[ad_1]
A ransomware threat called HardBit has been upgraded to version 2.0 and its operators are trying to negotiate a ransom which would be covered by the victim’s insurance company.
Specifically, the threat actor tries to convince the victim that it is in their interest to disclose all insurance details so that they can adjust their claims so that the insurer covers all costs.
Emergence of HardBit 2.0
The first version of HardBit was observed in October 2022, while version 2.0 was introduced in November 2022 and this is still the variant currently in circulation, according to a Varonis reporta data security and analytics company.
Unlike most ransomware operations, HardBit does not offer a data leak site, although its operators claim to steal victims’ data and threaten to leak it unless a ransom is paid.
As a strain of ransomware, HardBit 2.0 offers some features to reduce the victim’s safety, such as modifying the registry to disable Windows Defender’s real-time behavior monitoring, process scanning, and file protections. access.
The malware also targets 86 processes to be terminated, in order to make sensitive files available for encryption. It establishes persistence by adding itself to the “Startup” folder and deletes Volume Shadow Copies to make data recovery more difficult.
An interesting thing about the encryption phase is that instead of writing encrypted data to copies of files and deleting the originals as many stubs do, HardBit 2.0 opens files and overwrites their contents with encrypted data.
This approach makes it harder for experts to recover the original files and makes encryption slightly faster.
Ransom negotiation
Like other ransomware strains, the note that HardBit 2.0 drops on the victim’s system does not inform about the amount the hackers want in exchange for the decryption key. Victims have 48 hours to contact the attacker via an open source encrypted peer-to-peer communication messaging application.

The threat actor advises victims not to work with intermediaries, as this will only increase the total cost, but to contact them directly for negotiations.
For companies that have insurance against cyberattacks, hackers have a more elaborate set of instructions and urge them to disclose the amount of insurance for a successful dialogue.
Additionally, the hackers make it seem like sharing the insurance details is beneficial to the victim, portraying the insurer as the bad guy preventing their data from being recovered.
Threat actors say insurers never negotiate with ransomware actors with their customers’ interests in mind, so they make ridiculous counter-offers to their demands just to derail negotiations and refuse to pay.
“To avoid all of this and get the insurance money, be sure to tell us anonymously about the availability and conditions of the insurance cover, it benefits both you and us, but it does not benefit the insurance company,” HardBit operators say in a note to victims.
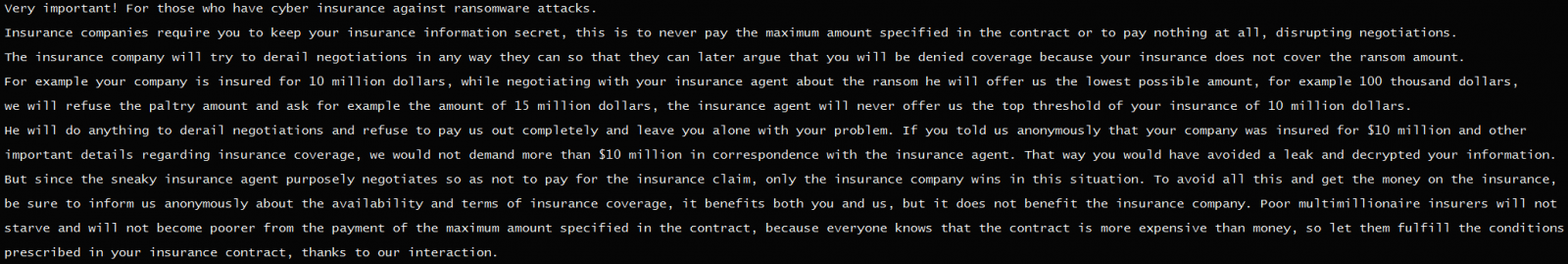
The attackers say that if they knew the exact amount of insurance, they would know exactly how much to ask for, so the insurer is obligated to cover the claim.
Of course, victims are also usually bound by contract not to disclose details of the insurance to the attackers, which risks losing the insurer’s chance to cover the damage. This is why hackers insist on these details being shared privately.
Regardless of their offer, ransomware operators’ goal is to get paid and they would say anything to get the money. The reality is that they cannot be trusted.
Refusing to pay the ransom and reporting the incident to law enforcement along with having a consistent backup strategy are the only ways to tackle and stop this type of threat.
THE Varonis report provides technical details on how HardBit 2.0 works from the initial phase and disabling security features to gaining persistence and deploying the encryption routine. The researchers also shared Indicators of Compromise (IoCs) that help identify the threat.
[ad_2]
Source link
