[ad_1]
Hypervolume DDoS (distributed denial of service) attacks in Q1 2023 shifted from using compromised IoT devices to exploiting hacked virtual private servers (VPS).
According to internet security firm Cloudflare, the new generation of botnets have gradually moved away from the tactic of creating large swarms of individually weak IoT devices and are now turning their attention to enslaving vulnerable and misconfigured VPS servers using leaked API credentials or known exploits.
This approach helps threat actors create high-performance botnets more easily and often faster, which can be up to 5,000 times more powerful than IoT-based botnets.
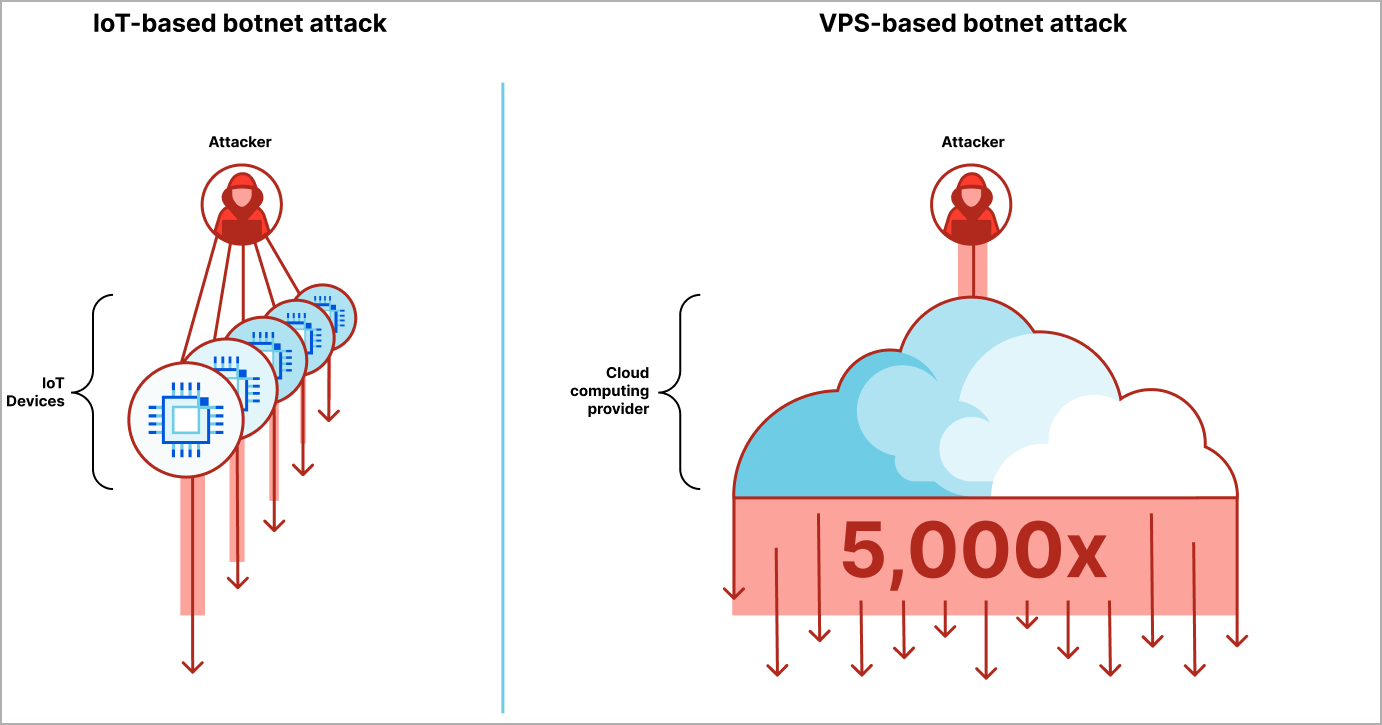
“The next generation of botnets use a fraction of the number of devices, but each device is considerably more powerful,” explains Cloudflare in The report.
“Cloud providers offer virtual private servers to allow start-ups and enterprises to build high-performance applications. The downside is that it also allows attackers to create high-performance botnets that can be up to 5,000 times more powerful.”
Cloudflare has worked with major cloud computing providers and partners to crack down on these emerging VPS-based threats and claims to have successfully removed substantial portions of these new botnets.
Q1 2023 DDoS Landscape
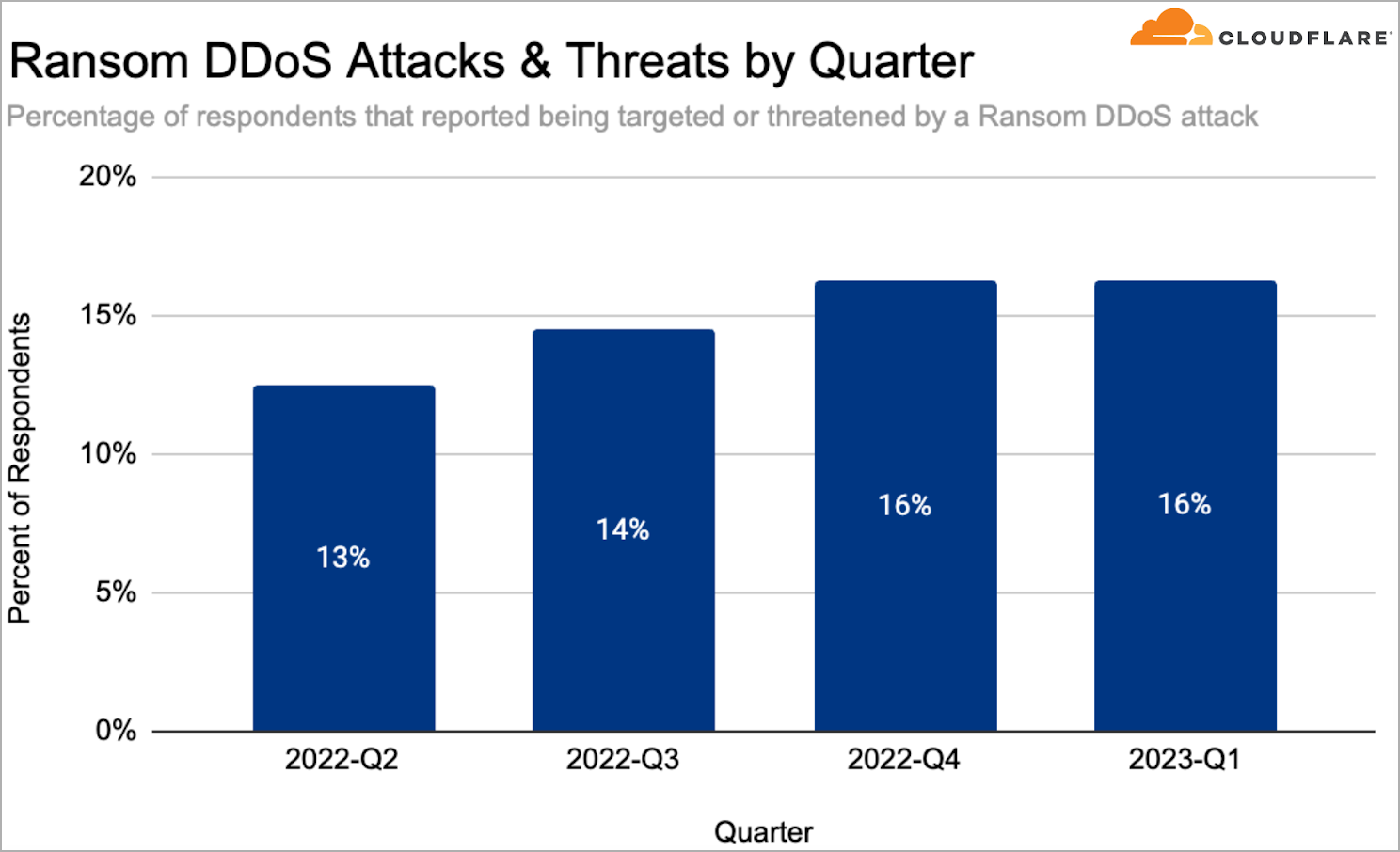
In general, Cloudflare reports stable DDoS activity in the first quarter of the year, with a notable 60% year-over-year increase in ransom DDoS attacks, representing 16% of all recorded DDoS attacks/ reported.
These extortion-based DDoS attacks cause outages to the target by bombarding it with garbage traffic and continue indefinitely until the victim responds to the attacker’s demands.
The country most targeted by DDoS attacks in general during Q1 23 was Israel, followed by the United States, Canada and Turkey. Internet services, marketing, software and games/games were the most targeted sectors.
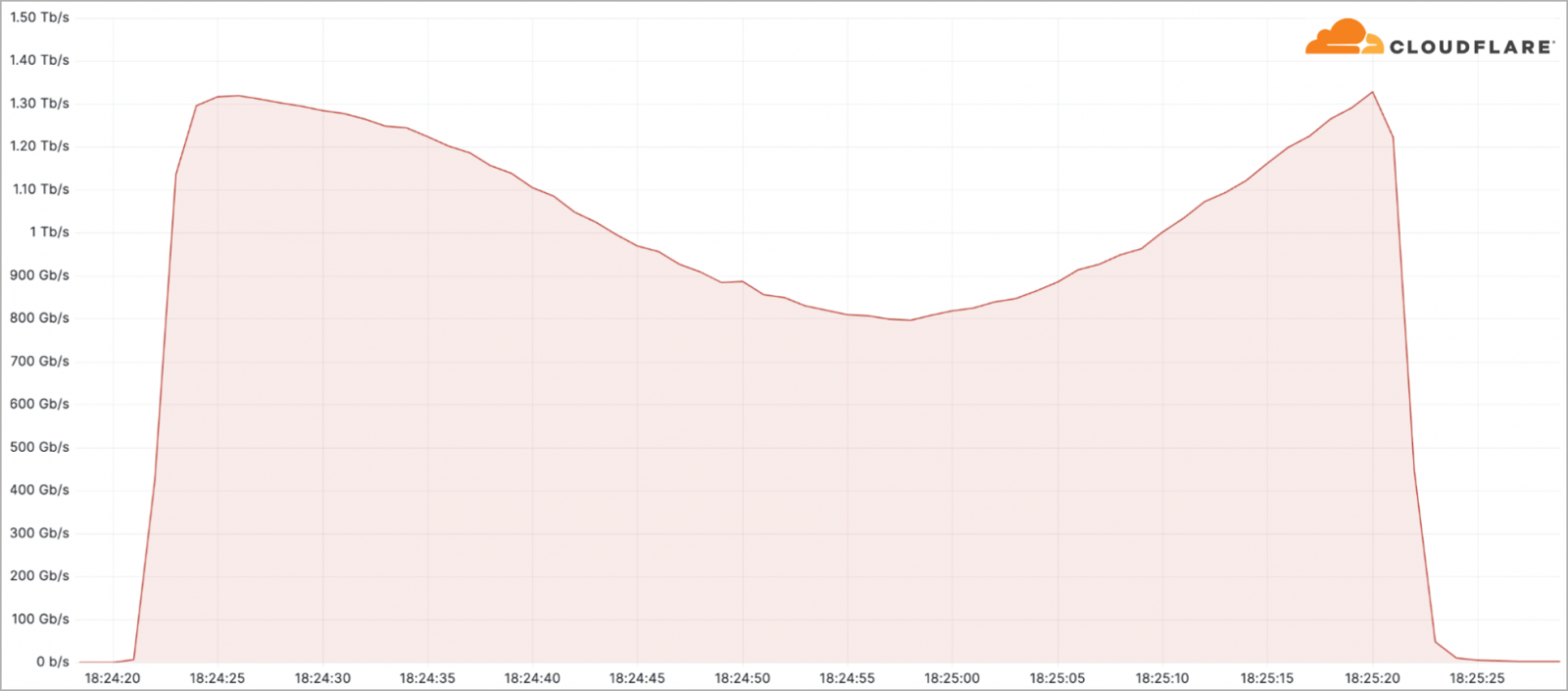
The largest attack seen by Cloudflare this quarter peaked at over 71 million requests per second. Another notable incident was a 1.3 terabit per second DDoS attack targeting a telecommunications service provider in South America.
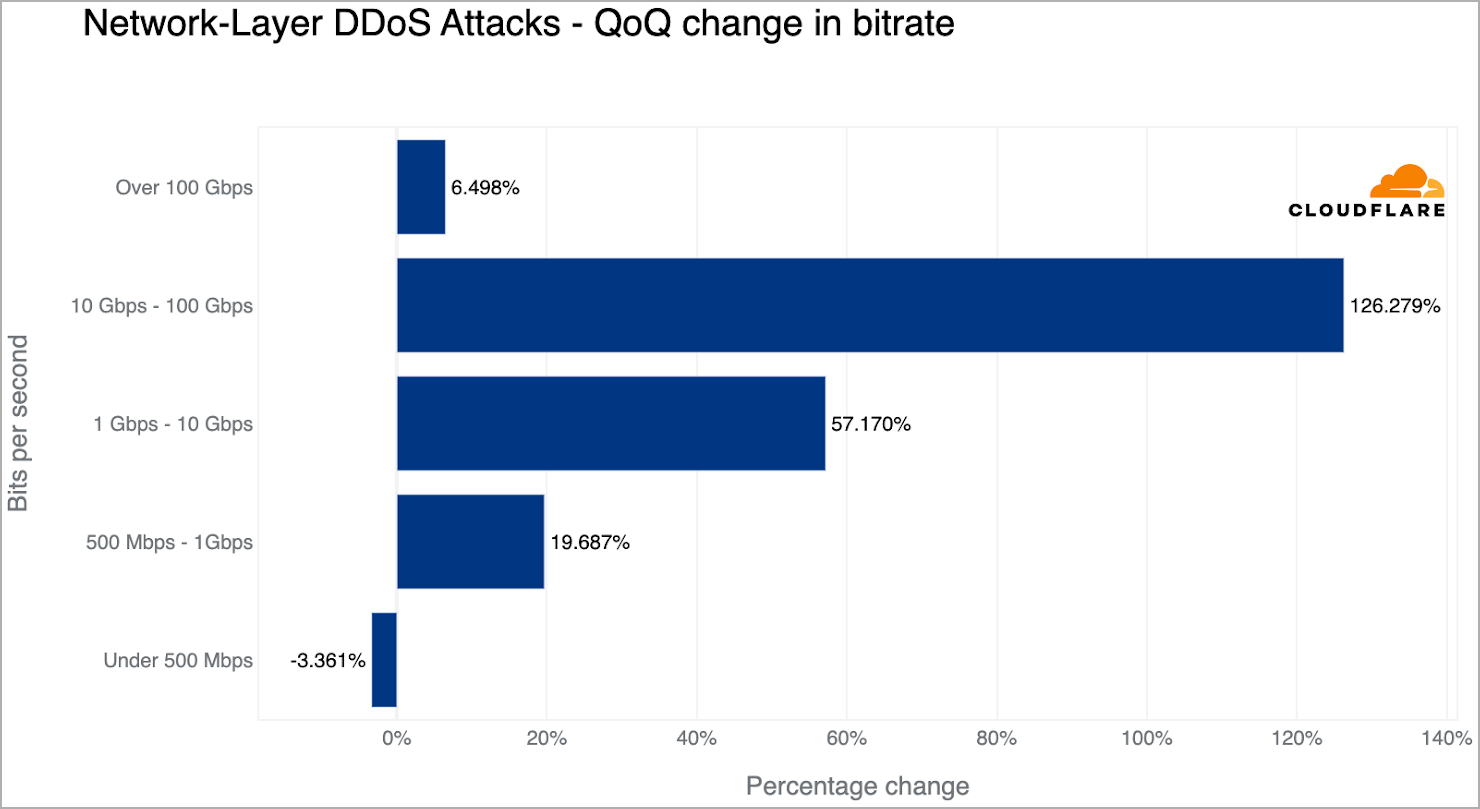
In terms of attack size and duration, most (86.6%) lasted less than 10 minutes, while 91% did not exceed 500 Mbps.
However, the number of larger attacks continues to grow, with attacks over 100 Gbps up approximately 6.5% from the prior quarter.
Emerging trends
DDoS attacks can manifest in many ways, and as defenses evolve to deal with them, attackers may devise new methods or revert to old tactics that new protection systems no longer prioritize.
During this quarter, Cloudflare recorded the following emerging trends:
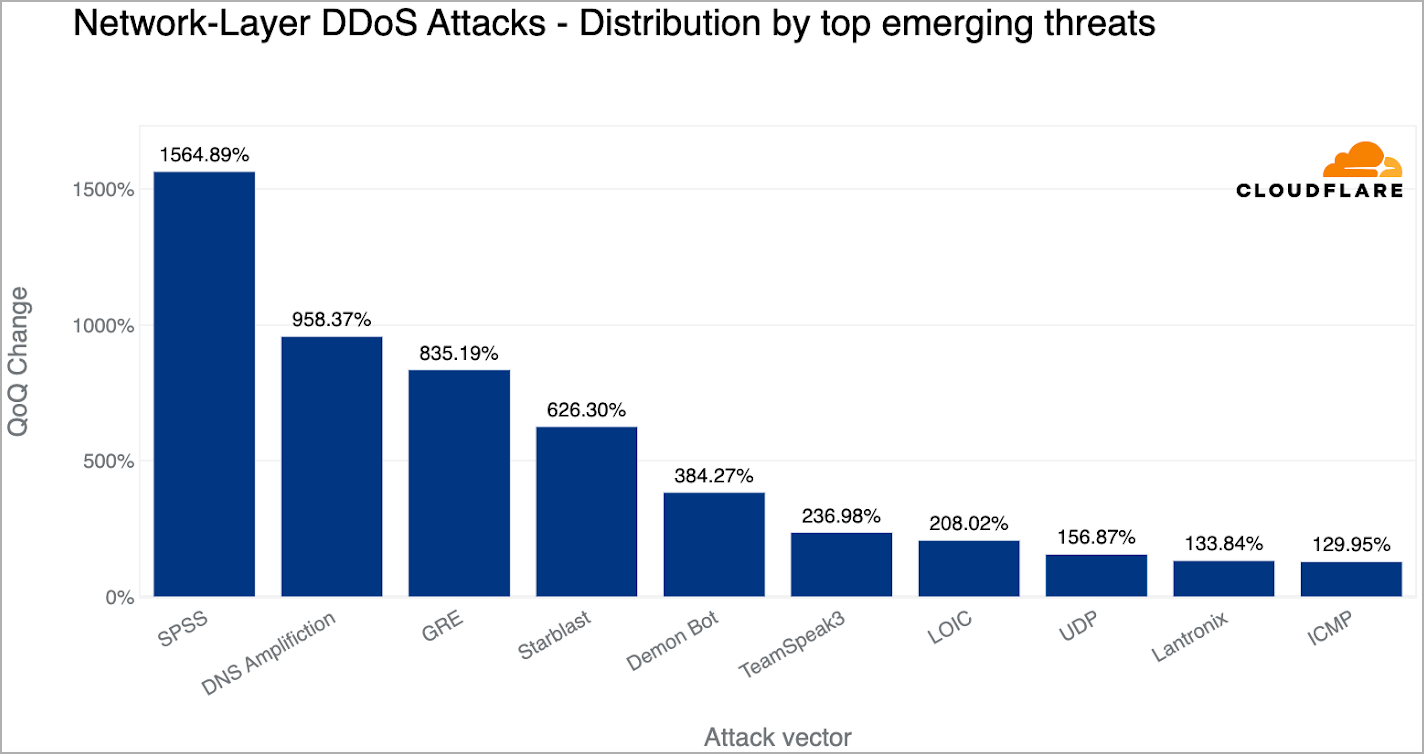
- 1565% QoQ increase in SPSS (statistical product and service solutions) based on DDoS attacks. This is fueled by the exploitation of two flaws (CVE-2021-22731 and CVE-2021-38153) in the Sentinel RMS License Manager service, exploited to launch reflection DDoS attacks.
- 958% QoQ increase in DNS amplification DDoS attacks, where attackers exploit flaws in the DNS infrastructure to generate large amounts of traffic.
- 835% QoQ increase in GRE (Generic Routing Encapsulation) based DDoS attacks, where attackers abuse the GRE protocol to flood the victim’s network with unnecessary requests.
DDoS attacks in Q1 2023 show an increasing trend in size and duration, targeting a wide range of industries. Therefore, effective defense strategies require automated detection and mitigation solutions.
[ad_2]
Source link
