[ad_1]

A new Lazarus campaign believed to be part of “Operation DreamJob” has been discovered targeting Linux users with malware for the first time.
This new targeting was uncovered by ESET researchers, who say it also confirms with high confidence that Lazarus conducted the recent supply chain attack on the 3CX VoIP provider.
The attack was discovered in March 2023, compromising several companies that were using the trojanized version of the 3CX client with information-stealing Trojans.
Lazarus was already suspected to be responsible for the attack, while several cybersecurity companies have agreed with high confidence that the threat actor who created the 3CX Trojan was North Korean link.
Today, Mandiant released the results of their investigation in the 3CX breach, further linking the attack to North Korean threat actors.
Mandiant claims that 3CX’s development environment was compromised after an employee installed trading software from Trading Technologies, the installer of which was infected with a Trojan in another blockchain attack. North Korean supply.
DreamJob Operation in Linux
Lazarus’ Operation DreamJob, also known as Nukesped, is an ongoing operation targeting people who work in software or DeFi Platforms with fake job offers on LinkedIn or other social media and communication platforms.
These social engineering attacks attempt to trick victims into downloading malicious files disguised as documents containing details of the job being offered. However, these documents instead drop malware onto the victim’s computer.
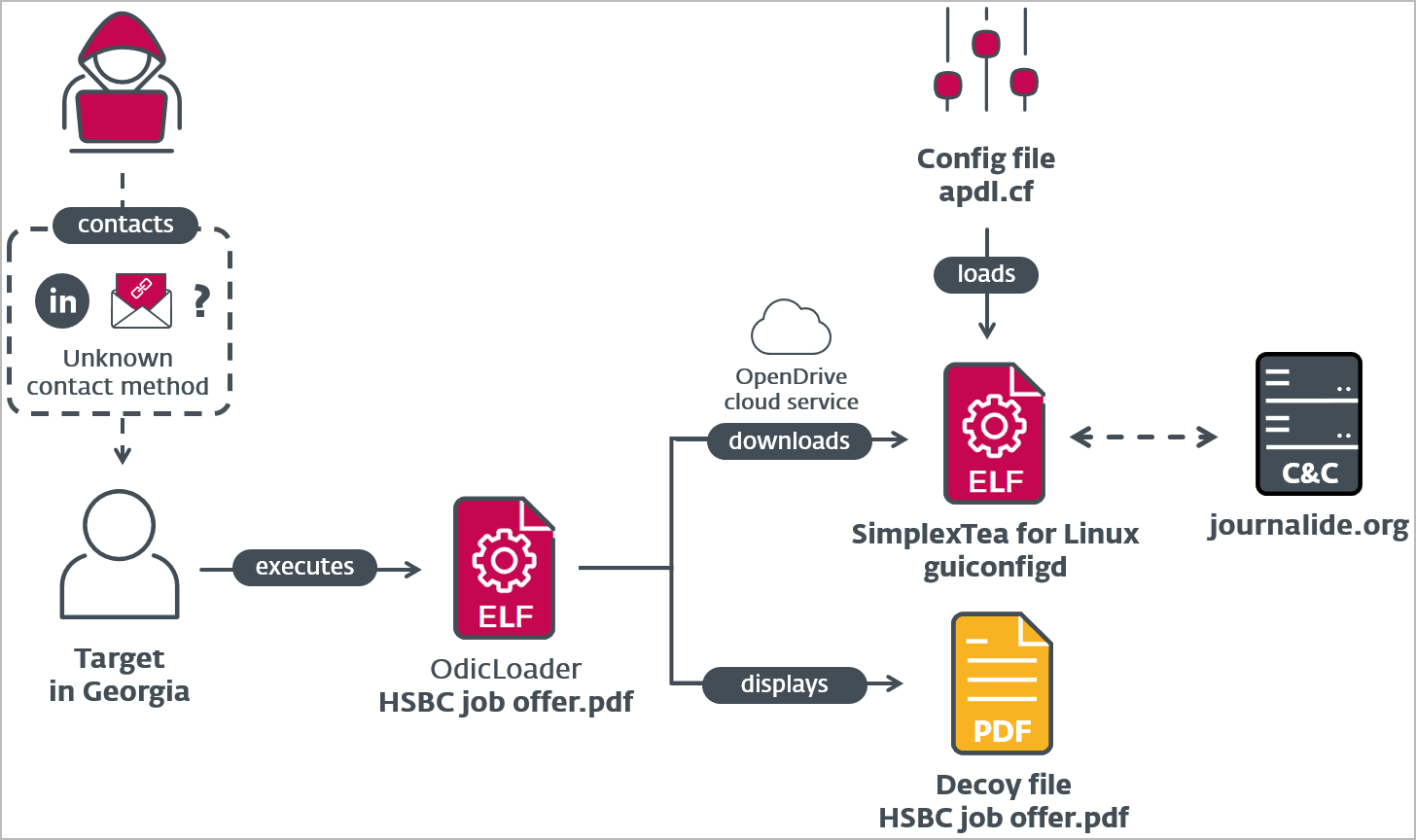
In the case discovered by ESET, Lazarus is distributing a ZIP archive named “HSBC job posting.pdf.zip” through spear phishing or direct messages on LinkedIn.
Inside the archive is a Linux binary written in Go that uses a Unicode character on its name to make it appear as a PDF.
“Interestingly, the file extension is not .pdf. This is because the apparent dot in the filename is a landmark represented by the Unicode character U+2024″, explains ESET.
“Using the leading dot in the filename was probably an attempt to trick the file manager into treating the file as an executable instead of a PDF.”
“This could cause the file to run on double-click instead of opening it with a PDF viewer.”
When the recipient double-clicks the file to launch it, the malware, called “OdicLoader”, displays a decoy PDF while simultaneously downloading a second-stage malware payload from a private repository hosted on the service. OpenDrive cloud.
The second stage payload is a C++ backdoor called “SimplexTea”, which is dropped in “~/.config/guiconfigd.SimplexTea”.
OdicLoader also modifies the user’s ~/.bash_profile to ensure that SimplexTea is launched with Bash and its output is muted each time the user starts a new shell session.
The 3CX Connection
After analyzing SimplexTea, ESET has determined that it is very similar in terms of functionality, encryption techniques and hard-coded infrastructure used with the Lazarus Windows malware named “BadCall”, as well as the macOS variant called “SimpleSea”.
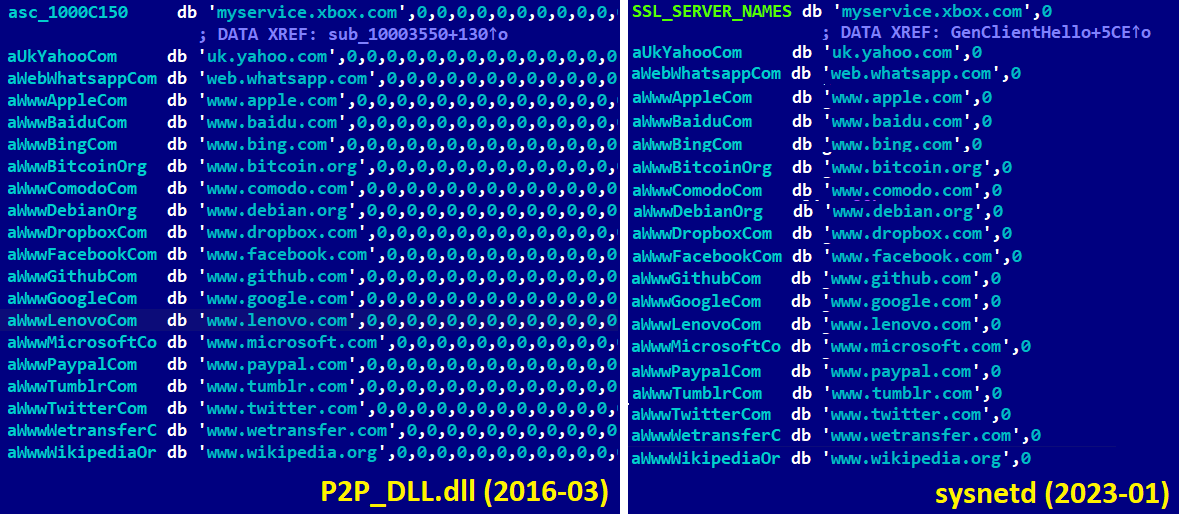
Additionally, ESET found an earlier variant of the SimplexTea malware on VirusTotal, named “sysnetd”, which is also similar to the mentioned backdoors but written in C.
This earlier variant loads its configuration from a file named /tmp/vgauthsvclog, which is used by the VMware Guest Authentication service. This suggests that the targeted system may be a Linux VMware virtual machine.
ESET analysts have also discovered that the sysnetd backdoor uses an XOR key previously discovered by the 3CX investigation to be used by the SimpleSea malware.
“By examining the three 32-bit integers, 0xC2B45678, 0x90ABCDEF, and 0xFE268455 in Figure 5, which represent a key for a custom implementation of A5/1 encryption, we realized that the same algorithm and keys were used in Windows Malware which dates back to late 2014 and was implicated in one of Lazarus’ most notorious cases: the Sony Pictures Entertainment cybersabotage,” ESET explained.
The XOR key between SimplexTea and SimpleSea payloads differs; however, the configuration file uses the same name, “apdl.cf”.
Lazarus’ move to Linux malware and the 3CX attack illustrates their ever-evolving tactics, now supporting all major operating systems, including Windows and macOS.
Similar Lazarus Operation DreamJob attacks have led to huge success for threat actors, allowing them to steal $620 million from Axie Infinity.
The FBI also confirmed that Lazarus was behind $100 million cryptocurrency theft of the bridge of harmony.
The recent Lazarus supply chain attack on 3CX marks another resounding success for the notorious cyber gang.
[ad_2]
Source link
