[ad_1]

JumpCloud, an enterprise software company based in the United States, informs several customers of an “ongoing incident”.
As a precaution, the company invalidated existing admin API keys to protect its customer organizations. The organizations involved will need to generate new keys.
Based in Louisville, Colorado and launched in 2013, the cloud-based directory-as-a-service platform serves more than 180,000 organizations in more than 160 countries.
JumpCloud invalidates API keys
This morning, BleepingComputer received a tip from an anonymous reader alerting us to a potential security incident at JumpCloud.
The drive in question is among JumpCloud customers who received an email from the company today stating that existing admin API keys have been invalidated while JumpCloud is investigating an “ongoing incident.”
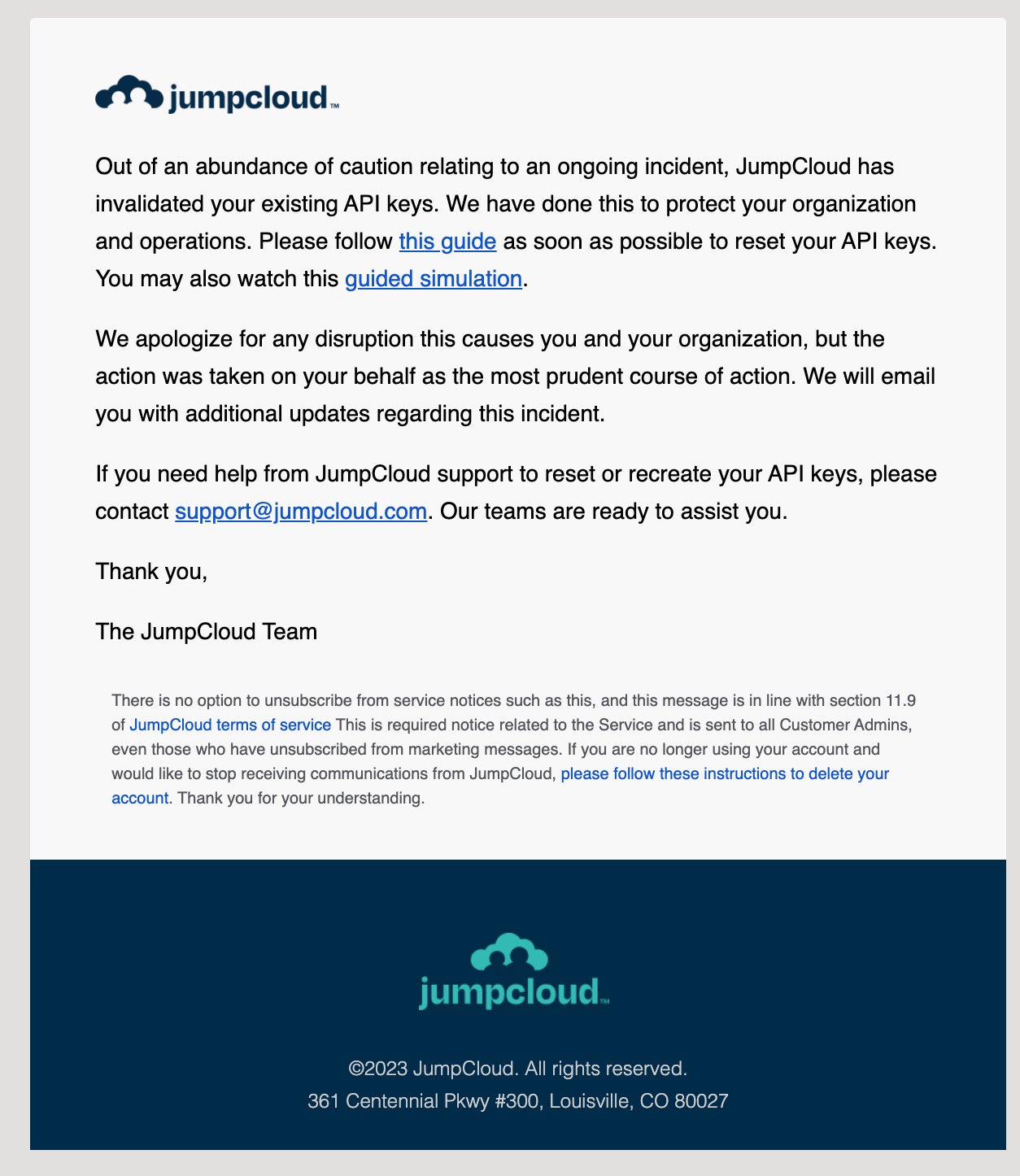
“Out of an abundance of caution regarding an ongoing incident, JumpCloud has invalidated your existing API keys. We did this to protect your organization and operations.” reads the email notification for JumpCloud administrators.
“We apologize for any disruption this causes to you and your organization, but the action has been taken on your behalf as the most prudent course of action.”
The cloud-based security service has asked affected customers, specifically admins who are “currently using their API key or an integration that relies on a JumpCloud admin API key” to generate one or more new API keys and update integrations with new API keys.
“Once an administrator’s API key is invalidated, that API key associated with that administrator will no longer work. This will impact one of the following”, States a safety notice.
Earlier this year, JumpCloud was study the potential impact to its customers following the month of January CircleCI Security Incident.
BleepingComputer contacted JumpCloud with questions related to the nature of the incident, its scope and overall impact. We await further details.
[ad_2]
Source link
