[ad_1]

A relatively unknown Advanced Persistent Threat (APT) group named “GoldenJackal” has been targeting government and diplomatic entities in Asia since 2019 for espionage purposes.
Threat actors have maintained a low profile for stealth, carefully selecting their victims and keeping the number of attacks to a minimum to reduce the likelihood of exposure.
Kaspersky has been tracking GoldenJackal since 2020 and today reports that threat actors have had notable activity in Afghanistan, Azerbaijan, Iran, Iraq, Pakistan, and Turkey.
“GoldenJackal is an APT group, active since 2019, that typically targets government and diplomatic entities in the Middle East and South Asia,” explains Kaspersky.
“Despite the fact that they began their activities years ago, this group is generally unknown and, to our knowledge, has not been publicly described.”
The vectors of APT infection are unknown. However, researchers have observed signs of phishing operations with malicious documents that use the technique of remote pattern injection to exploit the Microsoft Office Follina Vulnerability.
Additionally, Kaspersky has witnessed a case of Trojan “Skype for Business” installers dropping a Trojan alongside a legitimate copy of the software.
While Kaspersky analysts have noticed code and TTP (techniques, tactics, and procedures) similarities with Turla, they track GoldenJackal as a separate business cluster.
Rich set of “Jackal” custom tools
According to Kaspersky, GoldenJackal uses a set of custom .NET malware tools that provide various functions including credential dumping, data theft, malware loading, lateral movement, file exfiltration , etc.
The primary payload used first to infect a system is ‘JackalControl‘, which gives attackers remote control of the infected computer.
The malware can run as a Windows program or service and can establish persistence by adding registry keys, Windows scheduled tasks, or Windows services.
It receives encrypted commands from the C2 server via HTTP POST requests, which relate to the execution of arbitrary programs, the exfiltration of files or the retrieval of additional payloads from the C2.

The second tool used by hackers is ‘JackalFly‘, a dedicated implant to exfiltrate data from all logical drives of the compromised computer, including remote shares and even newly attached USB drives.
Attackers can run the thief with arguments determining targeted file types, paths, sizes, last used files, and excluding specific paths that security tools might monitor.
All files matching the defined parameters are encrypted using AES, RSA or DES, then compressed with GZIP and finally transmitted to the C2 server.
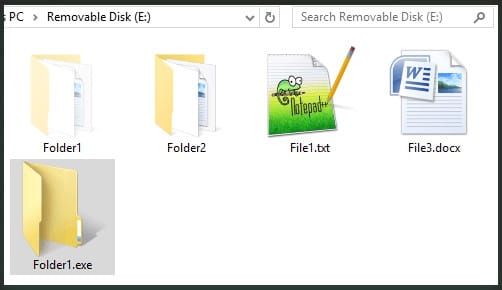
The third tool in GoldenJackal’s arsenal is ‘JackalWorm,’ which infects USB drives to spread to other potentially valuable computers.
“When the malware detects a removable USB storage device, it copies itself to it,” Kaspersky’s report reads.
“It will create a copy of itself on the root of the drive using the same directory name and change the attribute of the directory to “hidden”. This will cause the actual directory to be hidden and replaced with a copy of the malware with the name of the directory.”
To obscure its nature and trick the victim into running it, ‘JackalWorm’ uses a Windows directory icon on the removable drive.
If this happens, the worm will infect the host system, establish persistence by creating a scheduled task, and then erase its copy from the USB drive.
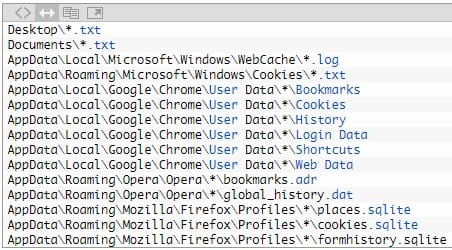
The fourth tool used by the Golden Jackal APT is ‘JacklPerInfo‘, a basic system information collector with additional capabilities to identify and exfiltrate browsing history and credentials stored in web browsers.
Serving as a typical information-stealing malware, JacklPerInfo can also exfiltrate files from Desktop, Documents, Downloads and AppData\Roaming\Microsoft\Windows\Recent directories.
The fifth and final malicious tool featured in Kaspersky’s report is ‘JackalScreenWatcher‘, which is used to take screenshots on the infected device.
Operators can specify image capture resolution and time intervals, and the tool will send media to C2 via HTTP POST requests as encrypted payloads.
In conclusion, GoldenJackal has carefully used a full set of custom tools against a limited number of victims to carry out what Kaspersky considers to be long-term espionage operations.
Although little is known about APT’s operational tactics, the diversity of observed infection chains combined with high-performance malware tools leaves no doubt that it is a threat actor. sophisticated.
[ad_2]
Source link
