[ad_1]
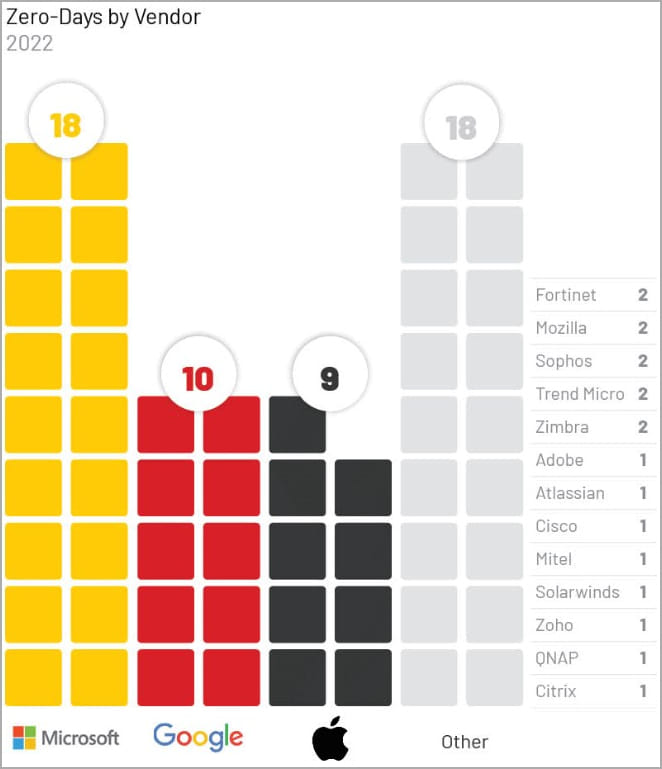
Hackers continue to target zero-day vulnerabilities in malicious campaigns, with researchers reporting 55 zero-days were actively exploited in 2022, most targeting Microsoft, Google and Apple products.
Most of these vulnerabilities (53 out of 55) allowed the attacker to gain elevated privileges or execute code remotely on vulnerable devices.
Zero-day vulnerabilities are security weaknesses in software products that are publicly disclosed or exploited before a developer knows about it or releases a patch.
They are considered extremely valuable to hackers because exploiting them is easy and stealthy as there are no specific protection or monitoring measures to track and stop attacks.
According Beggarmost of the zero-day flaws in the past year were exploited by Chinese state-sponsored actors and the most affected operating systems, web browsers and networking products.
In 2021, threat actors exploited 80 zero-day flaws in various products to perform security vulnerabilities, so last year shows a slight decline. Yet 2022 surpasses all other years when it comes to the number of actively exploited zero-day flaws.
Mandiant says 2021 has been a particularly stellar year for zero-day mining, and the cybersecurity firm expects the trend to continue upward for 2023.
However, the ongoing migration to cloud services may reduce the number of disclosed zero-day vulnerabilities, as cloud providers follow a different approach in security reporting.
Zero day landscape 2022
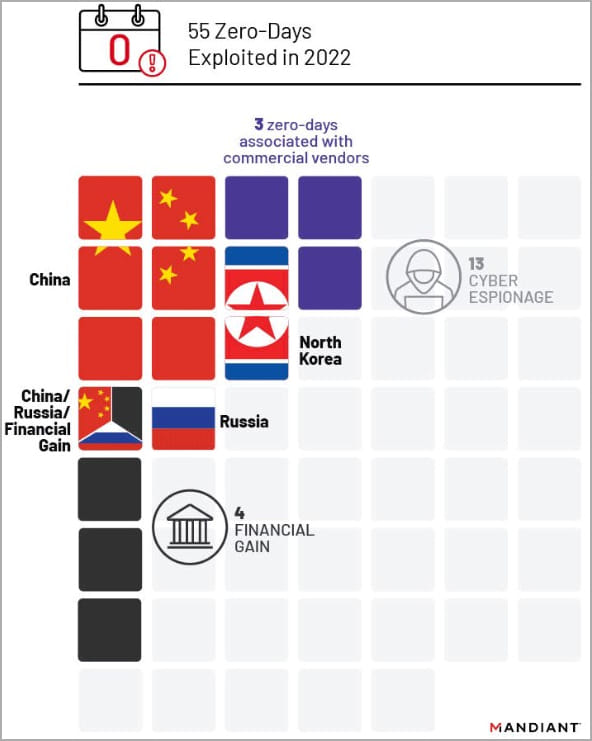
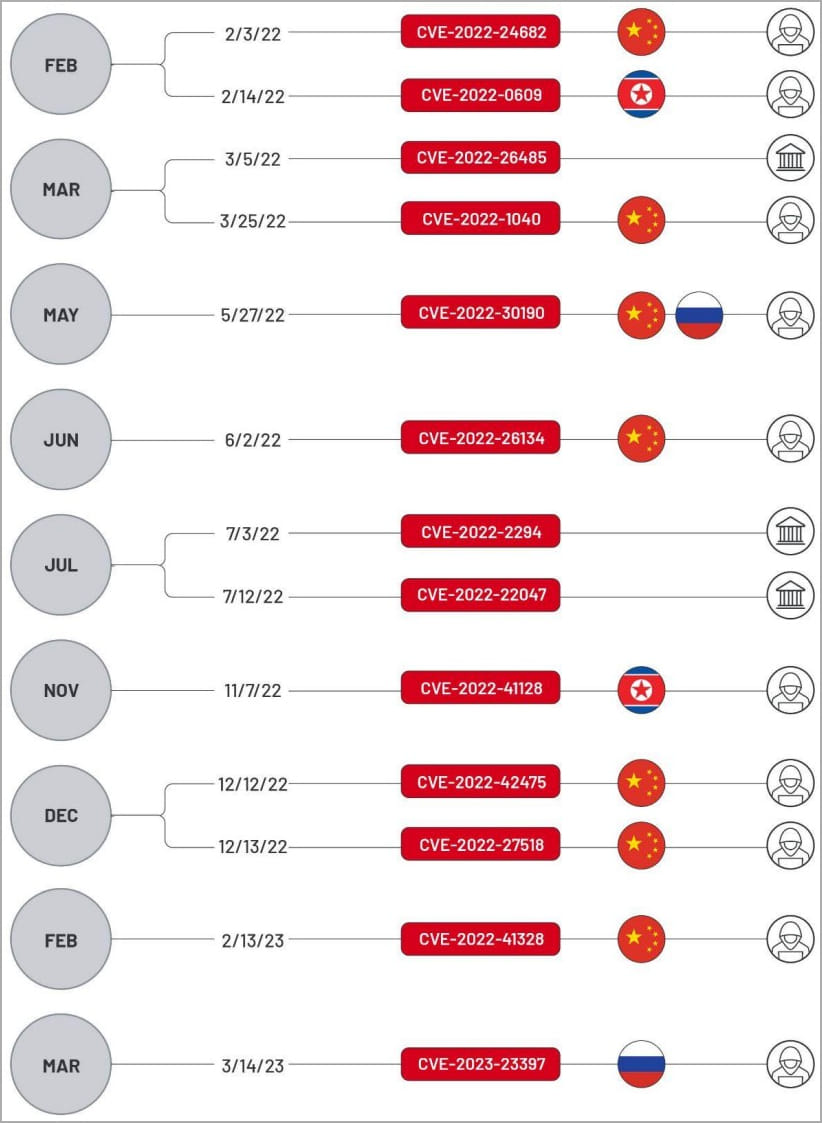
Of the 55 zero-day flaws exploited in 2022, 13 were exploited by cyber espionage groups, while Chinese cyber spies exploited 7.
Russian threat actors exploited two loopholes, with one overlapping, the North Koreans two others, while Mandiant could not determine the origin of the spy attacks in three cases.
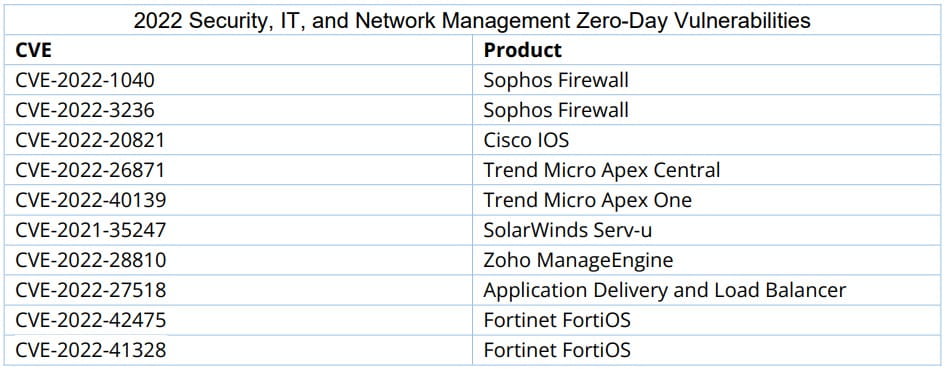
Cyber espionage groups have preferred to target “edge infrastructure” products because these typically lack detection solutions and are less likely to trigger alarms.
Additionally, exploiting them does not require interaction with the victim and can facilitate lateral movement within the compromised network.
Financially motivated threat actors are believed to be responsible for exploiting four zero-day vulnerabilities last year, three of which were attributed to ransomware actors.
Mandiant says he couldn’t deduce the exact motivation for exploiting 16 zero-day vulnerabilities.
Despite efforts by Western governments to stem the problem of commercial spyware, Mandiant reports that it continued to be a problem in 2022, with at least three zero days discovered by semi-legal malware vendors.
As for the targeted products, Windows was affected by 15 zero-day flaws in 2022, Chrome comes second with nine actively exploited vulnerabilities, iOS third with 5 zero-day flaws and macOS fourth with four zero-day issues.
Protecting systems against zero-day exploits can be difficult because there are no patches for the targeted vulnerabilities; however, organizations can still take steps to mitigate the impact of such attacks:
- Do not expose internal devices to the Internet unless necessary, and if you do, implement allowlists based on IP addresses.
- Use private tunnels or VPNs to access servers rather than exposing them to the internet.
- Apply the principle of least privilege to limit user access rights to the minimum necessary.
- Implement network segmentation to limit the spread of an attack in the event of a breach.
- Use network monitoring, firewalls, email and web filtering products, and endpoint security tools.
Administrators are also advised to subscribe to product announcements or security bulletins from their vendors to keep up to date with new updates as they are released.
[ad_2]
Source link
