[ad_1]

Fake extortionists prey on data breaches and ransomware incidents, threatening US companies to release or sell allegedly stolen data unless they are paid.
Sometimes actors add the threat of a Distributed Denial of Service (DDoS) attack if the message recipient does not comply with the instructions in the message.
bad actors
The attackers behind this activity use the Midnight name and began targeting businesses in the United States since at least March 16.
They also impersonated some ransomware and data extortion gangs in emails and pretended to be the intruders, stealing hundreds of gigabytes of valuable data.
In an e-mail to an employee of a holding company in the petroleum additives industry, the author of the threat claimed to be the Silent ransom group (SRG) – a split from the Conti Syndicate focused on data theft and victim extortion, also known as moon moth.
The same message, however, used in the subject line the name of another threat actor, the Surtr ransomware groupfirst seen encrypting corporate networks in December 2021.

source: BleepingComputer
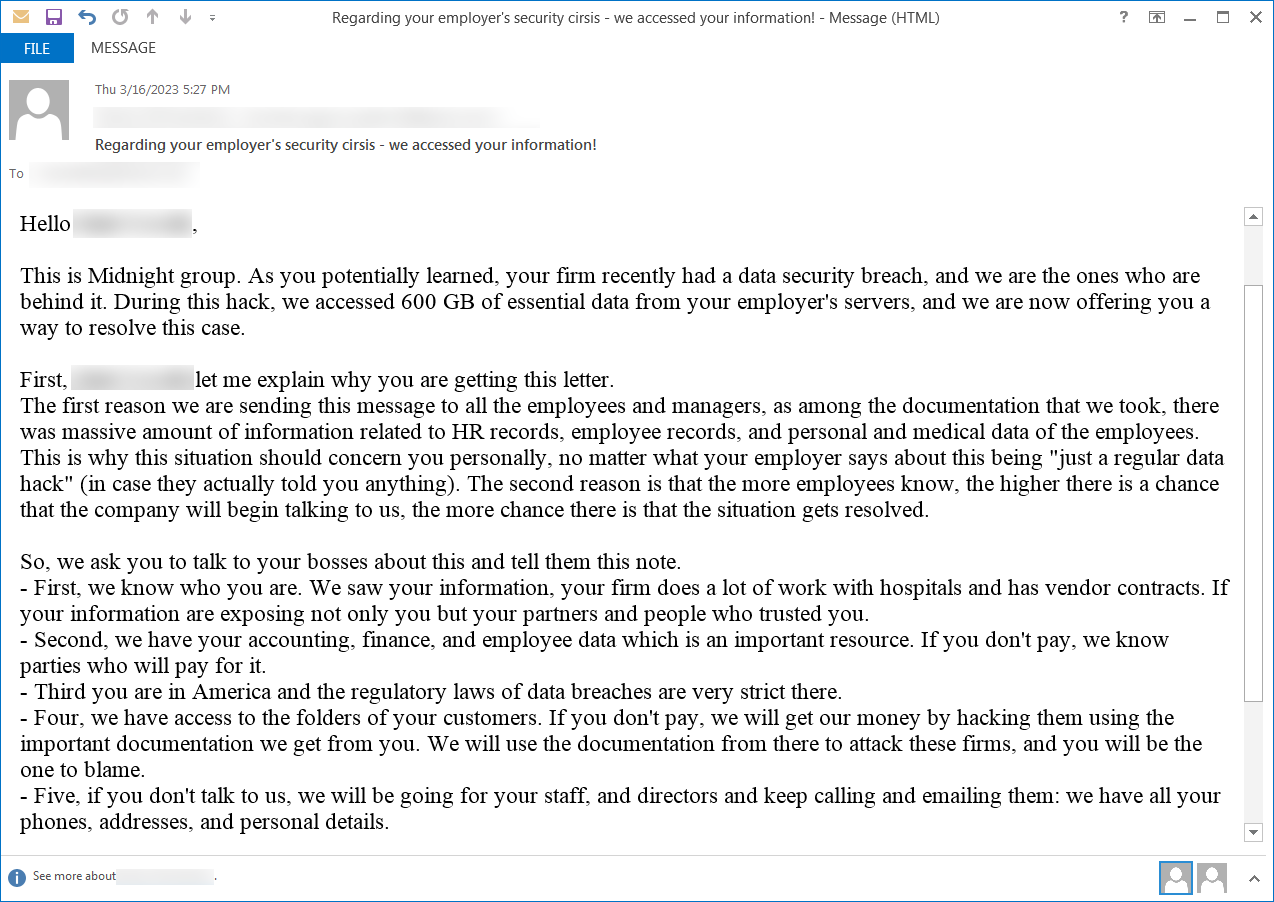
BleepingComputer found another email from Midnight Group, claiming they were the perpetrators of the data breach and had stolen 600GB of “essential data” from the servers.
The messages were sent to the address of a senior financial planner who had left the target company more than six months previously.
source: BleepingComputer
Pending DDoS threat
A report released in late March by the managed detection and response division of risk management consulting and investigation firm Kroll notes that some senders of similar emails have also been threatened with DDoS attacks.
Kroll investigators say that beginning March 23, organizations began filing an increased number of reports for emails received as the Silent Ransom Group.
It’s “a new wave of bogus extortion attempts,” Kroll’s responders say in the report, adding that the perpetrators are using the names of better-known cybercriminals in an attempt to intimidate and legitimize the threat.
“This method is cheap and easy to use by unskilled attackers. Much like 419 wirefraud scams, the scam relies on social engineering to extort victims by pressuring the victim to pay by a deadline. We expect this trend to continue indefinitely due to its profitability and ability to continue to generate revenue for cybercriminals” – Kroll
Kroll has witnessed such incidents since 2021, although this activity began in early November 2019, when non-paying victims also suffered DDoS attacks.
Nonetheless, the attacks were low-level DDoS and came with the threat of larger attacks unless the extortionists were paid.
Such incidents echo the activity of an extortion group that in 2017 sent DDoS Threats for Thousands of Businesses under the names of infamous hacker groups at the time (e.g. New World Hackers, Lizard Squad, LulzSec, Fancy Bear and Anonymous).
Target victims of ransomware attacks
Another report from incident response firm Arete confirms Kroll’s observations of fraudulent emails from Midnight Group impersonating Surtr and SRG and the highest number of messages delivered in the weeks leading up to March 24.
However, based on their visibility, responders observed that Midnight targeted organizations that had previously been victims of a ransomware attack.
According to Arete analysts, some of the initial attackers include QuantumLocker (currently rebranded as DagonLocker), Black Basta, and Luna Moth.
Fish bone says at least 15 of their current and previous clients received bogus threats from the Midnight Group, which backed up their data theft claims with vague details.
It’s unclear how the victims are selected, but one possibility comes from publicly available sources, such as the original attacker’s data leak site, social media, news reports, or company disclosures.
However, Arete notes that the fake attacker identified some ransomware victims even when the information was not publicly available, possibly indicating collaboration with the original intruders.
Ransomware actors often sell the data they steal to victims even when paid. If Midnight Group has access to marketplaces and forums where this data is traded or sold, they might learn more about ransomware victims who have not yet disclosed the cyberattack.
Void threats since 2019
The Midnight Group extortion scam is not new. The tactic was observed in 2019 by ransomware incident response firm Coveware calling it Phantom Incident Extortion.
Coveware explains that the threat actor tries to lend credibility to the threat by using data unique to the recipient’s target, adds the pressure of an expensive outcome, and demands a payment far less than the damages of public exposure .
These three components are the pillars of a Phantom Extortion Incident (PIE) and a clear indication of an empty threat.
Coveware initially provided four examples of PIE scams and only recently updated the report with an example email from the Midnight Group.
All three companies believe the threats from Midnight Group are part of a fraud campaign. Arete’s attempt to engage with the actor resulted in no response or evidence of the actor’s data being stolen.
The recommendation is to carefully analyze these emails to recognize the components of a phantom incident extortion message and dismiss them as an empty threat.
[ad_2]
Source link
