[ad_1]

Lending protocol Euler Finance was hit by a cryptocurrency flash loan attack on Sunday, with the threat actor stealing $197 million in multiple digital assets.
Cryptocurrency theft involved several tokensincluding $8.75 million in DAI, $18.5 million in WBTC, $33.85 million in USDC, and $135.8 million in stETH.
THE attacker‘ETH wallet used to store the stolen funds is tracked, so it will be difficult for the perpetrator to move the stolen funds and convert them into usable form.
However, Elliptical Reports that threat actors are already laundering proceeds through the sanctioned Tornado Cash cryptocurrency mixer.
The UK-based startup behind Euler Finance, Euler Labs, shared a brief statement on Twitter, saying it is currently engaging with security and law enforcement professionals and will post more information. when they are ready.
The attack caused the value of the Euler token (EUL) to drop 44.2% drop overnight, dropping from $6.56 to $3.37 at the time of writing this.
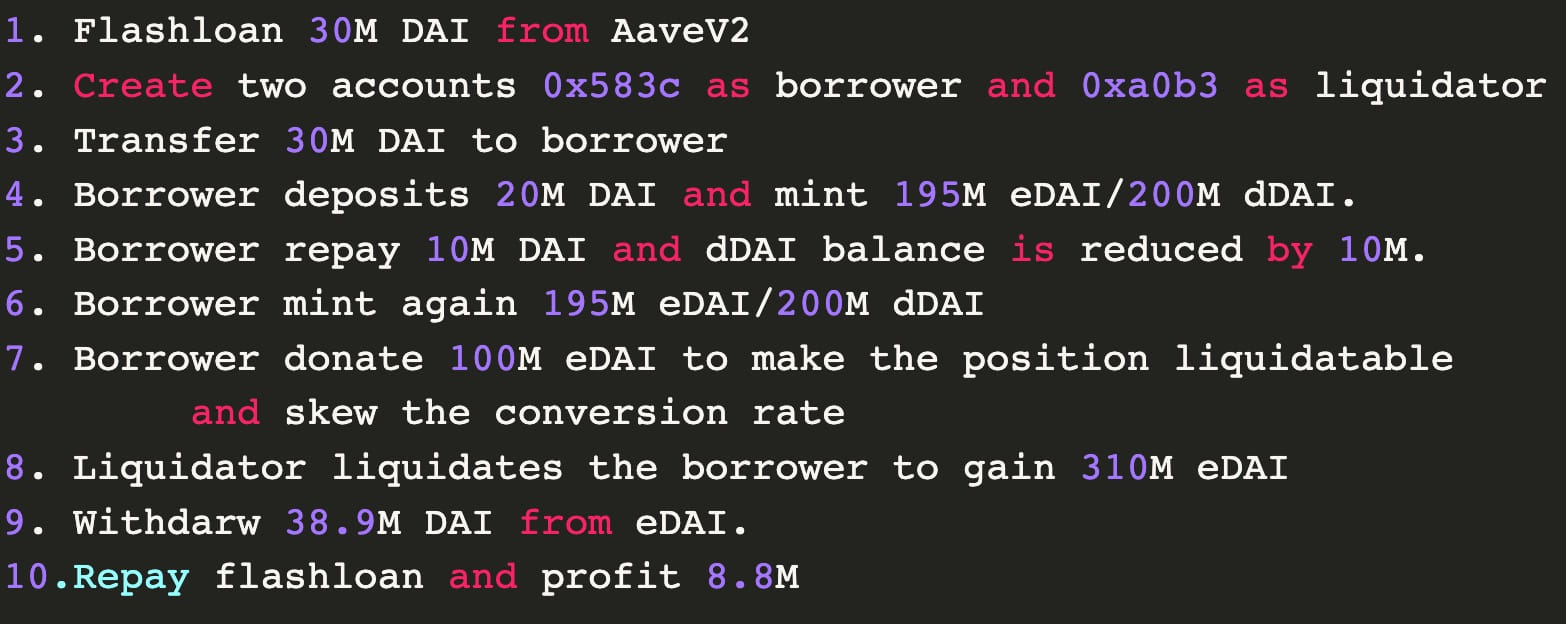
Flash lending attacks exploit a vulnerability in a lending protocol to borrow a large sum of money without having to return its value to the service.
The attackers use an exploit that allows them to manipulate the price of a token or asset on the platform for the few seconds they hold the loaned amount, so that when the transaction is complete, they end up with a huge profit.
A similar flash loan attack targeted the Beanstalk DeFi Platform in April 2022, when threat actors stole $182 million in assets.
Blockchain security and analytics company PeckShield reported that Euler’s hack was made possible due to the faulty logic of his donation and liquidation system.
Specifically, the “donateToReserves” function did not verify that the attacker was donating an over-collateralized sum, and the liquidation system did not correctly verify the conversion rate of the loan into collateral asset.
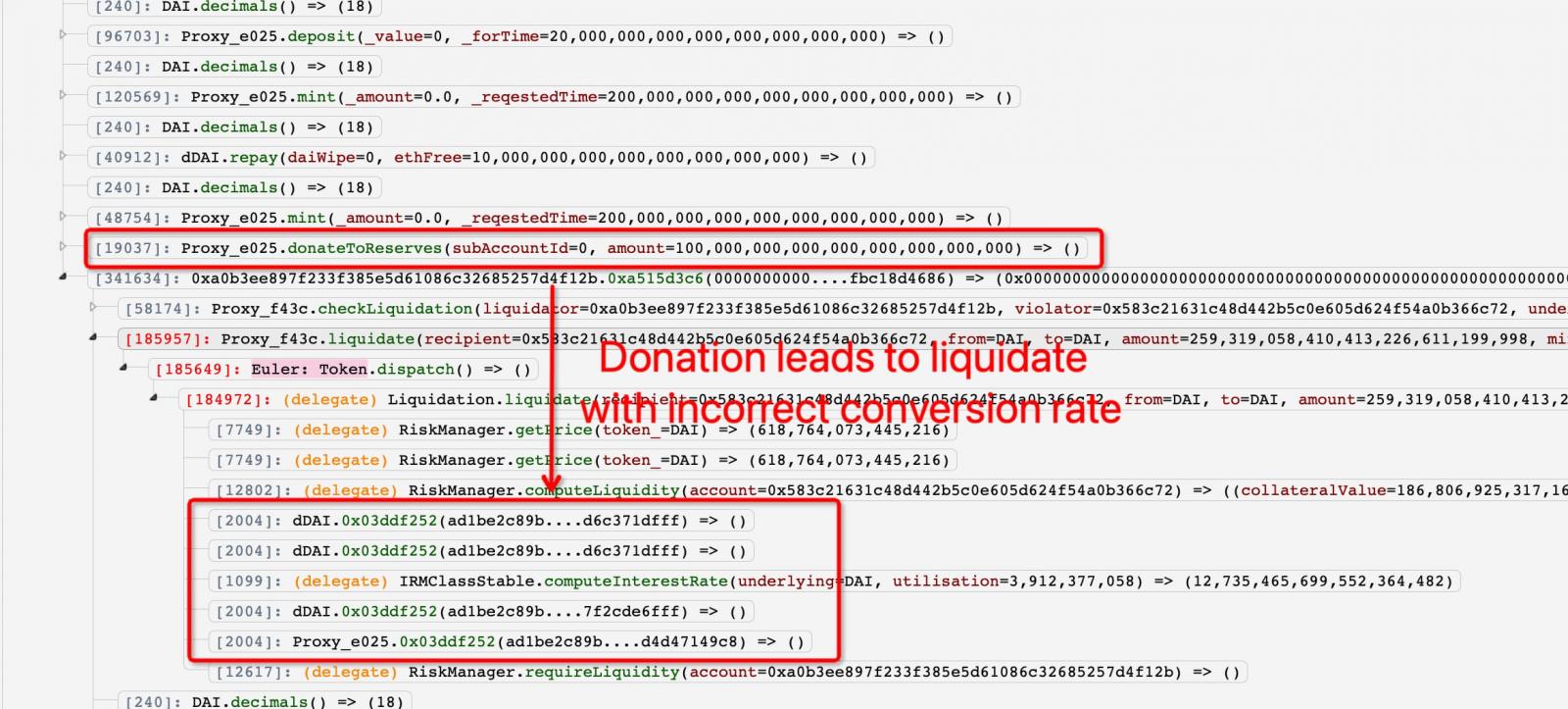
These flaws allowed attackers to manipulate the conversion rate to take advantage of the liquidation process.
PeckShield says the attack involved two hackers, a borrower and a liquidator, working in coordination to perform the required actions shown in the diagram below.
DeFi hacks have been rising over the past two years as hackers abandoned efforts to attack exchanges and focused on quickly exploiting logic flaws in the crypto lending platform’s smart contracts.
These attacks are so devastating that they can derail a healthy and successful business that has already undergone multiple security audits overnight.
[ad_2]
Source link