[ad_1]

US enterprise software company JumpCloud has been hacked by North Korean hackers from the Lazarus Group, according to security researchers from SentinelOne and CrowdStrike.
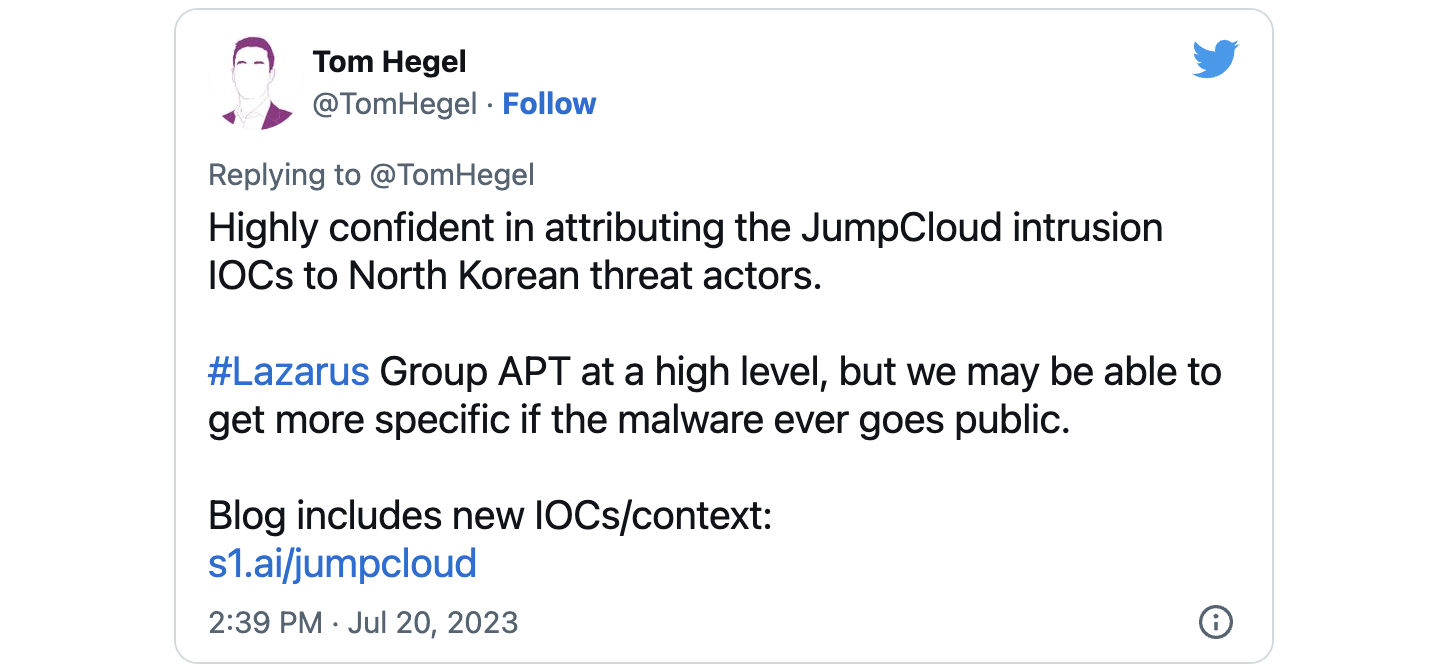
In a report released Thursday, SentinelOne senior threat researcher Tom Hegel linked North Korean threat group to JumpCloud hack based on multiple indicators of compromise shared by the company in a recent incident report.
“Reviewing recently released indicators of compromise, we associate the threat activity cluster with a North Korean state-sponsored APT,” Hegel said.
“IOCs relate to a wide variety of activities that we attribute to the DPRK, broadly centering on the supply chain targeting approach seen in previous campaigns.”
Cybersecurity firm CrowdStrike has also officially identified Labyrinth Chollima (whose business overlaps that of Lazarus Group, ZINC and Black Artemis) as the North Korean hacking team behind the breach based on evidence found while investigating the attack in conjunction with JumpCloud.
“One of their main goals has been to generate revenue for the regime. I don’t think this will be the last attack on the North Korean supply chain this year,” said Adam Meyers, CrowdStrike’s vice president for intelligence. told Reuters.
This hacking group has been active for more than a decade, since at least 2009, and is known for its attacks on high-profile targets around the world, including banks, government agencies and the media.
The FBI related Lazarus Group attackers at Axie Infinity Ronin Network Bridge Breachthe biggest cryptocurrency hack ever, which allowed them to steal a record $620 million from Ethereum.
In April, Mandiant said another North Korean threat group being tracked as UNC4736 was behind the supply chain cascade attack that hit VoIP company 3CX in March. UNC4736 is related to the Lazarus group behind Operation AppleGameswhat was connected by Google TAG to the compromise of the website of Trading Technologies, the developer of 3CX.
JumpCloud confirms hack by APT group
On June 27, JumpCloud discovered an incident where “a sophisticated nation-state-sponsored threat actor” breached its systems through a spear-phishing attack. Although there was no immediate evidence of customer impact, JumpCloud proactively rotated credentials and rebuilt the compromised infrastructure as a precaution.
During the investigation, on July 5, JumpCloud detected “unusual order activity for a small group of customers.” Working with incident response partners and law enforcement, he also analyzed logs for signs of malicious activity and forced rotation of all admin API keys.
In an opinion published on July 12, JumpCloud shared the details of the incident and published Indicators of Compromise (IOC) to help partners secure their networks against attacks from the same group.
At this time, JumpCloud has not disclosed the number of customers affected by the attack and has not assigned the APT group causing the breach to a specific state.
In January, the company also revealed that it studied the impact of one CircleCI Security Incident on its customers.
Based in Louisville, Colorado, JumpCloud operates a directory-as-a-service platform providing single and multi-factor authentication services to more than 180,000 organizations in more than 160 countries.
[ad_2]
Source link