[ad_1]

Zyxel has released a security advisory with advice on protecting firewalls and VPN devices from ongoing attacks and spotting signs of exploitation.
This warning follows multiple reports of widespread exploitation of CVE-2023-28771 and exploitability and severity from CVE-2023-33009 and CVE-2023-33010, all of which impact Zyxel VPN and firewall devices.
“Zyxel urged users to install the patches through multiple channels, including issuing multiple security bulletins to registered users and advisory subscribers; notifying users of the upgrade through the push notification of the web GUI for on-premises devices; and applying scheduled firmware upgrades for the cloud, which have not yet done so,” warns Zyxel’s security consulting.
Malicious botnets are currently exploits CVE-2023-28771 to execute unauthenticated remote commands through specially crafted malicious packages and infect devices.
The other two flaws, CVE-2023-33009 and CVE-2023-33010, are buffer overflow bugs that could allow unauthenticated attackers to impose a denial of service state on vulnerable devices or run remote code.
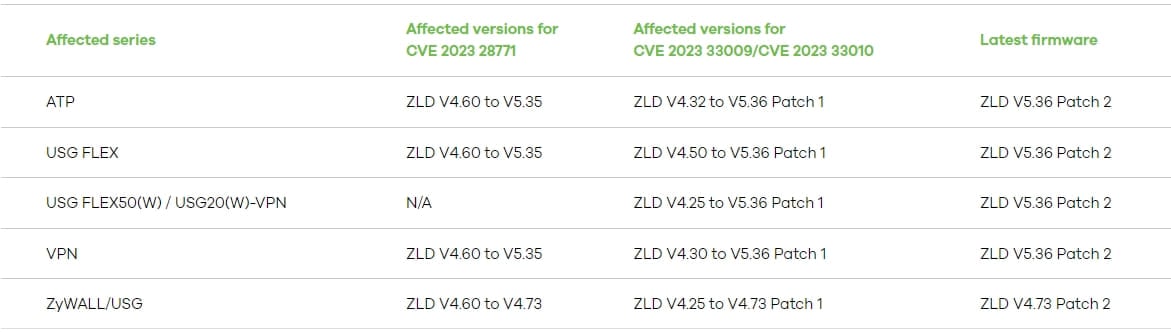
The following table summarizes the affected Zyxel products, the vulnerable firmware versions, and the target security updates for each.
Signs of Trouble and Mitigation
Zyxel says strong indicators of a hacked device include being unresponsive and being unable to access the device’s web UI or SSH management panel.
Frequent network interruptions and unstable VPN connectivity should also be treated as red flags and investigated.
The recommended action is to apply the available security updates, which are “ZLD V5.36 Patch 2” for ATP – ZLD, USG FLEX and VPN-ZLD, and “ZLD V4.73 Patch 2” for ZyWALL.
However, if updating is not possible now, system administrators are advised to implement some mitigation measures.
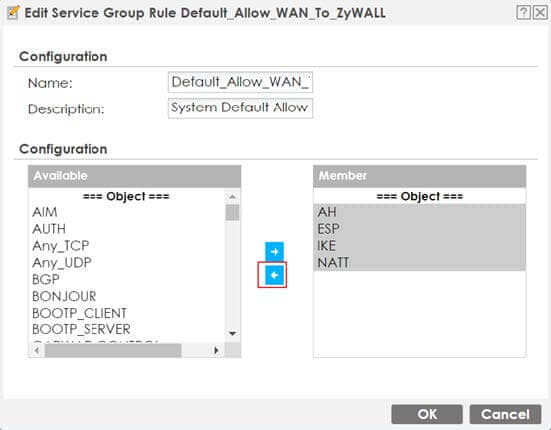
The first effective defense measure is to disable the HTTP/HTTPS services of the WAN (Wide Area Network). This should make vulnerable endpoints inaccessible to remote attackers.
If administrators need to manage devices over the WAN, they should enable “Policy Control” and add rules allowing only trusted IP addresses to access devices.
Enabling GeoIP filtering is also recommended to limit access to users/systems based on trusted locations.
Finally, Zyxel recommends disabling UDP ports 500 and 4500 if IPSec VPN is not needed, thus closing another avenue for attacks.
It is important to remember that attacks against listed products are currently in progressand are expected to increase in volume and severity. It is therefore imperative to take steps to protect your devices as soon as possible.
[ad_2]
Source link
