[ad_1]

Hackers are actively exploiting a recently patched critical vulnerability in Control Web Panel (CWP), a server management tool formerly known as CentOS Web Panel.
The security issue is identified as CVE-2022-44877 and received a critical severity score of 9.8 out of 10 because it allows an attacker to execute code remotely without authentication.
Exploit code readily available
On January 3, the researcher Numan Turle at Gais Cyber Security, which reported the issue around October last year, released a proof-of-concept (PoC) exploit and a video showing how it works.
Three days later, security researchers noticed hackers exploiting the flaw to gain remote access to unpatched systems and to find more vulnerable machines.
CWP version 0.9.8.1147 was released on October 25, 2022 to fix CVE-2022-44877, which affects previous versions of the panel.
A technical analysis of the PoC exploit code is available from CloudSek, which performed a search for CWP servers on the Shodan platform and found over 400,000 CWP instances accessible on the Internet.
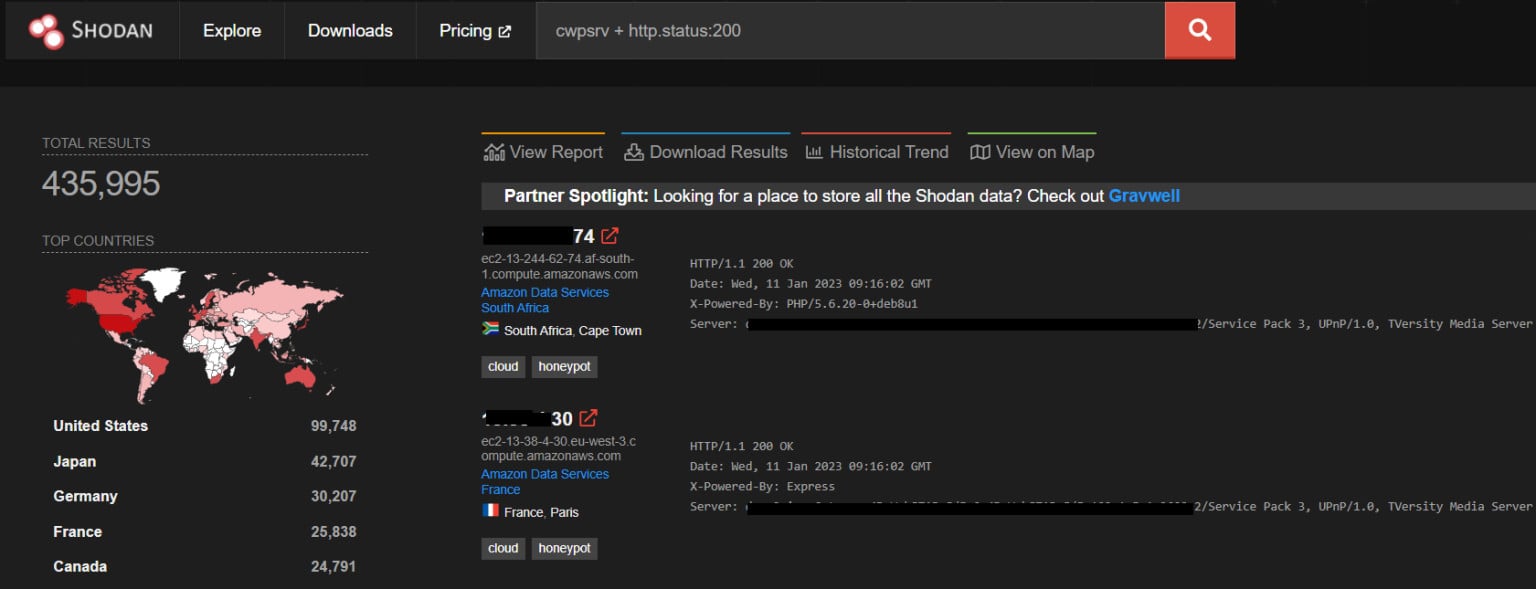
source: CloudSek
Researchers at Shadowserver Foundationwho have observed the vulnerability being exploited, note that their scans see approximately 38,000 CWP instances each day.
This figure does not represent the vulnerable machines but the population seen by the platform.
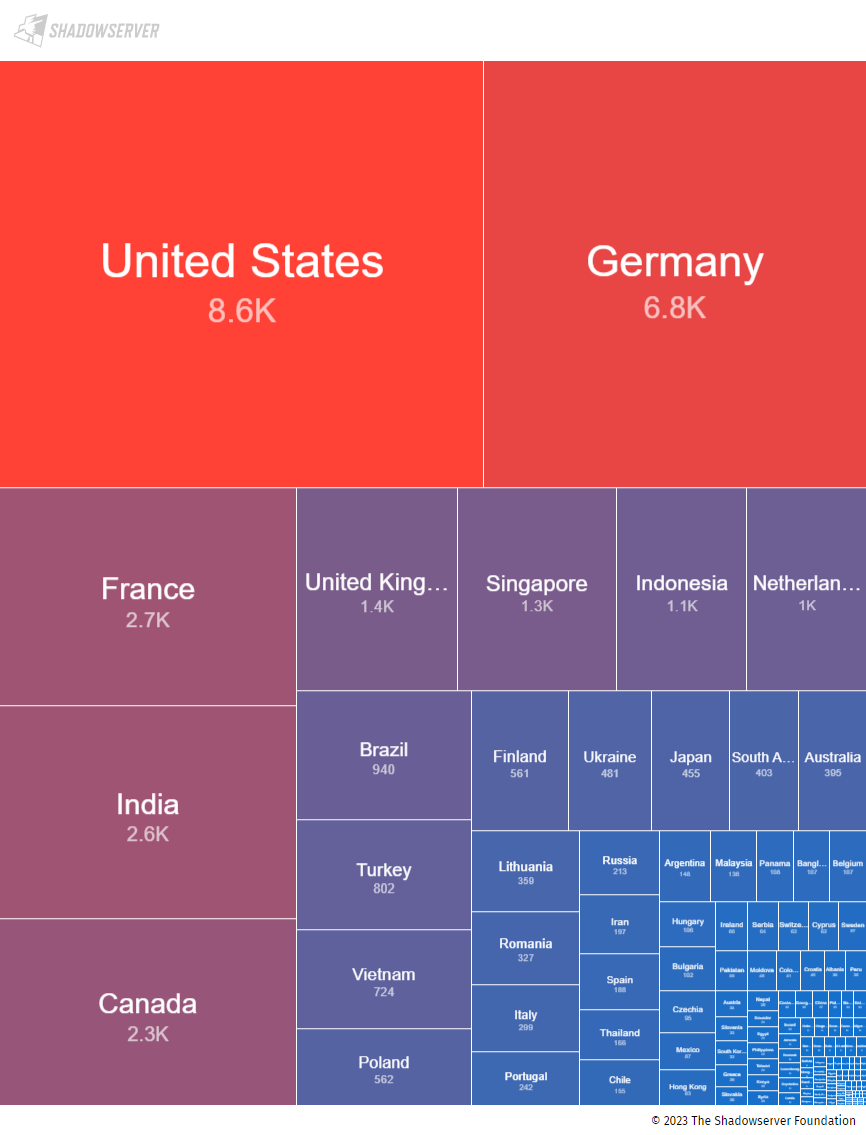
source: The Shadowserver Foundation
Malicious activity recorded by Shadowserver and shared with BleepingComputer revealed that attackers find vulnerable hosts and exploit CVE-2022-44877 to spawn a terminal to interact with the machine.
In some attacks, hackers use the exploit to start a reverse shell. The encoded payloads are converted into Python commands which invoke the attacker’s machine and generate a terminal on the vulnerable host using Python. pty Module.
Other attacks simply sought to identify vulnerable machines. It is unclear whether these scans are conducted by researchers or threat actors seeking to find rape machines at a later date.
It appears that all of these exploit attempts are based on Numan Türle’s original public PoC, slightly modified to suit the attacker’s needs.
Research company GreyNoise also observed several attacks on unpatched CWP hosts from IP addresses in the United States, Thailand, and the Netherlands.
Taking advantage of CVE-2022-44877 is easy and with the exploit code already public, all hackers have to do is find vulnerable targets, a menial task.
Admins should take immediate action and update CWP latest version availablecurrently 0.9.8.1148 released on December 1, 2022.
[ad_2]
Source link
