[ad_1]

A sophisticated threat actor named “CashRewindo” uses “legacy” domains in global malvertising campaigns that lead to investment scam sites.
Malicious advertising involves the injection of malicious JavaScript code into digital advertisements promoted by legitimate ad networks, leading website visitors to pages that host phishing forms, drop malware, or operate scams.
CashRewindo’s malvertisement campaigns are spread across Europe, North and South America, Asia and Africa, using custom language and currency to appear legitimate to local audiences.
The analysts of Confident have been following “CashRewindo” since 2018 and report that the threat actor stands out for having an unusually shrewd approach to setting up malicious advertising operations with great attention to detail.
Domains improve with age
Domain Aging it’s when hackers register domains and wait years to use them, hoping to bypass security platforms.
This technique works because old domains that haven’t been involved in malicious activity for a long time gain trust on the Internet, making them unlikely to be flagged as suspicious by security tools.
Confident says that CashRewindo uses domains that have aged for at least two years before being activated (having their certificates updated and assigned a virtual server).
The security firm was able to identify at least 487 domains used by the particular threat actor, some of which were registered as early as 2008 and first used in 2022.
Victims end up on these landing sites by clicking on infected advertisements found on legitimate sites.
To evade detection of “strong language” on legitimate sites, the threat actor alternates between innocuous wording and a call to action, usually starting the campaign cautiously and later moving to call ads. to action.
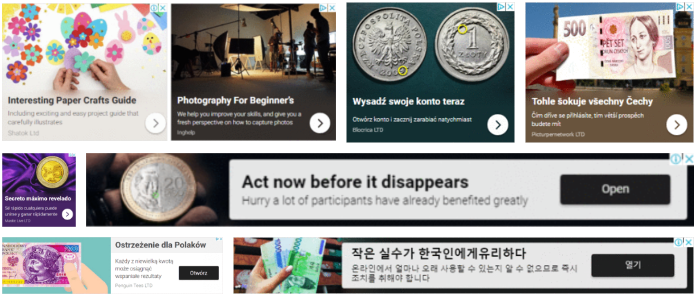
Malicious ads also feature a small red circle that helps confuse computer vision detection modules so they can’t catch the cheat.
Global but highly targeted
Each CashRewindo campaign targets a particular audience, so landing pages are configured to display either the scam or an innocuous or blank page for invalid targets.
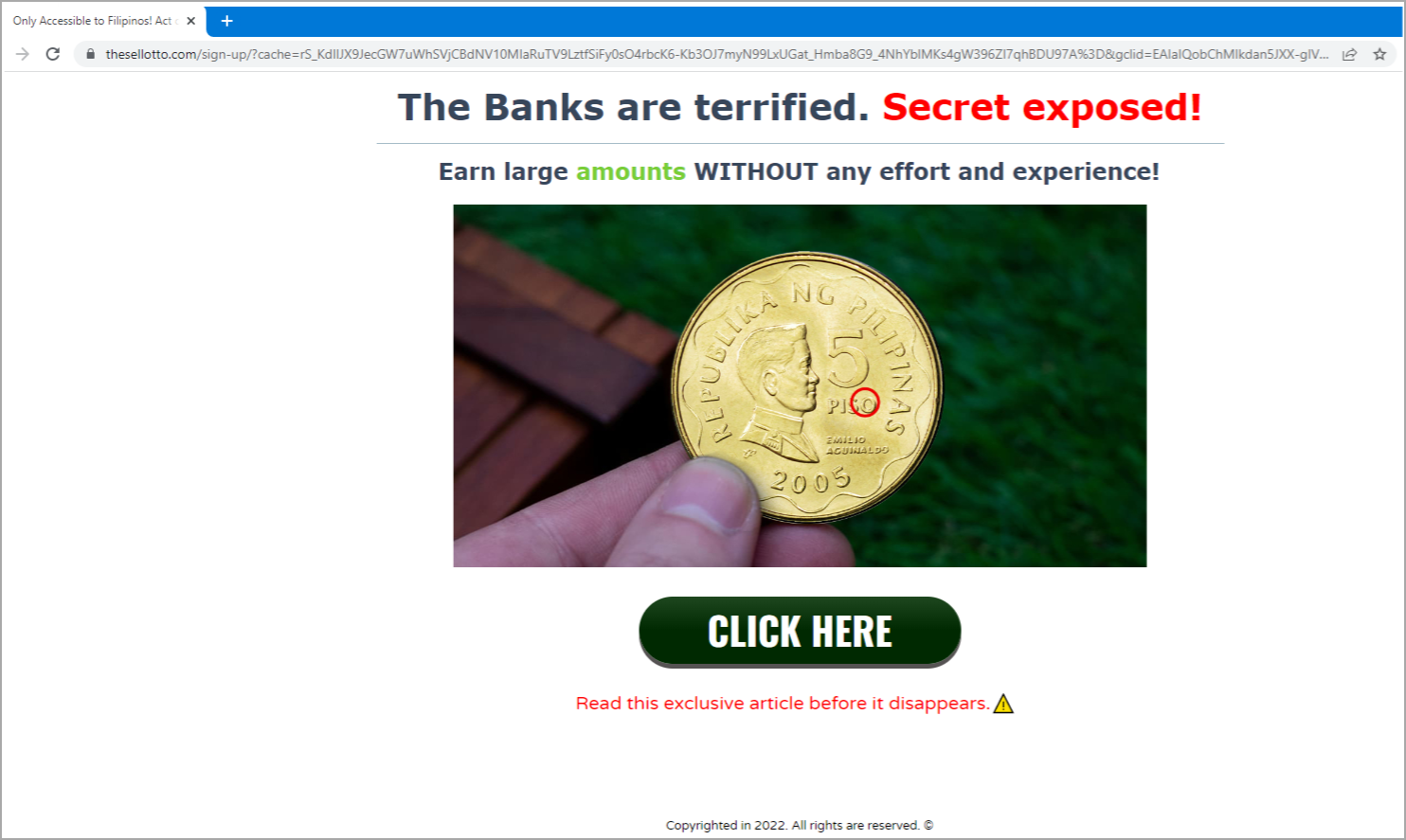
This is done by checking the time zone, device platform, and language used on the visitor’s system.
Users and devices outside the target audience who click on the embedded “Click here” button will be redirected to a harmless site.
Valid targets, on the other hand, will execute JavaScript code with the malicious code hiding in a common library to evade request inspection.
.png)
These users are redirected to a scam page and ultimately redirected to a fake cryptocurrency investment platform promising unrealistic returns on investment.

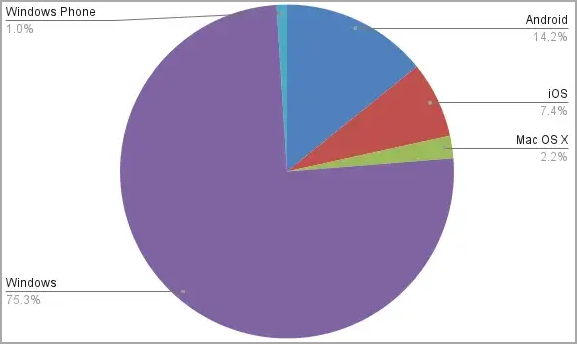
Confident reports that in 12 months, it has had over 1.5 million CashRewindo impressions, primarily targeting Windows devices.
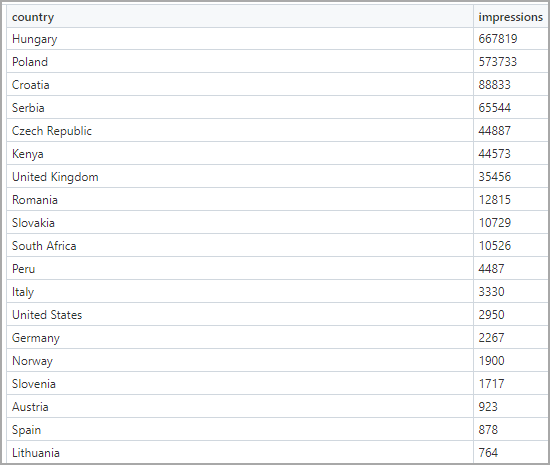
In terms of which countries generate the most of these impressions, the top 20 targeted placements are shown in the table below.
Investment scams are prevalent, but typically threat actors favor quantity over quality, pushing their hastily created fake sites to large user groups and hosting the scam platforms on newly registered domains doomed to disconnect quickly.
CashRewindo follows a different approach that requires more work but significantly improves the threat actor’s chances of success.
Any investment opportunity that guarantees returns is most likely a scam, so consider this a big red flag and do a thorough background check before depositing funds.
[ad_2]
Source link
