[ad_1]

Community Health Systems (CHS) says it has been hit by a recent wave of attacks targeting a zero-day vulnerability in Fortra’s GoAnywhere MFT secure file transfer platform.
The healthcare provider giant said on Monday that Fortra had issued an alert saying it had “experienced a security incident” resulting in the compromise of some CHS data.
A subsequent investigation revealed that the resulting data breach affected the personal and health information of up to 1 million patients.
“While this investigation is still ongoing, the Company believes that the Fortra breach had no impact on any of the Company’s information systems and that there was no material disruption to business. business of the company, including the delivery of patient care,” CHS said. an 8-K filing with the SEC first spotted by DataBreaches.net.
“As for the PHI and PI compromised by the Fortra flaw, the company currently estimates that approximately one million people may have been affected by this attack.”
He also added that he would offer identity theft protection services and notify all affected individuals whose information was exposed during the breach.
CHS is a leading healthcare provider that operates 79 affiliated acute care hospitals and more than 1,000 other care sites across the United States.
The Clop gang claims to have raped 130 Fortra customers
The Clop ransomware gang claims to be behind these attacks and told BleepingComputer they hacked into and stole data from over 130 organizations.
Clop also said they allegedly stole the data for ten days after breaching GoAnywhere MFT servers that were vulnerable to exploits targeting the CVE-2023-0669 RCE bug.
The gang did not provide further evidence or details regarding their claims when BleepingComputer asked when the attacks began, if they had already started extorting victims, and what ransoms they were demanding.
BleepingComputer has not been able to independently confirm any of Clop’s claims, and Fortra has yet to respond to several emails requesting more information regarding the exploitation of CVE-2023-0669 and the ransomware group’s claims. .
However, Huntress Threat Intelligence Manager Joe Slowik also found links between GoAnywhere MFT and TA505 attacksa threat group known to have deployed Clop ransomware in the past.
Clop is known to have used a similar tactic in December 2020, when they discovered and exploited a zero-day bug in Accellion’s former File Transfer Appliance (FTA) to steal large amounts of data from approximately 100 companies worldwide.
At the time, the victims received emails demanding $10 million in ransoms to prevent their data from being published on the cybercrime group’s data leak site.
Organizations whose Accellion servers have been hacked include, among others, energy giant Shell, cybersecurity company Qualys, supermarket giant Krogerand several universities around the world such as Stanford Medicine, University of ColoradoUniversity of Miami, University of California and University of Maryland Baltimore (UMB).
If Clop follows a similar extortion strategy, we’ll likely see a rapid release of data for non-paying victims on the threat actor’s data leak site in the near future.
Federal agencies order patching until March 3
Fortra, developer of GoAnywhere MFT (formerly known as HelpSystems) disclosed to its customers last week that a new vulnerability (CVE-2023-0669) was being exploited as day zero in the wild.
The company issued emergency security updates after a proof-of-concept exploit was published onlineallowing unauthenticated attackers to obtain remote code execution on vulnerable servers.
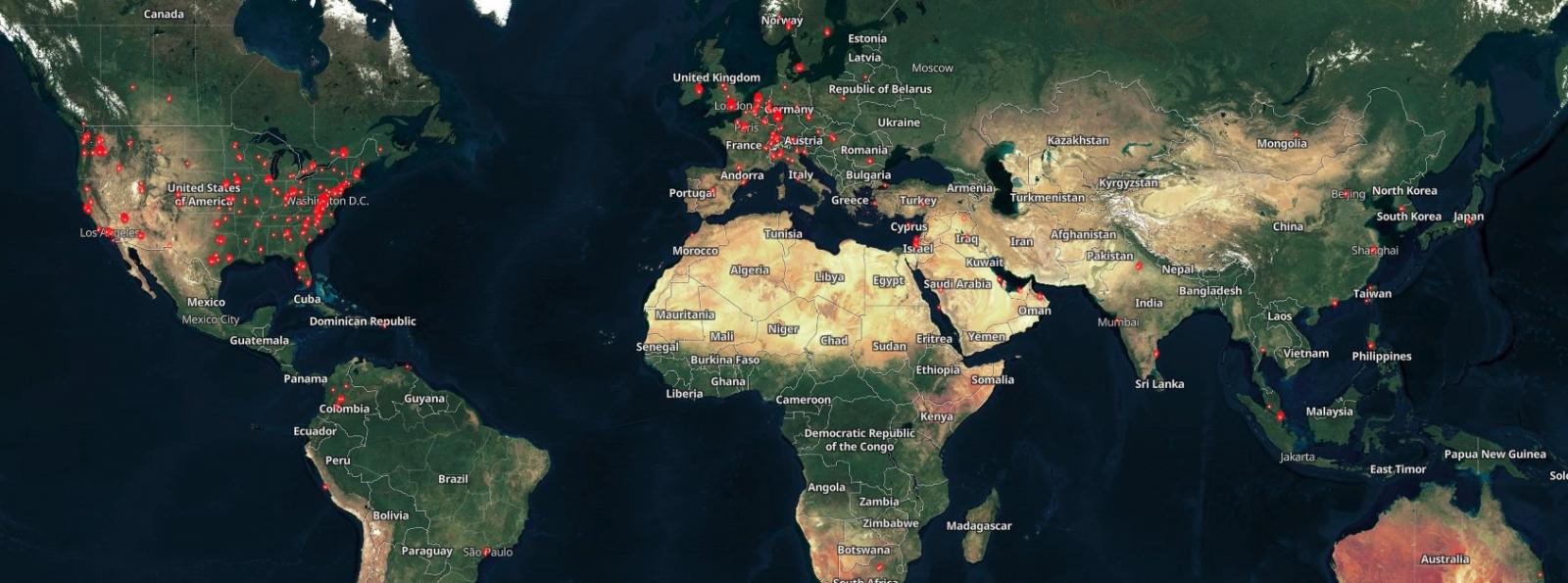
Even though Shodan currently shows that more than 1,000 GoAnywhere instances are exposed to attacks, only 136 are on ports 8000 and 8001 (those used by the vulnerable administration console).
Fortra also revealed, after releasing patches, that some of its MFTaaS hosted instances were also hacked in the attacks.
CISA added the GoAnywhere MFT flaw at its Catalog of known exploited vulnerabilities Friday, ordering US federal agencies to secure their systems within the next three weeks, through March 3.
[ad_2]
Source link
