[ad_1]
While analyzing its capabilities, Akamai researchers accidentally took down a cryptomining botnet that was also used for Distributed Denial of Service (DDoS) attacks.
As revealed in a report Released earlier this month, the KmsdBot malware behind this botnet was discovered by members of Akamai’s Security Intelligence Response Team (SIRT) after infecting one of their honeypots.
KmsdBot targets Windows and Linux devices with a wide range of architectures, and it infects new systems via SSH connections that use weak or default login credentials.
Compromised devices are being used to mine cryptocurrency and launch DDoS attacks, with some of the previous targets being gaming and tech companies, as well as luxury car manufacturers.
Unfortunately for its developers and fortunately for device owners, the botnet does not yet have persistence capabilities to evade detection.
However, this means that the malware has to start all over again if it is detected and removed or if it malfunctions in any way and loses its connection to the command and control (C2) server.
tango on the ground
This is also what led to the demise of the botnet after current versions of the KmsdBot malware were unintentionally disabled by Akamai researchers.
“In our controlled environment, we were able to send commands to the bot to test its functionality and attack signatures,” said Akamai, a vulnerability researcher. Larry Cashdollar Explained in New Report.
“As part of this analysis, a syntax error caused the bot to stop sending commands, thereby killing the botnet.”
What helped eliminate KmsdBot was its lack of error checking and “the coding equivalent of a typo”, which led to the malware crashing and stopping sending attack commands in due to an incorrect number of arguments to the C2 server.
Basically, as Cashdollar explained, the crash was caused by issuing an attack command where the space between the target website and the port was missing.
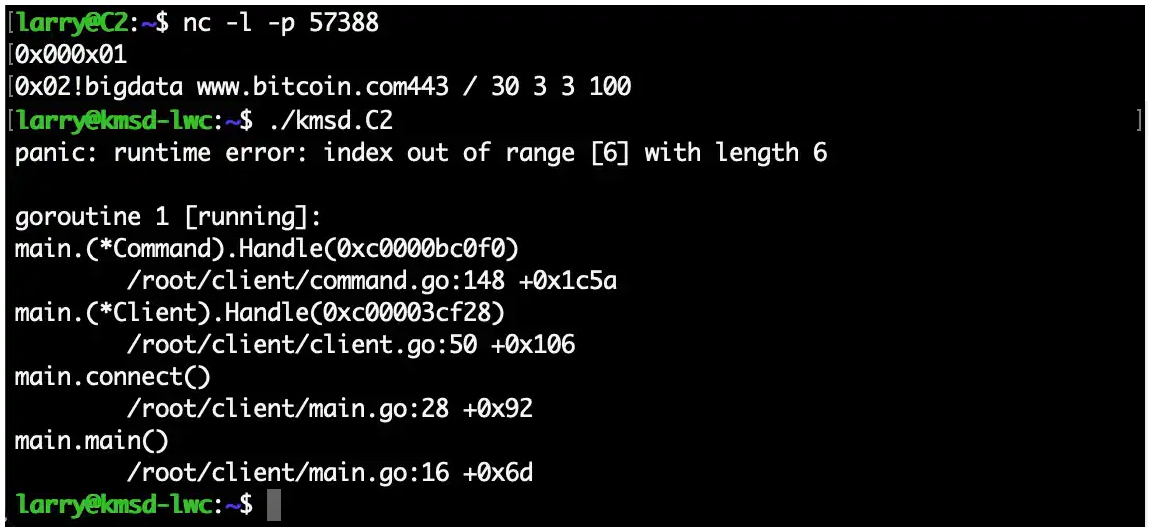
“This malformed command likely crashed all of the botnet code that was running on the infected machines and talking to C2 – essentially killing the botnet,” Cashdollar added.
“Because the bot has no persistence functionality on an infected machine, the only way to recover is to re-infect and rebuild the botnet from scratch.”
Organizations that may be the target of botnets using similar propagation tactics are advised to secure their systems against attack by:
- Do not use weak credentials and change the default ones for servers or deployed applications
- Ensure that all deployed software is up to date
- Using public key authentication for SSH connections to avoid compromise via brute force credentials
[ad_2]
Source link
