[ad_1]

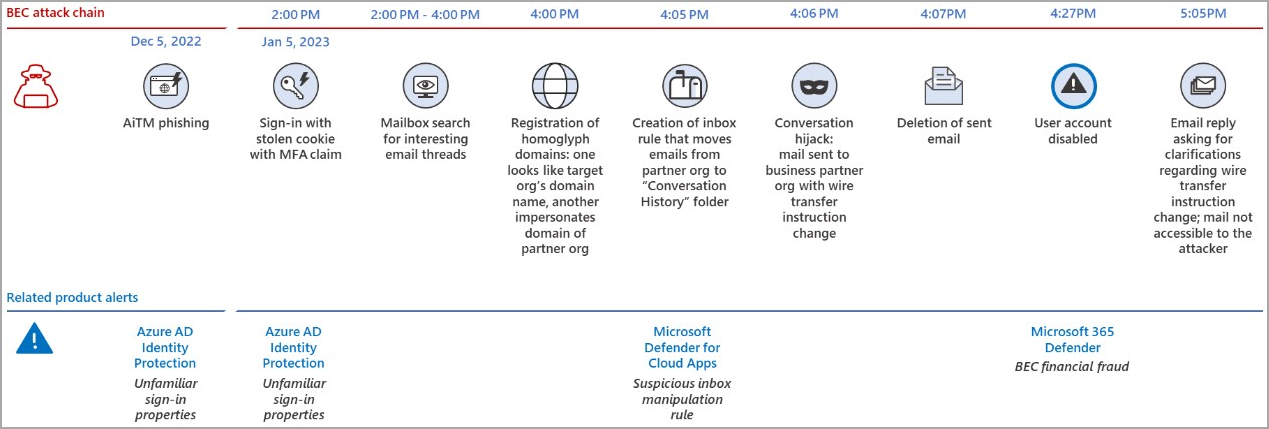
Microsoft’s Security Intelligence team recently investigated a business email compromise (BEC) attack and found that attackers moved quickly, with some steps taking only minutes.
The entire process, from logging in using compromised credentials to registering typosquatting domains and hijacking a thread, took threat actors just a few hours. .
This rapid progression of attacks ensures that targets will have minimal opportunity to identify signs of fraud and take preventative action.
A multi-billion problem
BEC attacks are a type of cyberattack where the attacker gains access to a target organization’s email account through phishing, social engineering, or buy account credentials on the dark web.
The attacker then poses as a trusted person, such as a senior or a vendor, to trick a financial department employee into approving a fraudulent wire transfer request.
According to FBI data, from June 2016 to July 2019, BEC attacks resulted in casualties amounting to more than $43 billionand this only applies to cases reported to law enforcement.
In a Twitter feedMicrosoft analysts explain that a recently investigated BEC attack began with the threat actor performing an “adversary in the middle” (AiTM) phishing attack to steal the target’s session cookie, bypassing MFA protection.
The attacker logged into the victim’s account on January 5, 2023 and spent two hours searching the mailbox for good threads to hack.
Thread Hijacking is a highly effective technique that makes the fraudulent message appear to be a continuation of an existing communication exchange, so recipients are much more likely to trust it.
After that, the attacker registered deceptive domains using homoglyph characters to make them appear nearly identical to the target organization’s and spoofed partner’s sites.
Five minutes later, the attacker created an inbox rule to siphon emails from the partner organization to a specific folder.
Within a minute, the attacker sent the malicious email to the trading partner requesting a change in bank transfer instruction and immediately deleted the sent message to reduce the likelihood of the compromised user discovering the breach.
From the first login to the deletion of the sent email, a total of 127 minutes had passed, reflecting a rush on the attacker’s side.
Microsoft 365 Defender generated a BEC financial fraud warning 20 minutes after the threat actor deleted the sent email and automatically halted the attack by disabling the user’s account.
“In our testing and evaluation of BEC detections and actions in customer environments facing real-world attack scenarios, dozens of organizations were better protected when accounts were automatically disabled by Microsoft 365 Defender,” says Microsoft.
“The new automatic disruption capabilities give the SOC team full control to investigate all actions taken by Microsoft 365 Defender and, if necessary, repair remaining and affected assets.”
Microsoft says its security product disrupted 38 BEC attacks targeting 27 organizations using high-trust extended detection and response (XDR) signals on endpoints, identities, email and SaaS applications.
[ad_2]
Source link
