[ad_1]
![]()
The collapse of Silicon Valley Bank (SVB) on March 10, 2023 caused a stir throughout the global financial system, but for hackers, scammers and phishing campaigns, it becomes a great opportunity.
As several security researchers report, threat actors are already registering suspicious domains, running phishing pages, and preparing for business email compromise (BEC) attacks.
These campaigns aim to steal money, steal account data, or infect targets with malware.
The SVB disappears
SVB was a United States-based commercial bank, the 16th largest in the country and the largest depository bank in Silicon Valley, California.
On March 10, 2023, the bank went bankrupt after a run on its deposits. The failure was the largest of any bank since the 2007-2008 financial crisis and the second largest in US history.
This event impacted many companies and individuals in the technology, life sciences, healthcare, private equity, venture capital and premium wine sectors who were clients of SVB.
The chaotic situation is further aggravated by the prevailing elements of urgency, uncertainty and the large sums of money deposited in the bank.
Scammers jump at the chance
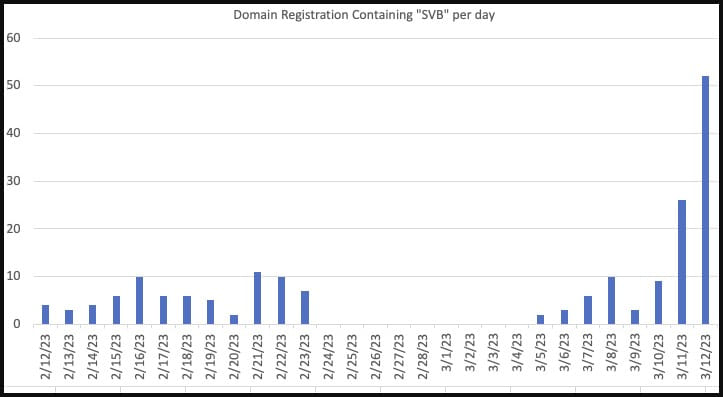
Security researcher Johannes Ulrich reported yesterday that threat actors are jumping at the chance, registering suspicious SVB-related domains that are highly susceptible to being used in attacks.
Some of the examples given in a report published on the SANS ISC website include:
- login-svb[.]com
- svbbailout[.]com
- svbcertificates[.]com
- svbclaim[.]com
- svbcollapse[.]com
- svbdeposits[.]com
- svbhelp[.]com
- svblawsuit[.]com
Ulrich warned that scammers might try to contact former SVB clients to offer them a bogus assistance package, legal services, loans or other services related to the bank’s collapse.
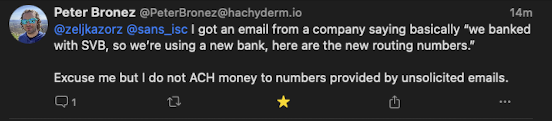
An attack already seen in the wild comes from BEC threat actors posing as SVB customers and telling customers they need payments sent to a new bank account after the bank collapses.
However, these bank accounts belong to threat actors, who steal payments intended for the legitimate company.
cyber intelligence firm Cyble today published a similar report exploring SVB-themed threat development, warning of these additional areas:
- svbdette[.]com
- svbclaims[.]net
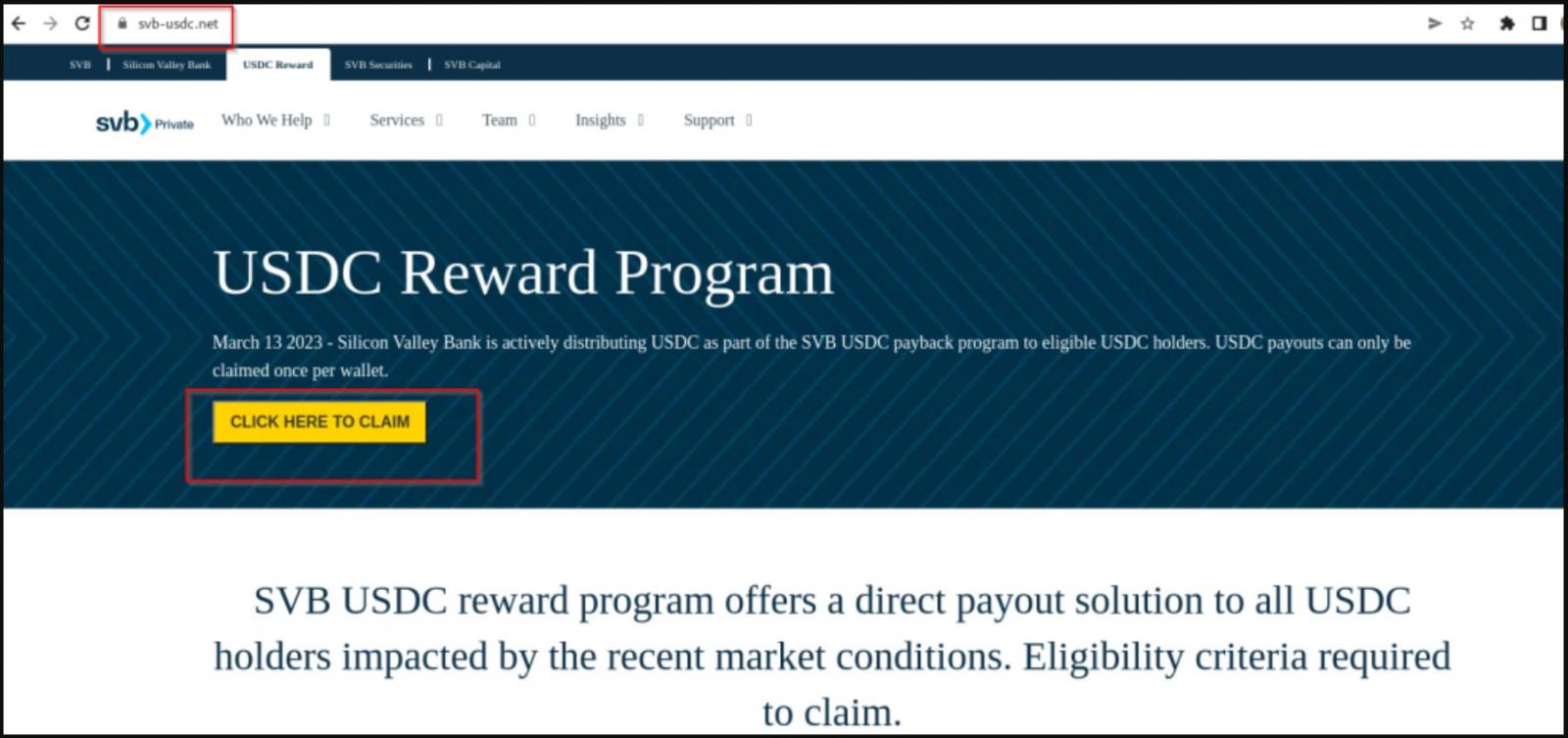
- svb-usdc[.]com
- svb-usdc[.]net
- svbi[.]io
- banksvb[.]com
- svbank[.]com
- svlogin[.]com
Many of these sites were registered on the day of the bank’s collapse, March 10, 2023, and are already hosting cryptocurrency scams.
These fraudulent pages tell SVB customers that the bank is distributing USDC as part of a “recovery” program.
“March 13, 2023 – Silicon Valley Bank is actively distributing USDC through the SVB USDC Refund Program to eligible USDC holders. USDC payouts can only be claimed once per wallet”, claims the cryptocurrency scam.
However, clicking the “Click here to claim” button on the site brings up a QR code that attempts to compromise Metamask, Exodus, and Trust Wallet crypto wallets when scanned.
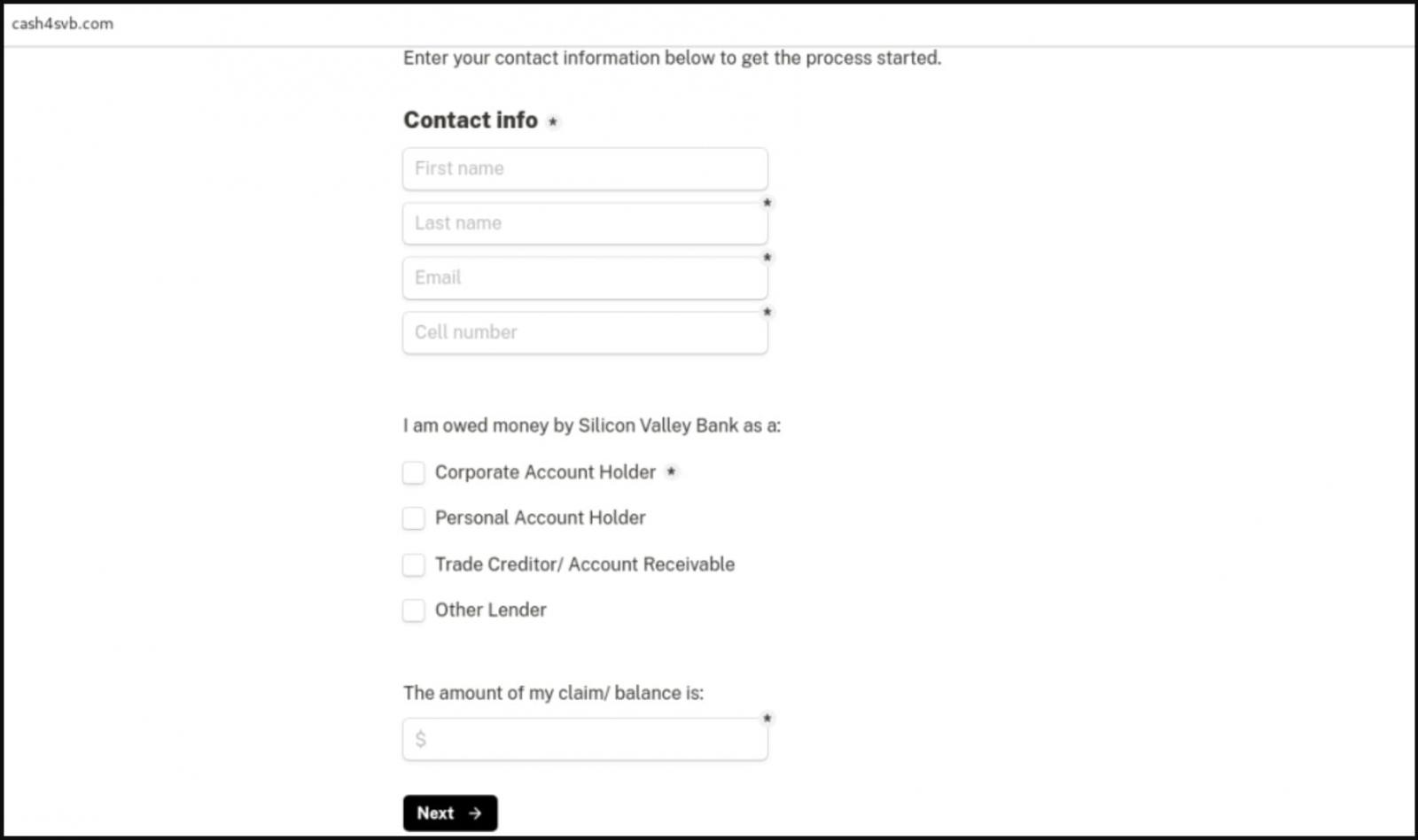
In another case, the threat actors behind “cash4svb.com” attempt to phish the details of former SVB customers who are trade creditors or lenders, promising them a return of between 65% and 85%.
Circular scams
Peer-to-peer payments company Circle, which runs the popular stablecoin USDC, had a cash reserve of $3.3 billion in SVB bank. However, the collapse of the SVB created uncertainty despite the company insurance of USDC liquidity.
This uncertainty has led to the creation of a network of fraudulent cryptocurrency sites using website domains such as:
- redeemed circle[.]com
- circle-reserves[.]com
- circleusdcoin[.]com
- circle-mintusdc[.]com
- svb-circle[.]com
- circle.web3claimer[.]net
- circle-usd[.]com
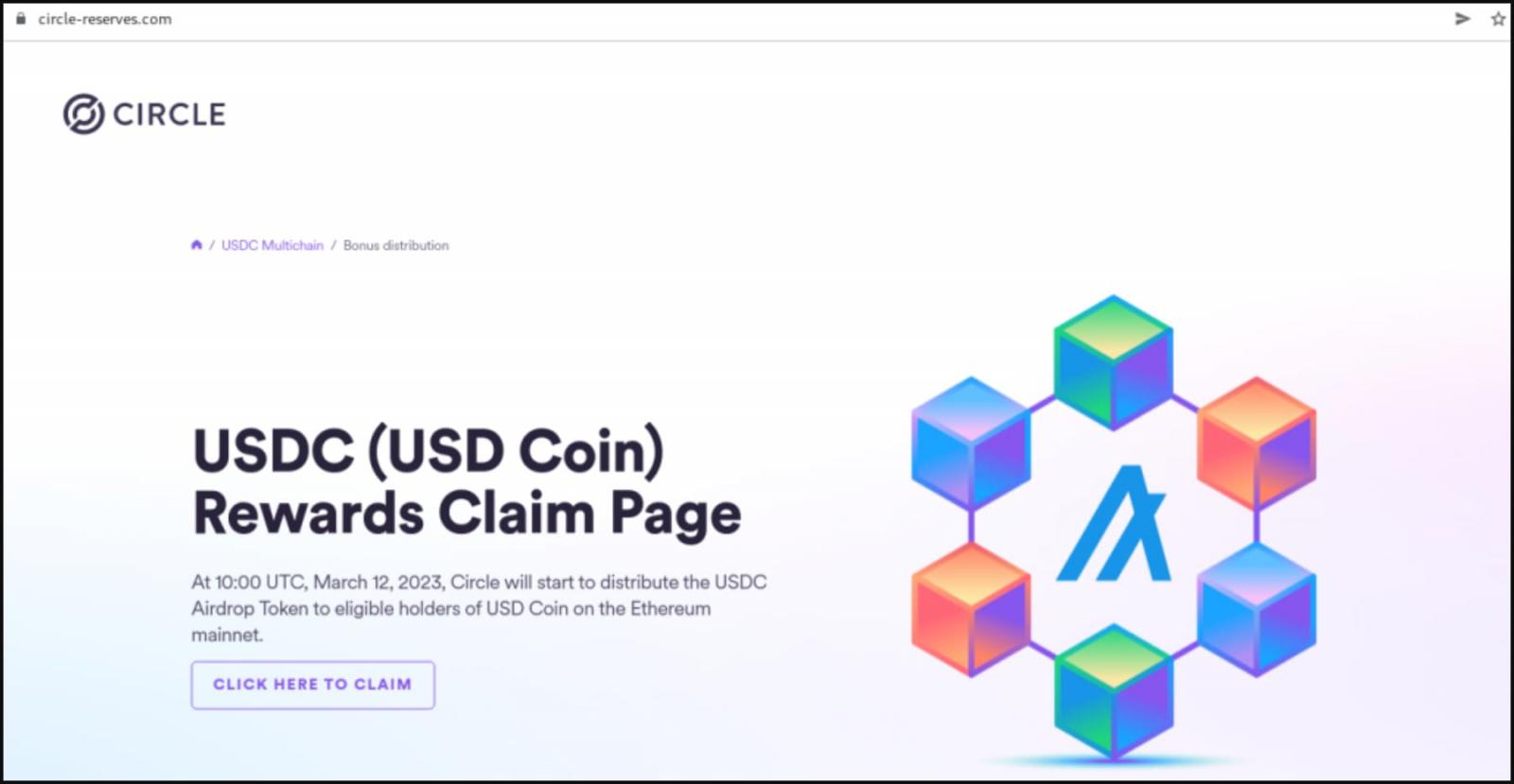
These websites have no real affiliation with Circle, and their sole purpose is to steal their visitors’ wallets, digital assets, or personal details.
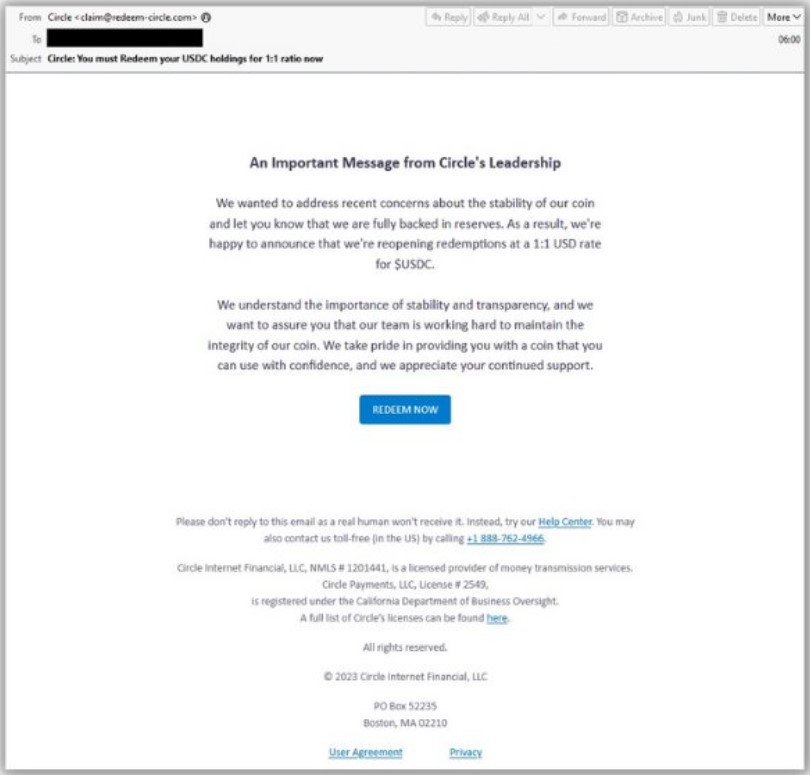
Email security firm Proofpoint has also spotted Circle scams stemming from the SVB events, sharing on Twitter a sample of phishing emails sent to targets.
If you are a former SVB customer, the best thing to do is to stay calm and follow the official communication channels of the United States Government And the FDIC.
Ignore all emails from unusual domains and check all requests from suspected SVB bank customers asking you to change bank details for payments.
The best method to confirm payment changes is to contact your contact by phone, not email, as email accounts can be compromised in these attacks.
[ad_2]
Source link