[ad_1]

A cyberattack hitting the Port Authority of Lisbon (APL), Portugal’s third-largest port, on Christmas Day has been claimed by the LockBit ransomware gang.
The port of Lisbon is part of the essential infrastructure of the Portuguese capital, being one of the most accessible ports in Europe, due to its strategic location, and serving container ships, cruise ships and boats of pleasure.
According to a company statement shared Monday with local media, the cyberattack had no impact on port operations.
“All the security protocols and response measures foreseen for this type of event were quickly activated, with the situation being monitored by the National Cybersecurity Center and the Judicial Police,” reads the announcement shared with the Portuguese national newspaper. public.
“The Port of Lisbon Administration (APL) works continuously and closely with all relevant entities to ensure the security of the respective systems and data,” the publication’s statement reads.
As of this writing, the port’s official website at “portodelisboa.pt” remains offline.
LockBit data leak threat
APL did not reveal the nature of the cyberattack in the announcement, but ransomware group LockBit added the organization to its extortion site yesterday, claiming responsibility for the attack.
The ransomware gang claims to have stolen financial reports, audits, budgets, contracts, cargo information, logbooks, crew details, customer PII (personally identifiable information), port documents, e-mail correspondence, etc.
The group has already published samples of the stolen data but BleepingComputer could not verify their legitimacy.
LockBit threatens to release all of the files they stole during the January 18, 2022 computer intrusion, if their demands for payment are not met.
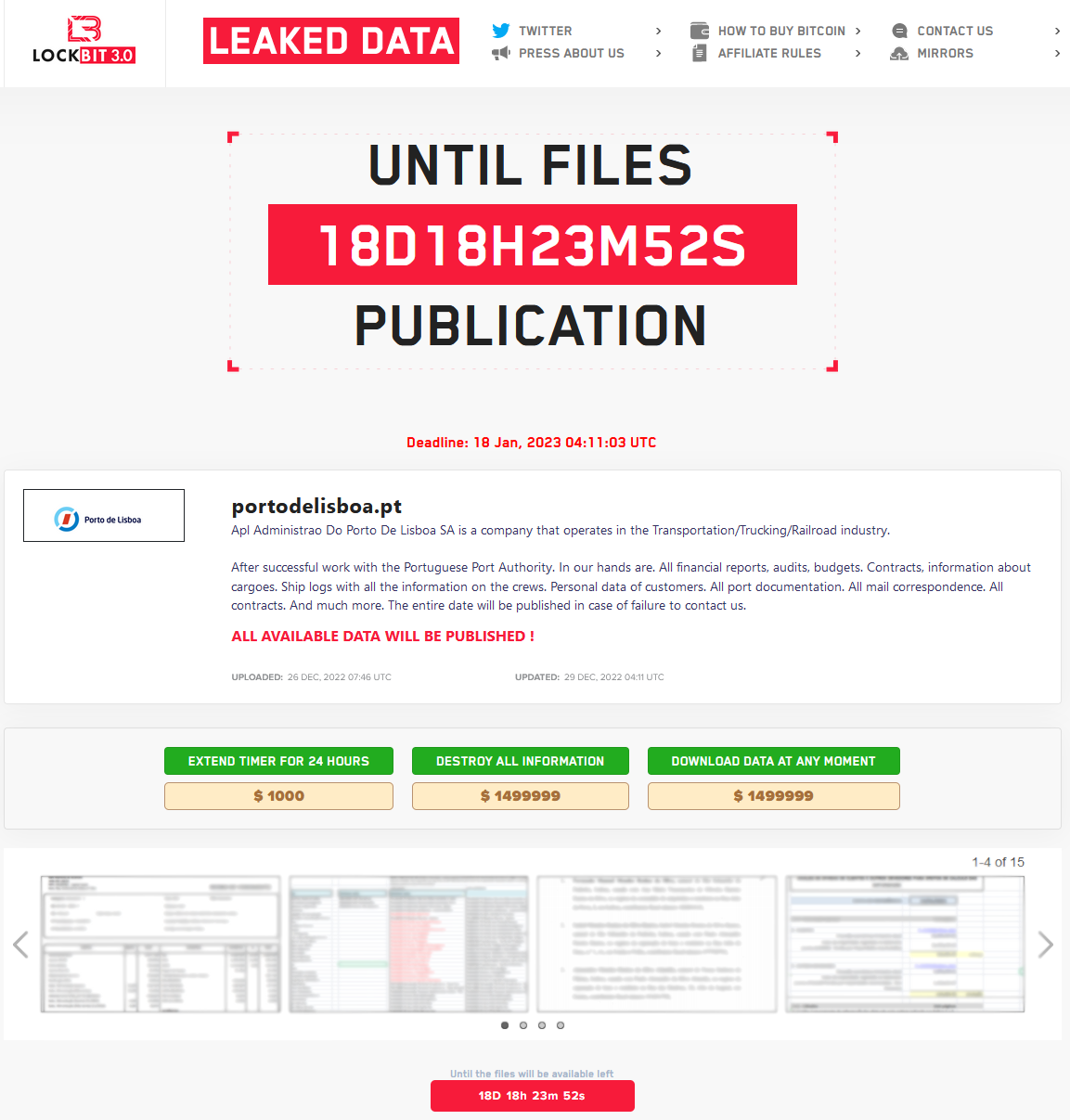
As seen in the image above, the threat actor has set the ransom at $1,500,000 and also gives the option to delay the data release for 24 hours by paying $1,000.
Interestingly, LockBit offers to sell the data for the same amount to anyone who wants immediate and exclusive access to it.
The LockBit gang is currently on the third release of their cipher that powers the notorious RaaS (ransomware as a service) project, and one of the most prolific gangs this year.
Another notable recent LockBit attack targeted Continental, the multinational automotive giant, which was listed on the ransomware gang’s Tor site. in November 2022.
This week, the Japanese media rumors have been circulating that the Japanese police’s cybercrime department helped at least three domestic companies restore their systems for free after the LockBit 3.0 attacks.
[ad_2]
Source link
