[ad_1]

The All-In-One Security (AIOS) WordPress security plugin, used by more than one million WordPress sites, was found to log plain text passwords of user login attempts to the site, endangering the security of accounts.
AIOS is an all-in-one solution developed by Updraft, offering web application firewall, content protection and login security tools for WordPress sites, promising to stop bots and prevent attacks by brute force.
About three weeks ago, a user reported that the AIOS v5.1.9 plug-in not only logged user login attempts to the aiowps_audit_log database table, used to track logins, logouts, and failed logins, and also to record the entered password.
The user expressed concern that this activity violates multiple security compliance standards including NIST 800-63 3, ISO 27000, and GDPR.
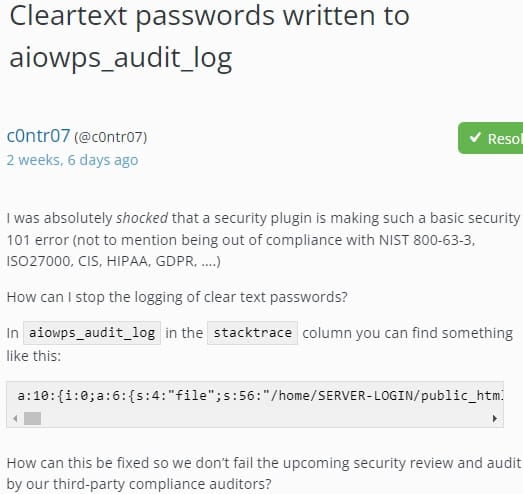
However, Updraft’s support agent replied saying it was a “known bug” and vaguely promising that a fix would be available in the next release.
After realizing the criticality of the problem, support offered development versions of the next version to affected users two weeks ago. Still, those attempting to install the development builds reported website issues and password logs not being deleted.
Fix now available
Finally, on July 11, the AIOS vendor released version 5.2.0, which includes a fix to prevent cleartext passwords from being saved and erase old entries.
“AIOS version 5.2.0 and newer updates fixed a bug in version 5.1.9 that caused users’ passwords to be added to the WordPress database in plain text,” reads the release announcement.
“It would be a problem if [malicious] site administrators had to try these passwords on other services where your users might have used the same password.”
If exposed individuals’ login credentials are not protected with two-factor authentication on these other platforms, malicious administrators could easily take control of their accounts.
Apart from the malicious administration scenario, websites using AIOS would face a high risk of hacking, as a bad actor gaining access to the site’s database could exfiltrate users’ passwords as plain text.
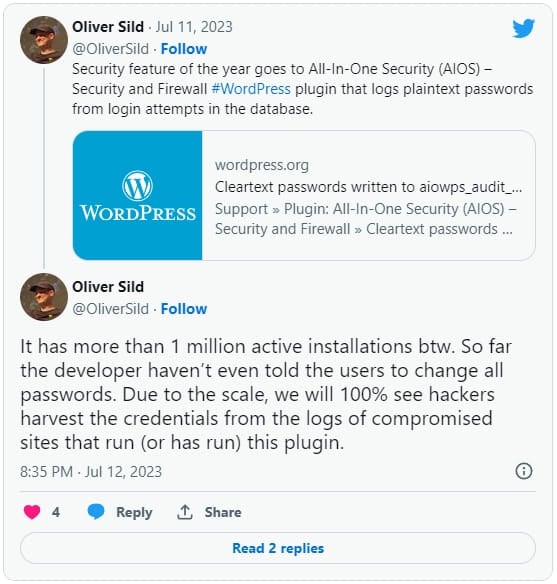
At the time of writing, WordPress.org Statistics show that around a quarter of AIOS users have updated to 5.2.0, so over 750,000 sites remain vulnerable.
Unfortunately, with WordPress a common target for threat actors, it’s possible that some of the sites using AIOS have already been compromised, and given that the issue has been circulating online for three weeks now, hackers have had ample opportunity to take advantage of the plugin creator’s slow response.
Furthermore, it is unfortunate that at no time during the exposure period did Updraft warn its users of the high risk of exposure, advising them on what action to take.
Websites using AIOS should now be updated to the latest version and require users to reset their passwords.
[ad_2]
Source link