[ad_1]

US fast food chain Chick-fil-A has confirmed that customers’ accounts were hacked in a months-long credential stuffing attack, allowing threat actors to use account balances. stored rewards and access personal information.
In January, Reported computer that Chick-fil-A had begun investigating what it described as “suspicious activity” on customer accounts.
At the time, Chick-fil-A set up a support page with information on what customers should do if they detect suspicious activity on their accounts.
This warning came after BleepingComputer emailed Chick-fil-A before Christmas about Chick-fil-A user accounts being stolen in credential stuffing attacks and being sold online. .
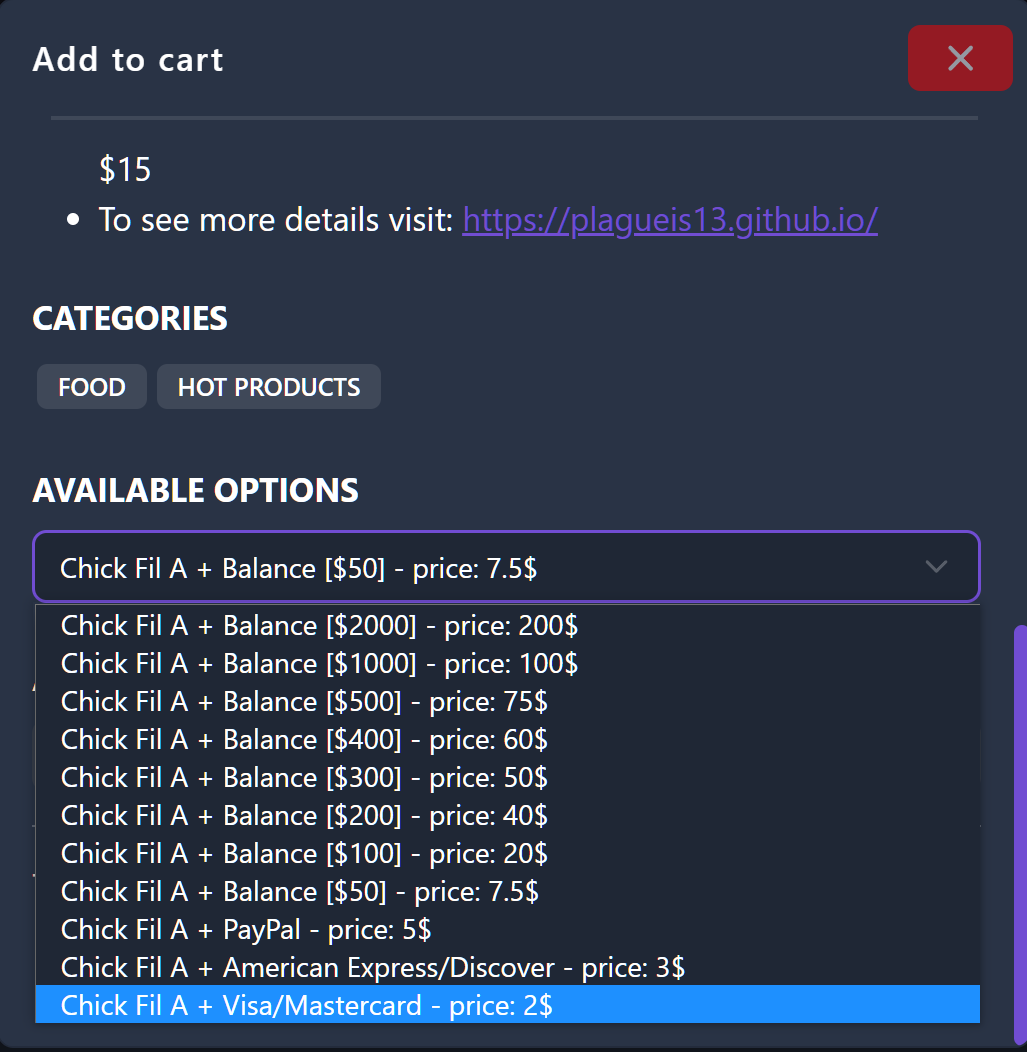
These accounts were sold for prices ranging from $2 to $200, depending on the rewards account balance and linked payment methods.
A Telegram channel seen by BleepingComputer showed people buying from these accounts and then sharing photos of their purchases made through these accounts.
Source: BleepingComputer
Chick-fil-A confirms credential stuffing attack
Today, Chick-fil-A confirmed our report in a security advisory submitted to the California Attorney General’s office, stating that they suffered a credential stuffing attack between December 18, 2022 and the February 12, 2023.
“After further investigation, we have determined that unauthorized parties launched an automated attack against our website and mobile application between December 18, 2022 and February 12, 2023 using account credentials (e.g., email addresses and passwords) obtained from a third party source.
Based on our investigation, we determined on February 12, 2023 that unauthorized parties subsequently gained access to your Chick-fil-A One account information.” – Notification Chick-fil-A.
The fast-food chain is warning affected customers that threat actors who gained access to their account would also have had access to their personal information, including their name, email address, Chick-fil-A One membership number and mobile payment number, QR code, hidden credit/debit card number and Chick-fil-A credit amount (e.g. e-gift card balance) in your account (if applicable).
For some customers, the information may have included birthdays, phone numbers, physical addresses, and the last four digits of credit cards.
In response to the attack, Chick-fil-A forced customers to reset passwords, froze funds loaded into accounts, and deleted all payment information stored on accounts.
Chick-fil-A also claims to have restored Chick-fil-A One account balances and added rewards to affected accounts as an apology.
As the accounts were hacked using credentials exposed in other data breaches, affected users must change their passwords on all sites they frequent, especially if they use the same Chick-fil-A password.
When resetting passwords, use a unique password for each site and store them in a password manager, like Bitwarden, so they can be easily managed.
Although there is no evidence that personal information has been misused, affected customers should also be on the lookout for potentially targeted phishing emails using this information.
[ad_2]
Source link
