[ad_1]

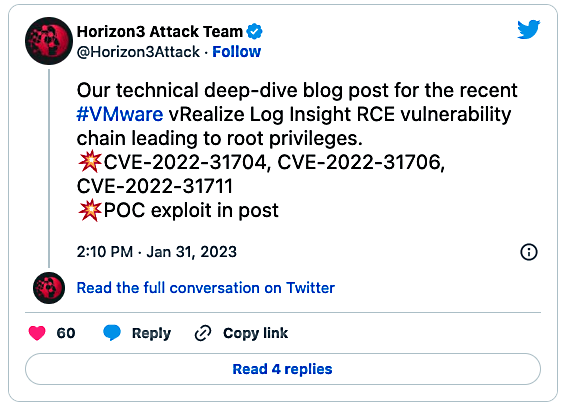
Horizon3 security researchers have released proof-of-concept (PoC) code for a VMware vRealize Log Insight vulnerability chain that allows attackers to achieve remote code execution on unpatched appliances.
vmware fixed four security vulnerabilities in its vRealize log analysis tool last week, two of which were critical and allowed remote attackers to execute code on compromised devices.
Both are labeled as critical gravity with CVSS Base Scores of 9.8/10 and can be exploited in low-complexity attacks that do not require user interaction.
The first (CVE-2022-31706) is a directory traversal bug, and the second (CVE-2022-31704) is a broken access control flaw. They can be misused to inject maliciously crafted files into the operating system of affected devices.
VMware also patched a deserialization vulnerability (CVE-2022-31710) that triggers denial of service states and an information disclosure bug (CVE-2022-31711) that attackers can use to gain access to sensitive information on sessions and applications.
Horizon3 published a blog post on Friday containing additional information on how three of them could be chained by malicious attackers to execute code remotely as root on compromised VMware vRealize appliances.
The researchers also released a list of Indicators of Compromise (IOCs) that network defenders could use to detect exploitation within their networks after warning one day early that they are going to release that targets this bug chain.
Earlier today, Horizon3 published the PoC exploit and Explain that the RCE exploit “abuses the various Thrift RPC endpoints to achieve an arbitrary file write”.
“This vulnerability is easy to exploit, however, it requires the attacker to have infrastructure configured to serve the malicious payloads,” the researchers said.
“Additionally, since this product is unlikely to be exposed to the Internet, the attacker likely has already established a foothold elsewhere on the network. This vulnerability allows remote code execution as root, essentially giving an attacker complete control over the system.”
While there are only a few dozen instances publicly exposed on the internet, according to data from Shodan, that’s to be expected given that VMware vRealize Log Insight appliances are designed to be accessed from inside the network of an organization.
However, it is not uncommon for attackers to exploit vulnerabilities in already compromised networks for lateral movement, making vulnerable VMware appliances valuable internal targets.
Although there are no public reports of attacks using this exploit chain and no attempt to exploit it in the wildresourceful and motivated hackers will likely quickly adopt Horizon3’s RCE exploit or create their own custom versions.
Last year, Horizon3 researchers also released an exploit to CVE-2022-22972a critical authentication bypass security flaw affecting multiple VMware products that allowed a malicious actor to gain administrator privileges on unpatched instances.
[ad_2]
Source link