[ad_1]
QBot malware phishing campaigns have adopted a new distribution method using SVG files to smuggle HTML that locally creates a malicious installer for Windows.
This attack is performed via embedded SVG files containing JavaScript that reassemble a Base64-encoded QBot malware installer that is automatically downloaded through the target’s browser.
QBot is Windows malware arriving via phishing email that loads other payloads including Cobalt Strike, Brute Honey Badgerand Ransomware.
SVG based contraband
HTML contraband is a technique used to “smuggle” encoded JavaScript payloads into an HTML attachment or website.
When the HTML document is opened, it decodes the JavaScript and executes it, allowing the script to locally execute malicious behavior, including creating malware executables.
This technique allows threat actors to bypass security tools and firewalls that monitor malicious files at the perimeter.
Researchers from Cisco Talos observed a new QBot phishing campaign that begins with a stolen response string email prompting the user to open an attached HTML file.
This attachment contains an HTML smuggling technique that uses a base64-encoded Scalable Vector Graphics (SVG) image embedded in the HTML to hide malicious code.
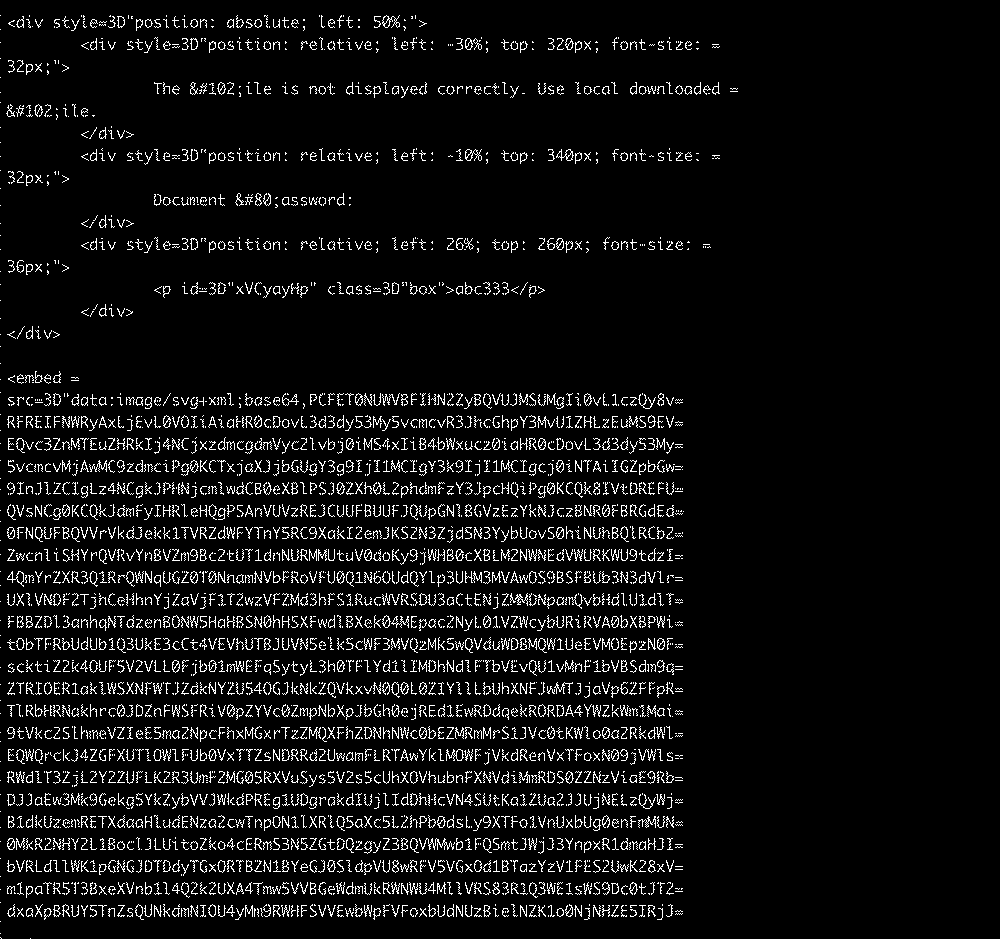
Unlike raster image types, such as JPG and PNG, SVGs are XML-based vector images that can include HTML tags
