[ad_1]
The malicious Glupteba botnet has returned to action, infecting devices around the world after it was shut down by Google nearly a year ago.
In December 2021, Google succeeded in causing a massive disruption to the blockchain-enabled botnet, obtaining court orders to take control of the botnet’s infrastructure and filing suits against two Russian operators.
Nozomi now reports that blockchain transactions, TLS certificate records, and reverse engineering of Glupteba samples show a new large-scale Glupteba campaign that started in June 2022 and is still ongoing.
Hide in the blockchain
Glupteba is a modular, blockchain-enabled malware that infects Windows devices to mine cryptocurrency, steal user credentials and cookies, and deploy proxies on Windows systems and IoT devices.
These proxies are then sold as “residential proxies” to other cybercriminals.
Malware is mainly distributed through malicious advertisements on pay-per-install (PUP) networks and traffic distribution systems (TDS) pushing installers disguised as freeware, videos and movies.
Glupteba uses the Bitcoin blockchain to avoid disruptions by receiving updated lists of command and control servers that it must contact for commands to be executed.
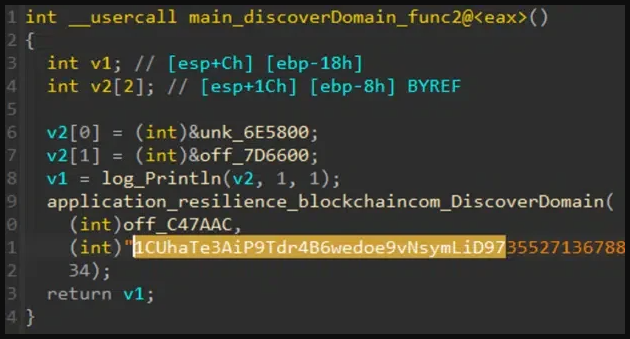
Botnet clients retrieve the C2 server address using a discovery function that enumerates Bitcoin wallet servers, retrieves their transactions, and scans them for an AES-encrypted address.
This strategy has been employed by Glupteba for several years nowproviding resilience against disassembly.
This is because blockchain transactions cannot be erased, so C2 address takedown efforts have limited impact on the botnet.
Also, without a bitcoin private key, law enforcement cannot plant payloads on the controller address, so sudden botnet takeovers or global disablements like the one that impacted Emotet in early 2021 are impossible.
The only downside is that the Bitcoin blockchain is public, so anyone can access it and review transactions to gather information.
Glupteba’s Return
Nozomi Reports that Glupteba continues to use the blockchain in the same way today, so its analysts scanned the entire blockchain to unearth hidden C2 domains.
The effort was immense, involving scrutinizing 1,500 Glupteba samples uploaded to VirusTotal to extract wallet addresses and attempt to decrypt transaction payload data using keys associated with the malware.
Finally, Nozomi used passive DNS records to find Glupteba domains and hosts and examined the latest set of TLS certificates used by the malware to uncover more information about its infrastructure.
The Nozomi investigation identified 15 Bitcoin addresses used in four Glupteba campaigns, with the most recent starting in June 2022, six months after the Google disruption. This campaign is still ongoing.
This campaign uses more Bitcoin addresses than previous operations, giving the botnet even more resilience.
.png)
Additionally, the number of hidden TOR services used as C2 servers has increased tenfold since the 2021 campaign, following a similar redundancy approach.
The most prolific address recorded 11 transactions and communicated to 1,197 samples, with its last activity recorded on November 8, 2022.
Nozomi also reports numerous Glupteba domain registrations as recently as November 22, 2022, discovered through passive DNS data.
From the above, it’s clear that the Glupteba botnet is back, and signs point to it being more massive than before and potentially even more resilient, creating a high number of fallback addresses to resist takedowns. by researchers and law enforcement.
[ad_2]
Source link
