[ad_1]

A new malware toolkit targeting businesses called “Decoy Dog” has been discovered after inspecting anomalous DNS traffic that stands out from normal internet activity.
Decoy Dog helps threat actors evade standard detection methods through strategic domain aging and DNS query dribbling, with the goal of establishing a good reputation with security vendors before moving on to facilitating operations of cybercrime.
Infoblox researchers discovered the toolkit in early April 2023 as part of its daily scan of more than 70 billion DNS records to look for signs of abnormal or suspicious activity.
Infoblox reports that Decoy Dog’s DNS fingerprint is extremely rare and unique among the 370 million active domains on the Internet, making it easy to identify and track.
Thus, the investigation of the Decoy Dog infrastructure quickly led to the discovery of several C2 (command and control) domains linked to the same operation, with most of the communications for these servers originating from hosts in Russia.
Further investigation revealed that the DNS tunnels on these domains had characteristics that pointed to Pupy RAT, a remote access Trojan deployed by the Decoy Dog Toolkit.
Pupy RAT is a modular open-source post-exploitation toolkit popular among state-sponsored threat actors to be stealthy (fileless), support encrypted C2 communications, and help them merge their activities with other threat actors. other users of the tool.
THE Pupy RAT Project supports payloads in all major operating systems including Windows, macOS, Linux, and Android. Like other RATs, it allows threat actors to execute commands remotely, elevate privileges, steal credentials, and spread laterally across a network.
Less skilled actors do not use Pupy RAT because deploying the tool with the correct DNS server configuration for C2 communications requires knowledge and expertise.
“This multi-part (DNS) signature gave us great confidence that the (correlated) domains were not just using Pupy, but were all part of Decoy Dog – a single large toolkit that deployed Pupy in a very specific way on enterprise or large organizational, non-consumer devices,” Infoblox revealed in his report.
Additionally, analysts discovered distinct DNS tagging behavior on all Decoy Dog domains that are configured to follow a particular pattern of generating periodic but infrequent DNS queries.
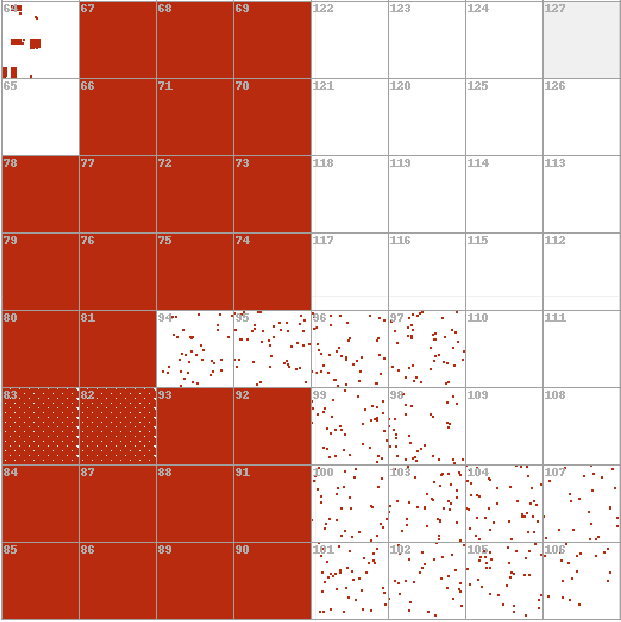
Investigations of hosting and domain registration details revealed that Operation Decoy Dog had been ongoing since early April 2022, so it remained under the radar for over a year despite box domains tools showing extreme outliers in analyses.
.png)
Decoy Dog’s discovery demonstrates the power of using large-scale data analytics to detect anomalous activity across the vastness of the Internet.
“Infoblox has listed Decoy Dog domains in its report and added them to its list of ‘suspicious domains’ to help defenders, security analysts, and targeted organizations protect against this sophisticated threat,” researchers explain. ‘InfoBlox.
“The discovery of Decoy Dog, and more importantly, the fact that several seemingly unrelated domains used the same rare toolkit was the result of this combination of automatic and human processes.”
Because the situation is complex and we have focused on the DNS aspects of discovery, we expect more details to come from the industry, in addition to ourselves, in the future.”
The company also shared indicators of compromise on its audience GitHub repositorywhich can be used for manual addition into blocklists.
[ad_2]
Source link
