[ad_1]
Cybercrime marketplaces are increasingly selling stolen corporate email addresses for as little as $2 to meet a growing demand from hackers who use them to compromise business emails and attack phishing or initial access to networks.
Analysts at Israeli cyber-intelligence firm KELA have been tracking the trend closely, reporting at least 225,000 email accounts for sale in underground markets.
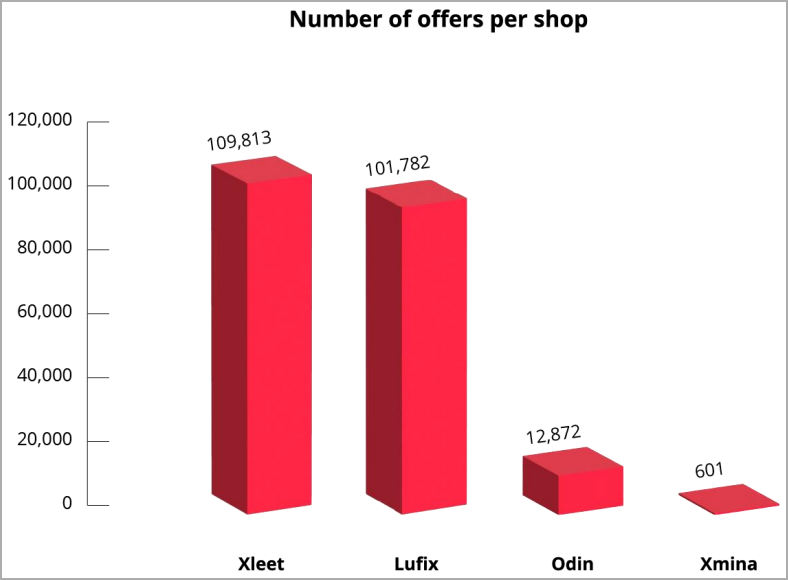
The biggest webmail shops are Xleet and Lufix, which claim to offer access to over 100,000 hacked corporate email accounts, with prices ranging from $2 to $30 or even more for highly desirable organizations.
Typically, these accounts were stolen through password cracking (brute-forcing) or credential stuffing, their credentials were stolen through phishing or bought from other cyber criminals .
Hackers use their access to corporate email accounts in targeted attacks such as business email compromise (BEC), social engineering, spear phishing, and deeper network infiltration.
Rise of auto-shop webmails
Sales of corporate email access have remained flat in the cybercrime space over the past two years, with threat actors on all major hacking forums selling “combined lists” of emails. emails to access various companies.
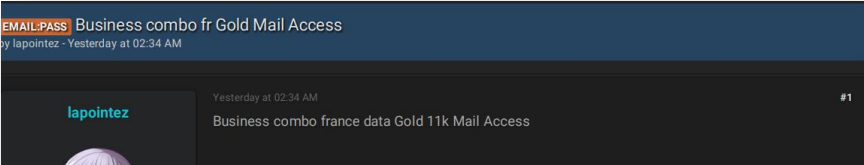
In a recent high-profile case, the “Everest” ransomware actor offered alleged access to an aerospace manufacturing company’s email accounts for $15,000.
Bundled and organized offers involve the tedious process of negotiating with the seller and taking risks on the validity of claims. At the same time, the demand for business emails continues to grow.
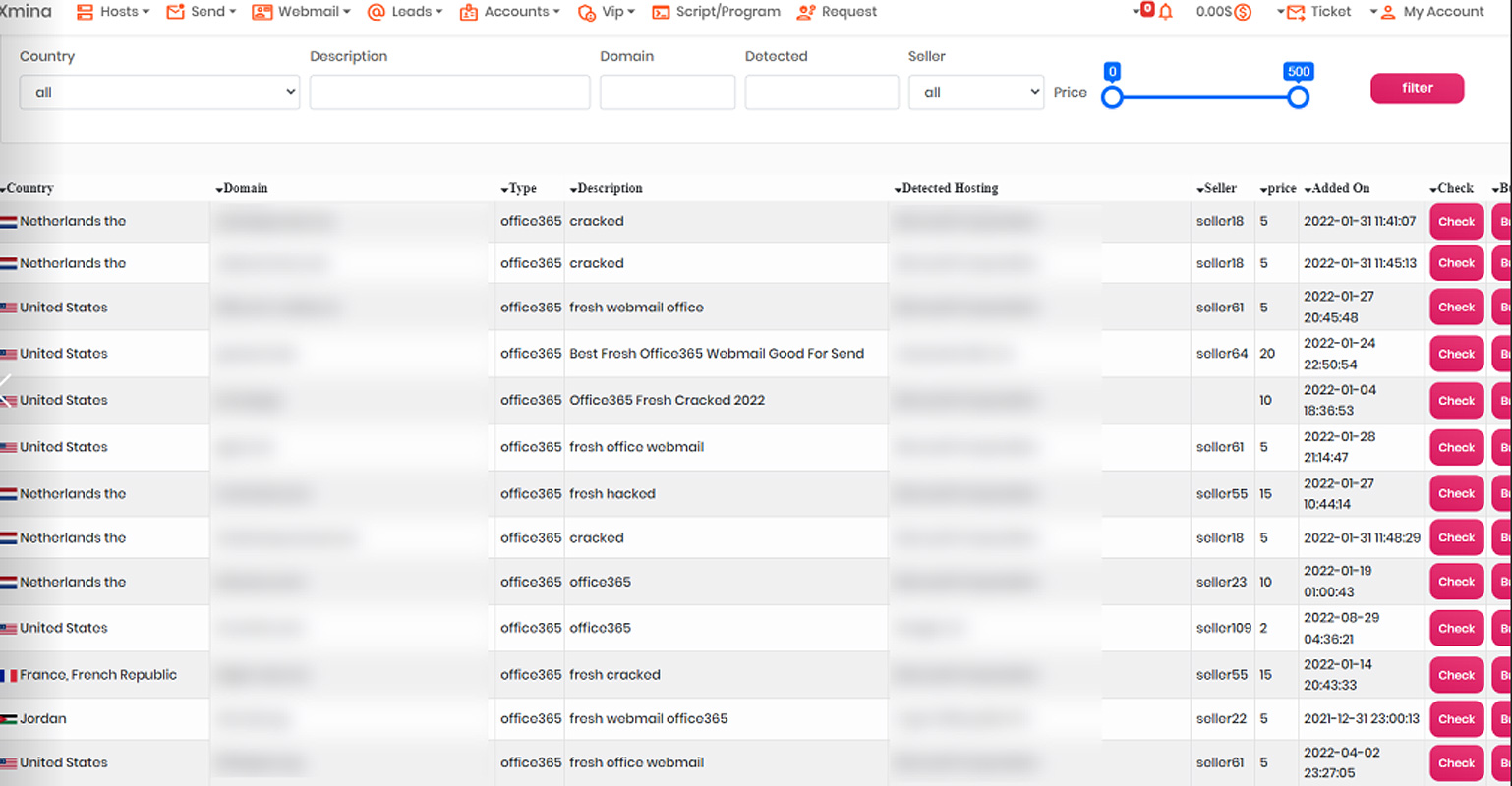
This has created the need for automated webmail shops like Xleet, Odin, Xmina, and Lufix, which allow cybercriminals to easily purchase access to email accounts of their choosing.
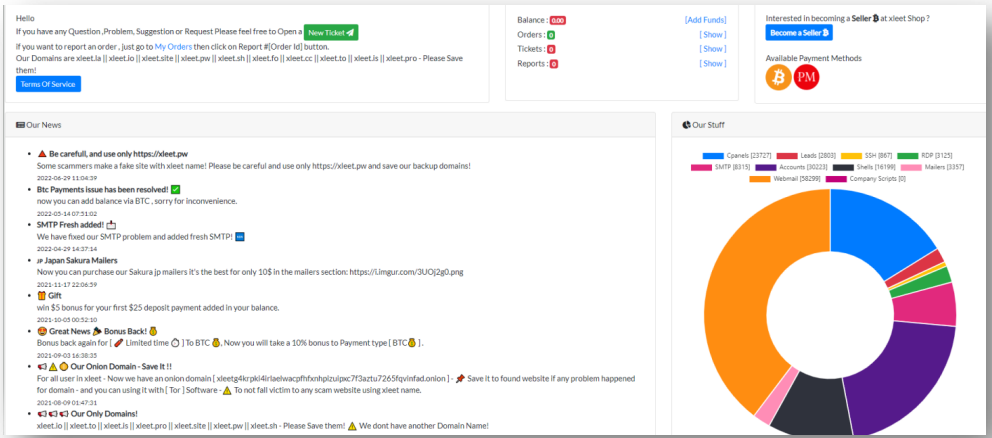
“Many of these stores offer advanced features, such as ‘proofs’ that webmail access is working,” explains KELA in the report.
“This evidence includes live verification of email to verify access or viewing a screenshot of the compromised account’s inbox.”
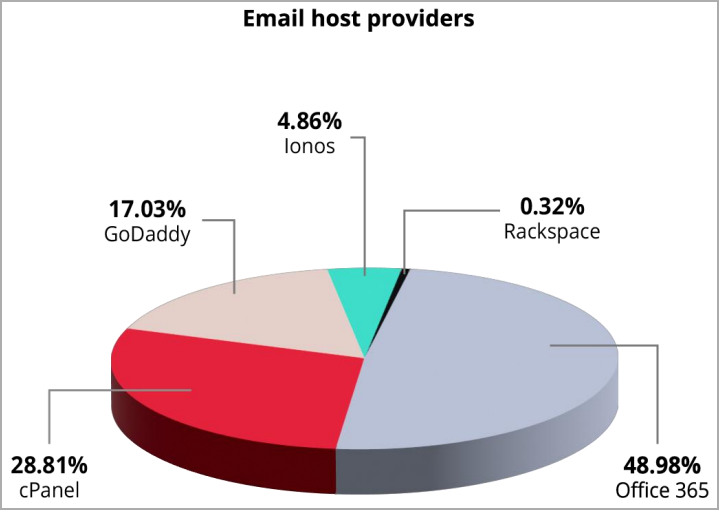
The most attractive offers are Office 365 accounts, which account for nearly half of all webmail listed, followed by hosts like cPanel, GoDaddy and Ionos.
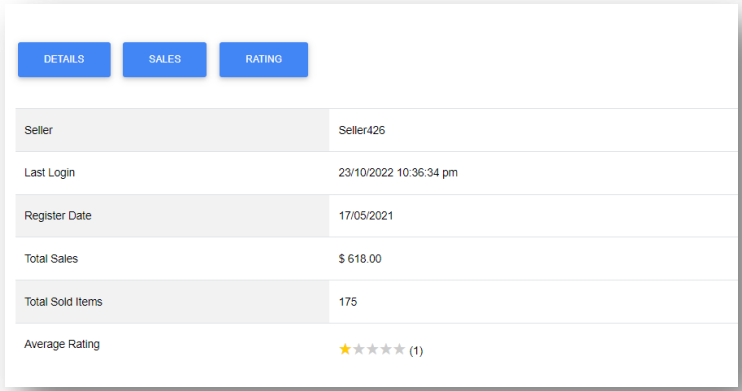
The sellers of these shops do not use aliases but hide behind a masking system assigning them numbers. Odin offers more details about sellers, such as number of items sold, total sales, and user ratings.
Odin and Xleet also clarify the source of webmails, with categories such as “hacked”, “cracked”, “logs” or “created”. However, the majority (98%) of Xleet have either been ‘hacked’ or ‘cracked’.
“Logs” are email ids stolen by information-stealing malware, while “created” are new email accounts that network intruders have created on the hacked company using email accounts. administrator compromised.
The rise of these markets makes it imperative to enforce periodic password resets across all services and platforms to render compromised credentials useless.
Since most webmails offered are cracked or hacked, using strong (longer) passwords and training staff to identify phishing emails would help reduce these threats significantly.
[ad_2]
Source link
