[ad_1]

The CloudPanel self-hosted web administration solution was found to have several security issues, including using the same SSL certificate private key across all installations and unintentionally overriding firewall rules to adopt default to lower settings.
The vulnerabilities were discovered by Rapid7 researcher Tod Beardsley in November 2022, who reported them to software vendor MGT-COMMERCE.
At the time of writing, the two issues mentioned above remain unresolved, while the software developer has addressed a third security issue regarding the installation script.
Faults on CloudPanel
The first issue concerns the reliability of the “curl to bash” installation procedure when downloading code without integrity checks, which the vendor quickly addressed by releasing a cryptographically secure checksum of the installation script.
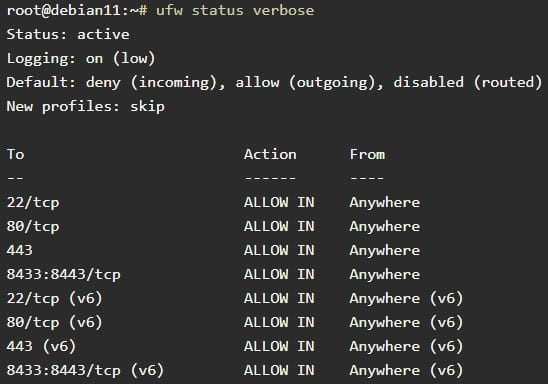
The second problem is that the CloudPanel Setup Script will reset a server’s pre-existing uncomplicated (ufw) firewall rules and introduce a much more permissive set of rules.
This means that if an administrator has configured their server’s firewall only to allow specific IP addresses to access a server’s ports, after installing CloudPanel, those rules will have been replaced by the more ruleset. permissive below.
Additionally, CloudPanel’s superuser admin account after installation is left empty, allowing savvy and fast attackers to set their own passwords and take control of the system.
Attackers would need to find new CloudPanel installations to exploit this issue, which is made possible by the third issue discovered by Rapid7.
The CloudPanel document warns of this issue with the following message:
“For security reasons, access CloudPanel as soon as possible to create the administrator user. There is a small window of time where bots can create the user. If possible, open port 8443 only for your IP via a firewall,” explains CloudPanel in their installation documentation.
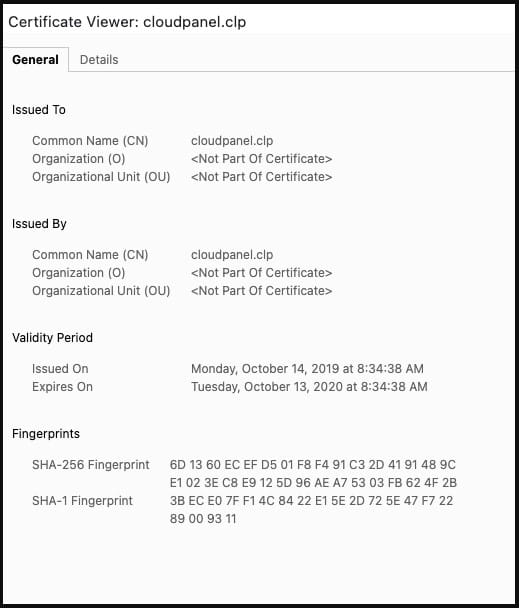
The third flaw is identified as CVE-2023-0391 and is caused by CloudPanel installations using a static SSL certificate, allowing attackers to find CloudPanel instances using the certificate thumbprint.
More worryingly, since the private key of each SSL certificate provided with CloudPanel is the same, this could allow hackers to spy on encrypted HTTPS traffic to CloudPanel servers.
Impact
Using the internet analysis tool Shodan, Rapid7 found 5,843 CloudPanel servers using the default certificate, most of them based in the United States and Germany.

(Quick7)
“By chaining firewall permissiveness and reused certificate issues, an attacker can target and exploit new CloudPanel instances as they are deployed,” Rapid7 research director Tod Beardsley explained in The report.
“It’s important to note that CloudPanel is presented as an easy-to-use interface for basic Linux administration, is aimed at relatively inexperienced users, and much of the documentation assumes a live installation procedure over the internet. routable with a new VPS instance.”
Self-hosting is currently going through a trending phase, enjoying growing popularity fueled by rising values of data privacy and control, personalization, and cost savings.
CloudPanel features prominently on the websites of cloud service providers like AWS, Azure, GCP, and Digital Ocean, promoting it as an easy-to-use administration solution for self-hosted Linux servers.
However, since there is no fix for firewall and SSL certificate issues, users are advised to immediately reconfigure their firewall rules after installing CloudPanel, and generate and install their own SSL certificate.
[ad_2]
Source link
