[ad_1]

Google released an emergency security update for the desktop version of the Chrome web browser, fixing the eighth zero-day vulnerability exploited in attacks this year.
The high-severity flaw is identified as CVE-2022-4135 and is a buffer overflow in the GPU, discovered by Clement Lecigne of Google’s Threat Analysis Group on November 22, 2022.
“Google is aware that an exploit for CVE-2022-4135 exists in the wild,” reads the update advisory.
As users need time to apply the security update to their Chrome installations, Google withheld details of the vulnerability to prevent further expansion of its malicious exploit.
“Access to bug details and links may be restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third-party library that others projects depend similarly, but have not yet been fixed.” – Google
In general, buffer overflow is a memory vulnerability that causes data to be written to forbidden (usually adjacent) locations without verification.
Attackers can use buffer overflow to overwrite an application’s memory to manipulate its execution path, resulting in unrestricted access to information or the execution of arbitrary code.
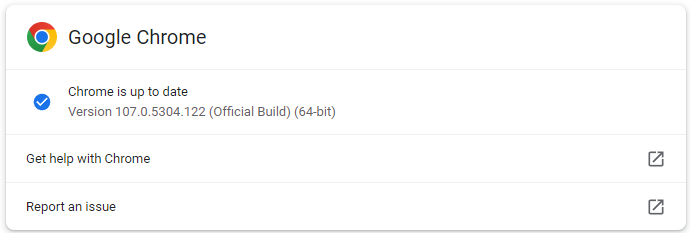
Chrome users are recommended to upgrade to version 107.0.5304.121/122 for Windows and 107.0.5304.122 for Mac and Linux, which fixes CVE-2022-4135.
To update Chrome, go to Settings → About Chrome → Wait for the latest version to finish downloading → Restart the program.
Chrome’s eighth zero-day patch in 2022
Chrome build 107.0.5304.121/122 fixes the eighth actively exploited zero-day vulnerability this year, indicating high interest from attackers against the widely used browser.
The previous seven zero-day patches are:
These flaws are usually exploited by sophisticated hackers who use them in highly targeted attacks.
Nevertheless, all Chrome users are strongly advised to update their web browsers as soon as possible in order to block possible exploit attempts.
[ad_2]
Source link
