[ad_1]

Zimbra today urged administrators to manually fix an actively exploited zero-day vulnerability to target and compromise Zimbra Collaboration Suite (ZCS) mail servers.
This widely adopted messaging and collaboration platform is currently used by more than 200,000 businesses in 140 countries, including more than 1,000 government and financial organizations worldwide.
“A security vulnerability in Zimbra Collaboration Suite version 8.8.15 that could potentially impact the confidentiality and integrity of your data has surfaced. [..] The fix is expected to ship in the July patch release,” the company said. warned Thursday via a review that fails to inform customers that the bug is also abused in nature.
The security flaw (currently without a CVE ID) is a Mirrored Cross-Site Scripting (XSS) discovered and reported by security researcher Clément Lecigne of Google Threat Analysis Group.
As part of XSS attacks, hackers could steal sensitive user information or execute malicious code on vulnerable systems.
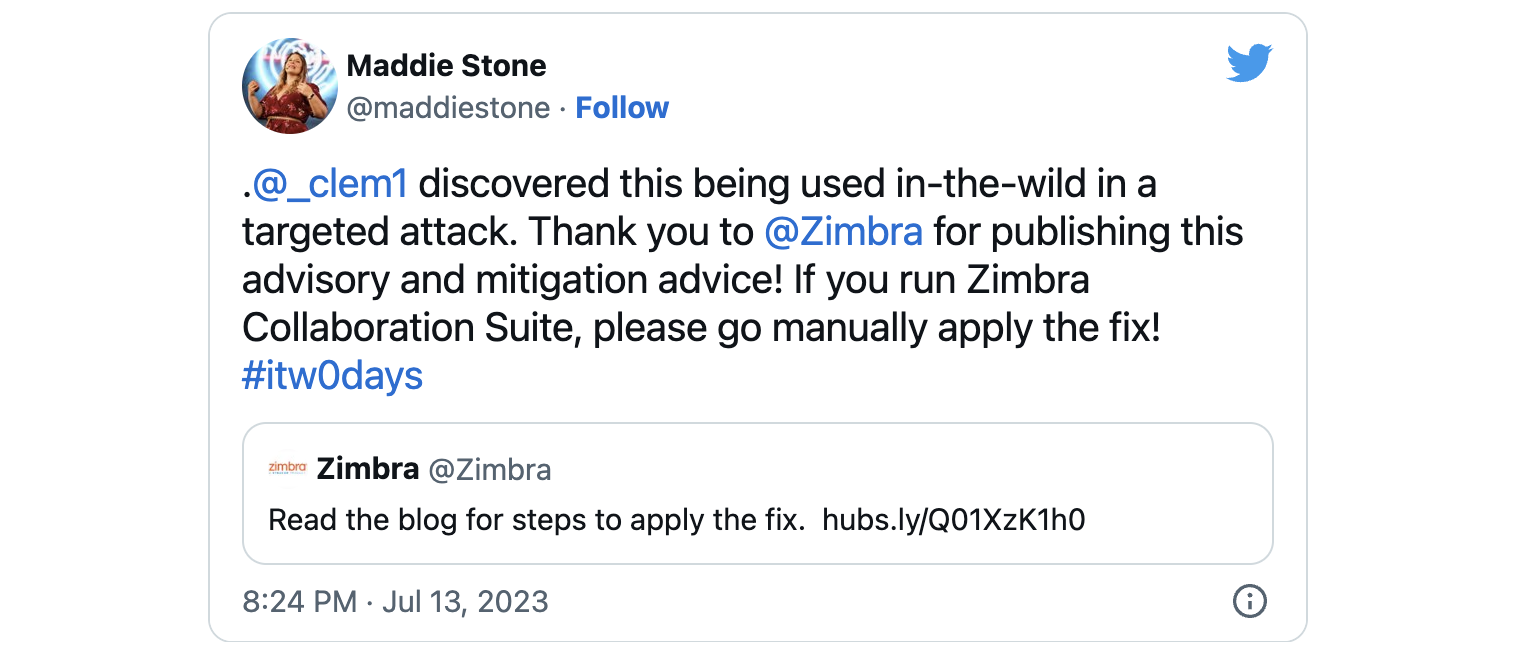
Maddie Stone from Google TAG tweeted today that this mirrored XSS vulnerability was discovered while being exploited in a targeted attack.
Although Zimbra has yet to provide security patches to address this actively exploited zero-day, it has provided a patch that administrators can manually apply to remove the attack vector.
“To maintain the highest level of security, we ask for your cooperation in manually applying the patch to all of your mailbox nodes,” the company said.
The procedure required to manually mitigate the vulnerability on all mailbox nodes requires administrators to complete the following steps:
- Make a backup of the file /opt/zimbra/jetty/webapps/zimbra/m/momoveto
- Edit this file and go to line number 40
- Update the parameter value to
- Before the update, the line appeared as
The patch can be applied without downtime as a restart of the Zimbra service is not required to apply the mitigation.
Admins should prioritize zero-day mitigation, as several Zimbra bugs have been explored in the wild to breach hundreds of vulnerable mail servers worldwide in recent years.
For example, as early as June 2022, Zimbra authentication bypass and remote code execution bugs were exploited to breach more than 1,000 servers.
Starting in September 2022, hackers started exploiting an unpatched RCE vulnerability in Zimbra Collaboration Suite, compromising nearly 900 vulnerable servers within two months.
The Russian hacking group Winter Viven also used exploits targeting another XSS bug reflected since February 2023 to violate NATO-aligned governments‘ webmail portals and steal email mailboxes belonging to civil servants, governments, military and diplomats.
[ad_2]
Source link