[ad_1]

McAfee security researchers discovered a set of 16 malicious clicker apps that managed to sneak into Google Play, the official app store for Android.
Clicker apps are a special category of adware that loads advertisements in invisible frames or in the background and clicks on them to generate revenue for their operators.
The effect on the device can be decreased performance, overheating, increased battery usage, and inflated mobile data charges.
All 16 apps were removed from Google Play after McAfee reported them. However, they still racked up an install count of 20 million.
.png)
The baddest of the bunch is DxClean, which was installed five million times before being removed. It had a relatively positive overall user rating of 4.1 out of 5 stars.

DxClean bills itself as a system cleaner and optimizer, promising to detect the causes of system slowdowns and stop annoying ads while performing the exact opposite actions in the background.
Clicker app functions
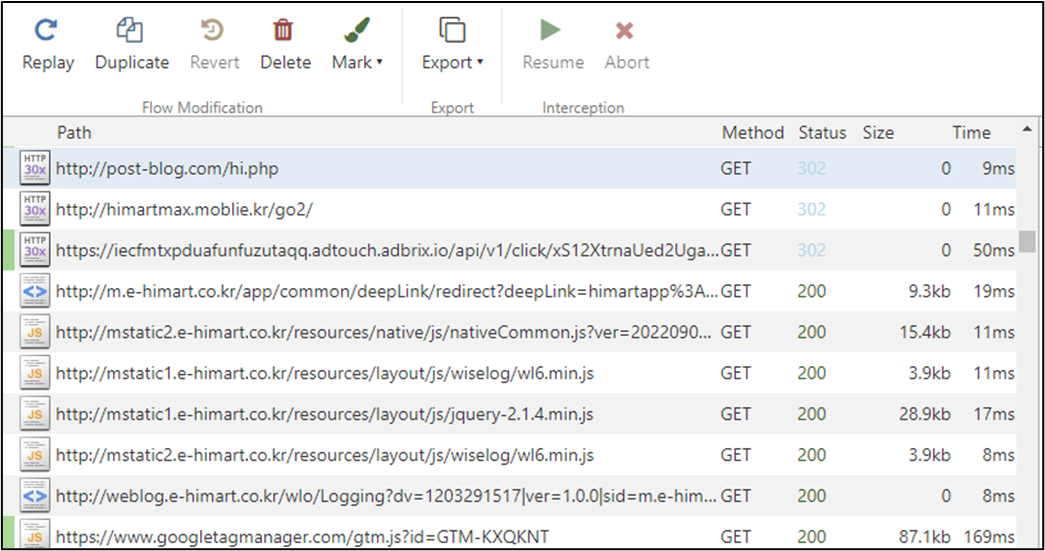
After launch, apps download their configuration from a remote location via an HTTP request and register a Firebase Cloud Messaging (FCM) listener to receive push messages.
These messages contain instructions for clickers, such as functions to call and parameters to use.
“When an FCM message receives and meets certain conditions, the latent function begins to work,” McAfee explains in the report.
“It mainly involves visiting websites that are delivered by FCM message and successively browsing them in the background while mimicking user behavior,” the researchers add.
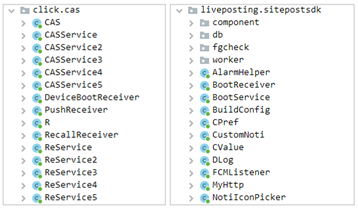
The auto-click feature is handled by the ‘click.cas’ component, while the agent that handles hidden advertising services is ‘com.liveposting’.
(McAfree)
McAfee analysts say the Live Publishing SDK can also work on its own, possibly to create ad impressions only, but recent versions of the apps feature both libraries.
The victim never interacts with the open websites and is unlikely to perform the underground processes that generate profit for the remote operators.
To stay under the user’s radar, the malicious operation does not start within the first hour after installing the app delays its start when the user is actively using the device.
To find out if any such apps are present on the device, users need to check the battery and internet usage. If the system has been sitting idle for a while, there is no reason for more battery drain and increased mobile data usage.
For the full list of all 16 clicker apps, see the indicators of compromise section at the bottom of The McAfee report.
[ad_2]
Source link
