[ad_1]
The US Department of Justice has seized 48 Internet domains and indicted six suspects for their involvement in operating “Booter” or “Stresser” platforms that allow anyone to easily carry out distributed denial of service attacks.
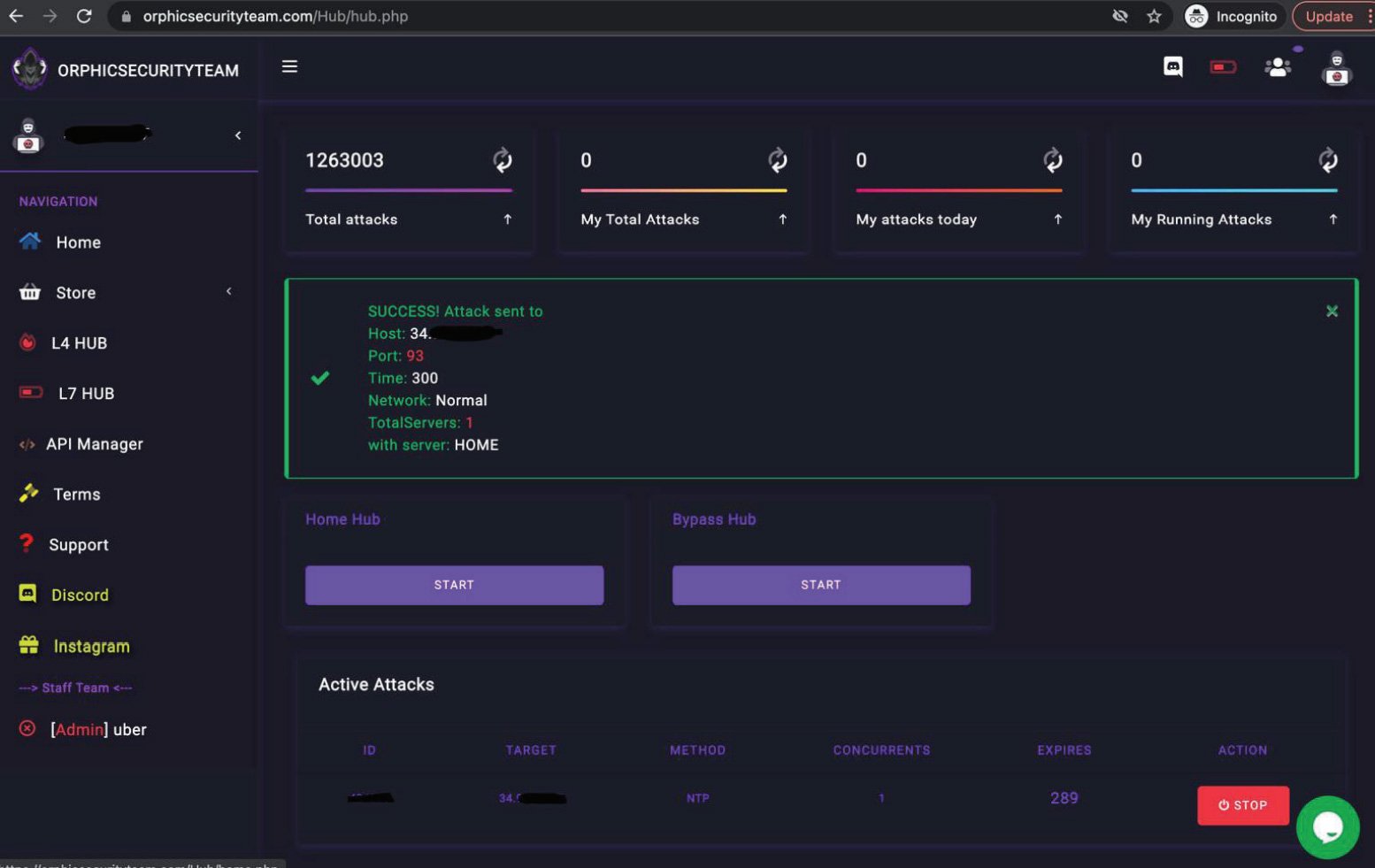
Booters are online platforms that allow hackers to pay for distributed denial of service attacks on websites and internet-connected devices. Essentially, they “boot” the target from the Internet.
Stressors offer the same DDoS functionality but claim to be provided to legitimately test the reliability of web services and the servers that support them.
“Some sites use the term ‘stressor’ in an attempt to suggest that the service could be used to test the resilience of its own infrastructure; however, as described below, I believe this is window dressing and that these services exist to conduct DDoS attacks on victims’ computers not controlled by the attacker, and without the victim’s permission,” reads a affidavit by FBI Special Agent Elliott Peterson of the Alaska Field Office.
To use these services, hackers create an account and deposit cryptocurrency, which is then used to pay for the services.
Source: FBI
While almost all booter/stresser sites require a subscriber to agree not to use the services to carry out attacks, many of these services are promoted on hacker forums and the criminal market.
In many cases, the owners of the platforms themselves promote deals and coupons on cyber crime sites or use affiliates who earn commissions for promoting the service.
Target DDoS platforms worldwide
Today, the U.S. Attorney’s Office for the Central District of California and the U.S. Attorney’s Office for the District of Alaska announced the indictment of six people for the operation of priming/stress sites.
“These startup services allow anyone to launch cyberattacks that harm individual victims and compromise everyone’s ability to access the Internet,” U.S. Attorney Martin Estrada said. “This week’s enforcement activity is a major milestone in our ongoing efforts to root out criminal behavior that threatens the infrastructure of the Internet and our ability to function in a digital world.”
The suspects include one person from Texas, three from Florida, one from New York and another from Hawaii who allegedly operated various stress/booter sites including RoyalStrasser.com, SecurityTeam.io, Astrostress.com, Booter.sx, Ipstressor .com and TrueSecurityServices.io.
As part of a more extensive operation against DDoS platformsDubbed Operation PowerOFF, the FBI and international law enforcement are seizing 48 internet (full list at the end of the article) for stress and boot rigs around the world.
Once the domains have been officially seized and transferred to the DNS used by law enforcement, they will display a seizure message warning that these services are illegal, as shown below.

Source: MJ
Thom Mrozek, director of media relations for the Central District of the U.S. Attorney’s Office in California, told BleepingComputer that the FBI is currently working with domain authorities to enforce seizure messages, but the platforms no longer work. .
The FBI is also working with the UK’s National Crime Agency and Dutch police to display search engine advertisements when people search for startup services.
For example, when searching for “startup service” on Google, the search engine showed us an ad that said, “Looking for DDoS tools? Starting is illegal”.
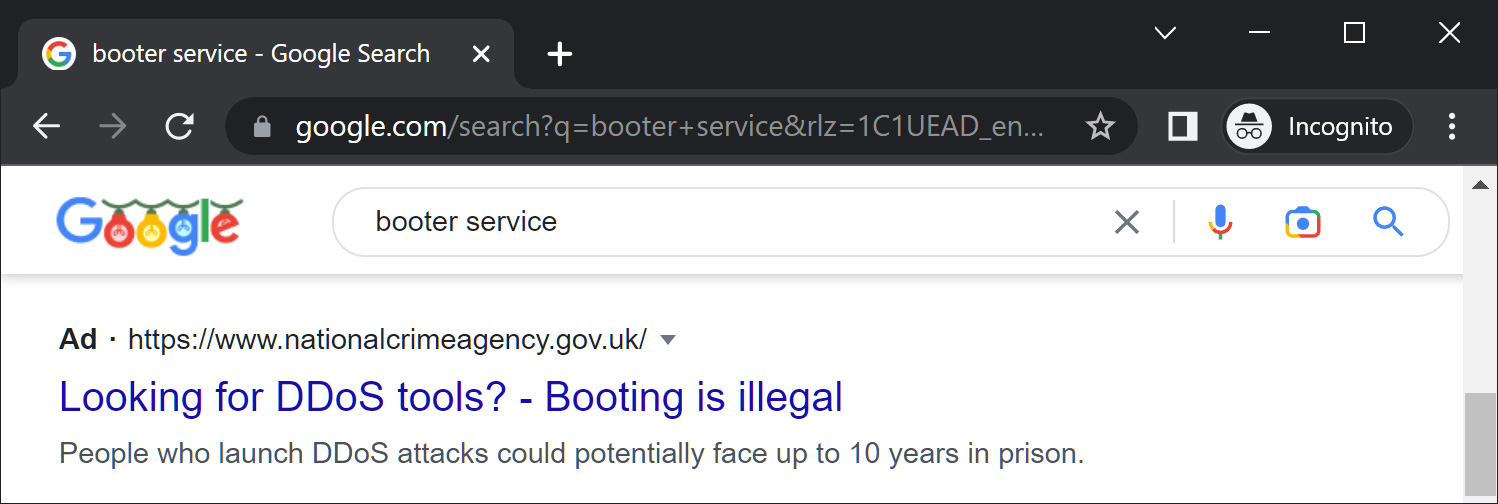
Source: BleepingComputer
British publicity leads to a Cyber-choice page offering information on how people can “make informed choices and use their cyber skills in legal ways”. A similar FBI ad leads to a webpage maintained by the Anchorage field office explaining why DDoS attacks are illegal.
The complete list of domains seized by the FBI is available below:
anonboot.com
api-sky.xyz
astrostress.com
booter.sx
booter.vip
brrsecurity.org
buuter.cc
cyberstress.us
dragonstresser.com
dreams-stresser.io
freestresser.so
instant-stresser.com
ipstress.org
ipstress.vip
ipstresser.wtf
orphicsecurityteam.com
ovhstresser.com
quantum-stresser.net
redstresser.cc
royalstresser.com
silentstress.net
stresser.app
stresser.best
stresser.gg
stresser.is
stresser.net/stresser.org
stresser.one
stresser.so
stresser.top
supremesecurityteam.com
truesecurityservices.io United States France Namecheap 1
vdos-s.co
zerostresser.com
ipstresser.xyz
kraysec.com
securityteam.io
blackstresser.net
ipstresser.com
ipstresser.us
stresser.shop
exotic-booter.com
mcstorm.io
nightmarestresser.com
shock-stresser.com
stresserai.com
sunstresser.com
bootyou.net
defconpro.net[ad_2]
Source link
