[ad_1]

Windows gamers and power users are targeted by fake MSI Afterburner download portals to infect users with cryptocurrency miners and RedLine infostealer malware.
MSI Afterburner is a GPU utility that lets you configure overclocking, create fan profiles, take video captures, and monitor the temperature and CPU usage of your installed graphics cards.
Although created by MSI, the utility can be used by users of almost any graphics card, leading to its use by millions of gamers worldwide who tweak settings to improve game performance, render their Quieter GPUs and achieve lower temperatures.
However, the tool’s popularity has also made it a good target for threat actors, who seek to target Windows users with powerful GPUs that can be hijacked for cryptocurrency mining.
Impersonate MSI Afterburner
According a new report from CybleMore than 50 websites posing as the official MSI Afterburner site have appeared online in the past three months, pushing XMR (Monero) miners with information-stealing malware.

The campaign used domains that could trick users into thinking they were visiting MSI’s legitimate website and are easier to promote using BlackSEO. Some of the domains spotted by Cyble are listed below:
- msi-afterburner–download.site
- msi-afterburner-download.site
- msi-afterburner-download.tech
- msi-afterburner-download.online
- msi-afterburner-download.store
- msi-afterburner-download.ru
- msi-afterburner.download
- mslafterburners.com
- msi-afterburnerr.com
In other cases, the domains did not resemble the MSI brand and were likely promoted through direct messages, forums, and social media posts. Examples include:
- git[.]git[.]skblxin[.]matrizauto[.]report
- git[.]git[.]git[.]skblxin[.]matrizauto[.]report
- git[.]git[.]git[.]git[.]skblxin[.]matrizauto[.]report
- git[.]git[.]git[.]git[.]git[.]skblxin[.]matrizauto[.]report
Stealth mining while stealing your passwords
When the fake MSI Afterburner installer file (MSIAfterburnerSetup.msi) is run, the legitimate Afterburner program will be installed. However, the installer will also quietly remove and run RedLine infostealer malware and an XMR miner in the compromised device.
The miner is installed via a 64-bit Python executable named ‘browser_assistant.exe’ in the local Program Files directory, which injects a shell into the process created by the installer.
This shellcode fetches the XMR miner from a GitHub repository and injects it directly into memory in the explorer.exe process. Since the miner never touches the disk, the chances of being detected by security products are minimized.
The miner logs into their mining pool using a hard-coded username and password, then collects and exfiltrates basic system data to threat actors.
One of the arguments used by the XMR miner is the “CPU max threads” set to 20, exceeding most modern CPU thread counts, so it is set to capture all available power.
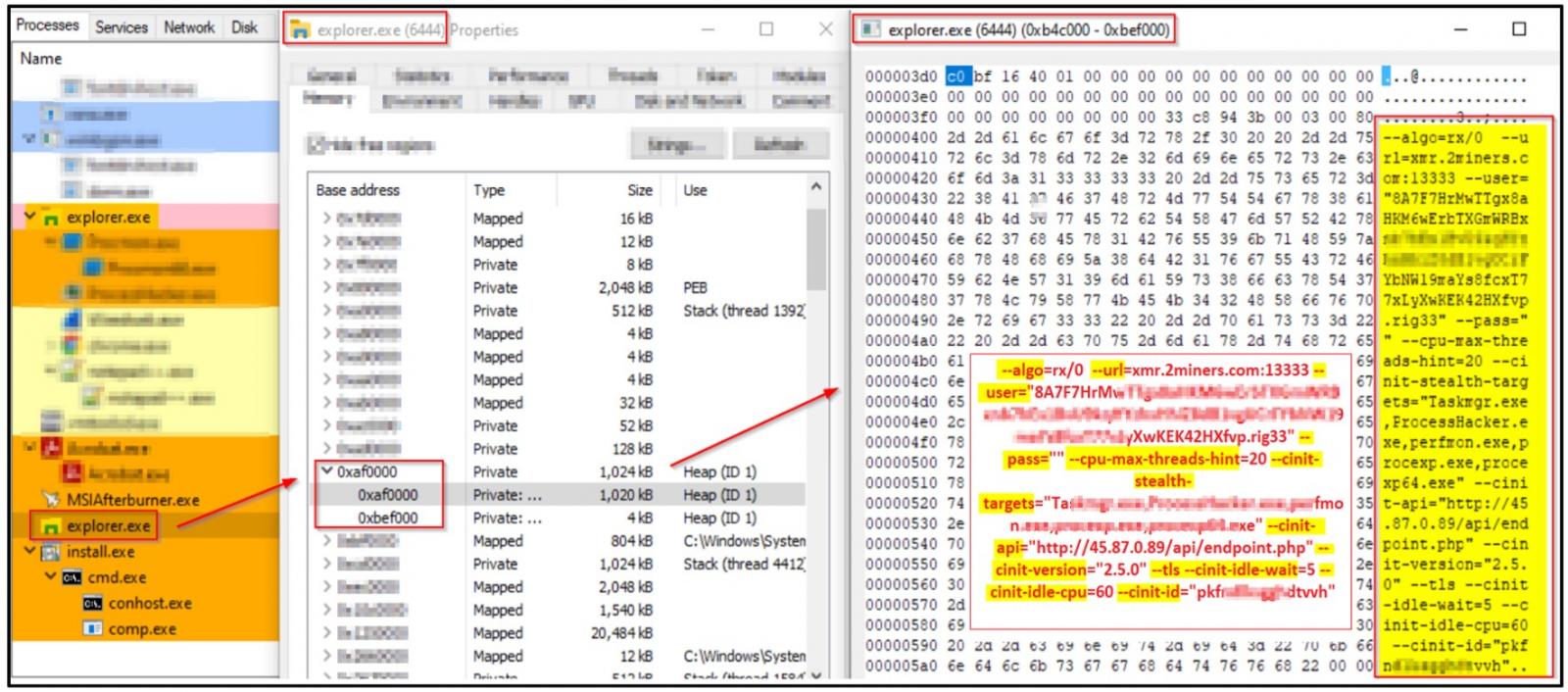
The miner is only set to mine after 60 minutes since the CPU went to sleep, which means the infected computer is not performing any resource-intensive tasks and is most likely left unattended.
Also, it uses the “-cinit-stealth-targets” argument, which is an option to suspend mining activity and clear GPU memory when specific programs listed under “stealth targets” are launched.
These can be process monitors, antivirus tools, hardware resource viewers and other tools that help the victim to spot the malicious process.
In this case, the Windows applications from which the miner tries to hide are Taskmgr.exe, ProcessHacker.exe, perfmon.exe, procexp.exe and procexp64.exe.
While the miner quietly hijacks your computer’s resources to mine Monero, RedLine has already operated in the background to steal your passwords, cookies, browser information, and potentially all cryptocurrency wallets.
Unfortunately, almost all components of this fake MSI Afterburner campaign have poor antivirus software detection.
VirusTotal reports that the malware ‘MSIAfterburnerSetup.msi’ The installation file is only detected by three out of 56 security products, while the ‘browser_assistant.exe‘ is only detected by 2 out of 67 products.
To stay safe from miners and malware, download tools directly from official sites rather than sites shared in forums, social media or direct messages.
In this case, the legitimate MSI Afterburner can be downloaded directly from MSI at www.msi.com/Landing/afterburner/graphics-cards.
[ad_2]
Source link
