web Store users.
Earlier today, however, cybersecurity firm Avast said it reported the extensions to Google after confirming their malicious nature and expanding the list to 32 entries. Collectively, these have seen 75 million installs.
Avast said that while extensions appear harmless to unsuspecting users, they are adware that hijacks search results to display sponsored links and paid results, sometimes even serving malicious links.
Responding to a request for comment from BleepingComputer before Avast released its findings, a Google spokesperson said “the reported extensions have been removed from the Chrome Web Store.”
“We take security and privacy claims against extensions seriously, and when we find extensions that violate our policies, we take appropriate action.”
“The Chrome Web Store has policies in place to ensure user safety that all developers must adhere to,” the Google representative told BleepingComputer.
Avast highlights the significant impact of the extensions, which targeted tens of thousands of its customers, and potentially millions worldwide.
For its customers, Avast has selectively neutralized only malicious elements within extensions, letting legitimate functionality continue to function uninterrupted.
While the 75 million downloads look worrying, the company suspects the number has been “artificially inflated”. A full list of malicious extensions (IDs) can be found at Avast’s report.
Users should note that removing extensions from the Chrome Web Store does not automatically disable or uninstall them from their browsers, so manual action is required to eliminate the risk.
[ad_2]
Source link
