[ad_1]

A new Distributed Denial of Service (DDoS) attack that took place on Monday, September 12 broke the previous record that Akamai had recently recorded in July.
DDoS attacks are cyberattacks that flood servers with bogus requests and garbage traffic, rendering them unavailable to legitimate visitors and customers.
Cybersecurity and cloud services company Akamai reports that the recent attack appears to come from the same threat actor, meaning the operators are further bolstering their swarm.
The victim is also the same as in Julyan anonymous customer from Eastern Europe who has been “relentlessly bombarded” by DDoS agents the whole time.
On September 12, these attacks peaked at unprecedented levels when “garbage” traffic sent to the target network peaked at 704.8 Mpps, about 7% higher than the July attack.
In addition to the attack volume, threat actors have also broadened their targeting, which was previously rather narrow, by focusing on the main enterprise data center.
This time, the threat actors extended their firepower to six data center locations in Europe and North America.
Additionally, Akamai detected and blocked 201 cumulative attacks, down from 75 in July, and recorded traffic sources from 1,813 IP addresses, down from 512 previously.
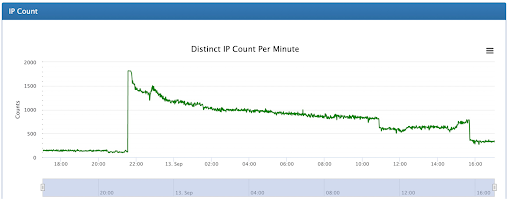
“The attackers’ command and control system was quick to activate the multicast attack, which grew in 60 seconds from 100 to 1,813 active IPs per minute,” comments Akamai in the report.
This widening of the targeting scope aims to reach resources that are not prioritized as critical and therefore insufficiently protected, but whose unavailability will still cause problems for the company.
“Such a widely distributed attack could drown an underprepared security team in alerts, making it difficult to assess the severity and scope of the intrusion, let alone fight back the attack.” -Akamai
The company in question, however, had taken precautions due to the July attack and had secured all of its 12 data centers, which enabled 99.8% of the malicious traffic to be pre-mitigated.
The motivation behind these persistent and large-scale attacks remains unknown, but the Eastern European region has been at the epicenter of hacktivism since the start of the year.
[ad_2]
Source link
