[ad_1]

Colombian energy company Empresas Públicas de Medellín (EPM) suffered a BlackCat/ALPHV ransomware attack on Monday, disrupting company operations and taking down online services.
EPM is one of Colombia’s largest public energy, water and gas providers, providing services to 123 municipalities. The company generated more than $25 billion in revenue in 2022 and is owned by the Colombian municipality of Medellin.
On Tuesday, the company asked about 4,000 employees to work from home as IT infrastructure was down and company websites were no longer available.
EPM disclosed to local media that they were responding to a cybersecurity incident and providing customers with alternative methods to pay for services.
The prosecutor’s office later confirmed THE COLOMBIAN this ransomware was behind the attack on EPM that resulted in device encryption and data theft.
However, the ransomware operation behind the attack has not been disclosed.
BlackCat ransomware behind the attack
BleepingComputer has since learned that ransomware operation BlackCat, aka ALPHV, was behind the attacks, claiming to have stolen corporate data in the attacks.
BleepingComputer also saw the sample encryptor and ransom notes from the EPM attack and confirmed that they are from the BlackCat ransomware operation.
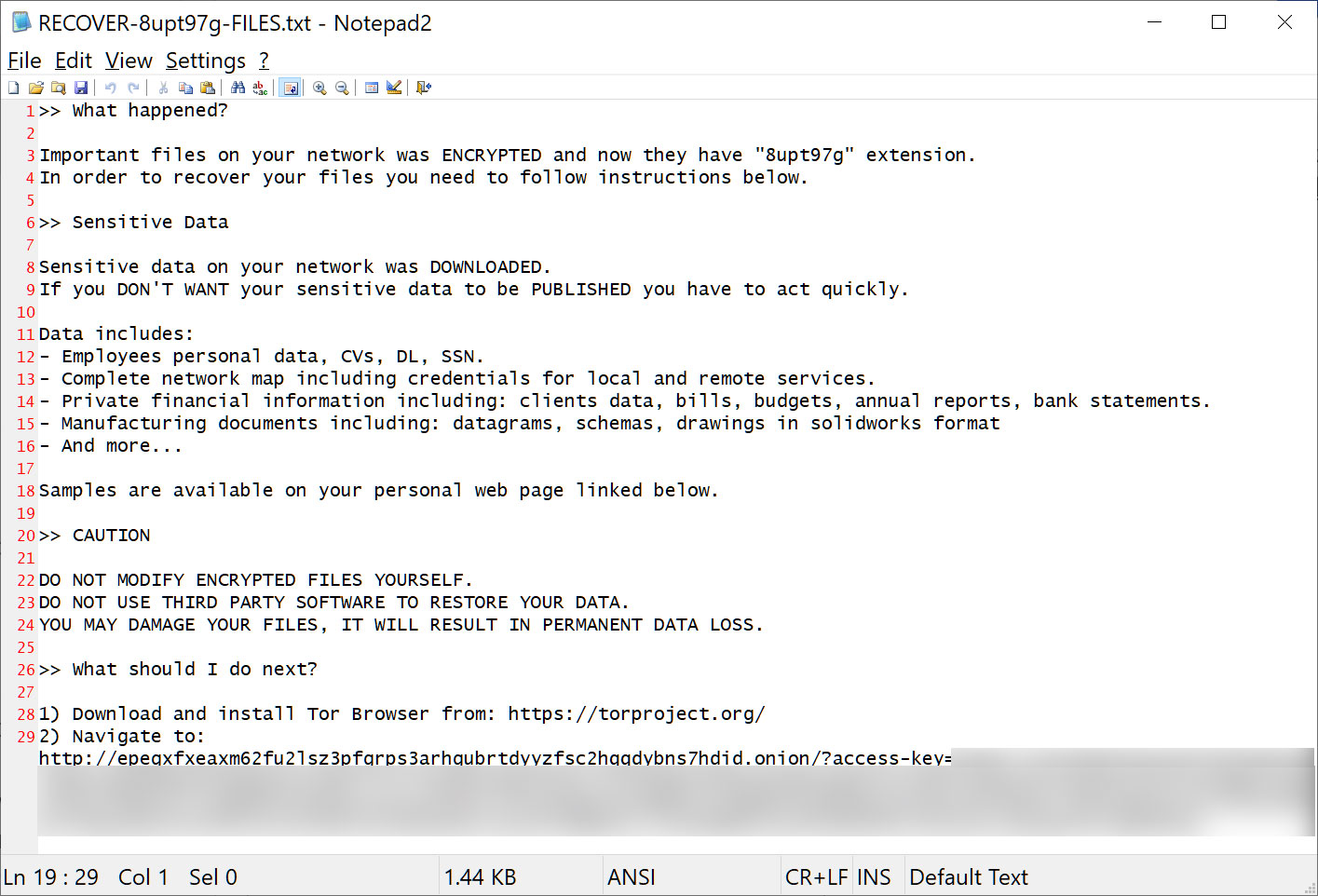
Source: BleepingComputer
Although the ransom note created during the attack indicates that the threat actors stole a wide variety of data, it should be noted that this is the exact text used in all BlackCat ransom notes and that is not specific to EPM.
However, other findings indicate that the hackers likely stole quite a bit of data from EPM during the attack.
Chilean security researcher Germán Fernández discovered a recent sample of BlackCat’s “ExMatter” data-stealing tool, uploaded from Colombia to a malware analysis site.
ExMatter is a tool used in BlackCat ransomware attacks to steal data from corporate networks before devices are encrypted. This data is then used as part of the ransomware gang’s double extortion attempts.
When the tool is run, it steals data from devices on the network and stores it on servers controlled by the attacker in folders named after the name of the Windows computer it was stolen from.
When analyzing the ExMatter tool, Fernández found that it was uploading the data to a remote server that was not sufficiently secure, allowing any visitor to see the data stored there.
In the Colombia ExMatter variant, data was downloaded to various folders starting with “EPM-“, as shown below. Fernández told BleepingComputer that these computer names match known computer naming formats used by Empresas Públicas de Medellín.
While it’s unclear how much total data was stolen, Fernández told BleepingComputer there were just over 40 devices listed on the site.
BleepingComputer contacted EPM to inquire about the attack and the amount of stolen data, but no response was immediately available.
This is not the first time that a ransomware attack has targeted a Colombian energy company.
In 2020, the Enel Group suffered a ransomware attack twice in the same year.
Colombia has also seen an increase in attacks in recent months, with the country’s health system disrupted last month by a RansomHouse attack on Keraltya multinational healthcare organization.
[ad_2]
Source link
