[ad_1]

Security researchers have noticed that operators of the ChromeLoader browser hijacking and adware campaign now use VHD files named after popular games. Previously, these campaigns relied on an ISO-based distribution.
The malicious files were discovered by a member of the Ahnlab Security Emergency Response Center (A SECOND) via Google search results to queries for popular games
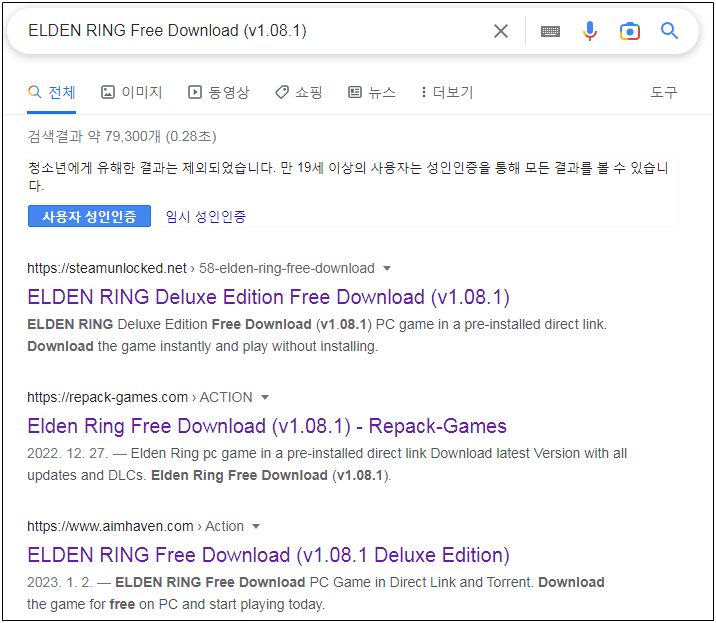
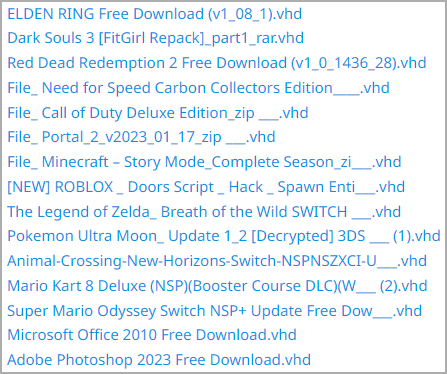
Some of the game titles abused for adware distribution purposes include Elden Ring, ROBLOX, Dark Souls 3, Red Dead Redemption 2, Need for Speed, Call of Duty, Portal 2, Minecraft, Legend of Zelda, Pokemon, Mario Kart , Animal Crossing and more.
A network of malvertising sites distributes malicious files, which appear as legitimate game-related packages, which install the ChromeLoader extension.
ChromeLoader hijacks browser searches to display ads. It also modifies browser settings and collects browser credentials and data.
According red canary data, the malware became more prevalent in May 2022. In September 2022, VMware reported new variants performing more sophisticated network activities. In some cases, the actor even delivered Enigma ransomware.
In all cases seen throughout 2022, ChromeLoader arrived on the target system as an ISO file. Lately, operators seem to prefer VHD packaging.
VHD files can be easily mounted on a Windows system and are supported by several virtualization software.
The images include several files, but only one of them, a shortcut called “Install.lnk”, is visible. Deploying the shortcut triggers the execution of a batch script that decompresses the contents of a ZIP archive.
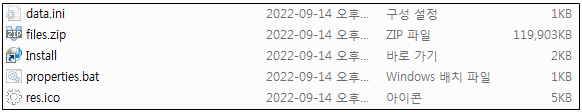
In the next step, the batch file executes “data.ini”, a VBScript and JavaScript that retrieves the final payload from a remote resource.
According to ASEC, ChromeLoader will start redirecting to advertising sites, thereby generating revenue for its operators.
The researchers say the addresses hosting the payload are no longer accessible. They note that the malicious Chrome extension created and executed by ChromeLoader can also collect credentials stored in the browser.
The ASEC report provides a brief set of Indicators of Compromise that can help detect the ChromeLoader threat.
Users are advised to avoid downloading games from unofficial sources and stay away from cracks for popular products as they usually pose a high security risk.
[ad_2]
Source link
