[ad_1]

A ransomware operation targets Russian players of the multiplayer first-person shooter Enlisted, using a fake website to distribute trojanized versions of the game.
Enlisted is a legit game released by Gaijin Entertainment in 2021 with between 500,000 and 1 million monthly active players.
The game is free, so hackers could easily download the editor’s installer and modify it to distribute malicious payloads to unsuspecting users.
The ransomware bundled with the game installer claims to be the third major version of the notorious WannaCryeven using ‘.wncry’ file extension on encrypted files.
Engaged in ransomware
According The Cyble Researchers who analyzed the strain, this new “WannaCry” variant is based on the open-source Python “Crypter” locker, of course, designed for educational purposes.
It should be noted that this is not the first time that someone tried to imitate WannaCrypresumably to intimidate victims into prompt ransom payment.
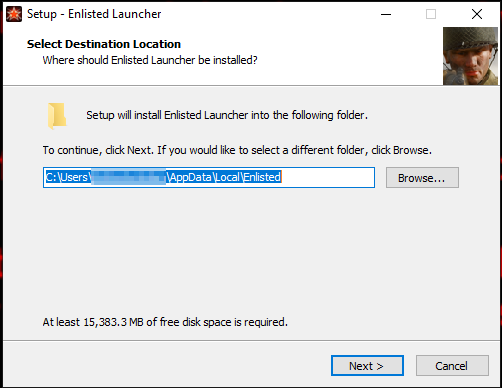
The installer downloaded from the fake website is “enlisted_beta-v1.0.3.115.exe”, which drops two executable files on the user’s disk if launched, namely “ENLIST~1” (the actual game) and “enlisted” (the Python ransomware launcher).
The ransomware creates a mutex during initialization to avoid multiple instances running on the infected computer.
Next, it analyzes its JSON configuration file, which determines which file types are targeted, which directories should be skipped, which ransom note to generate, which wallet address should receive the ransom, and other attack parameters.
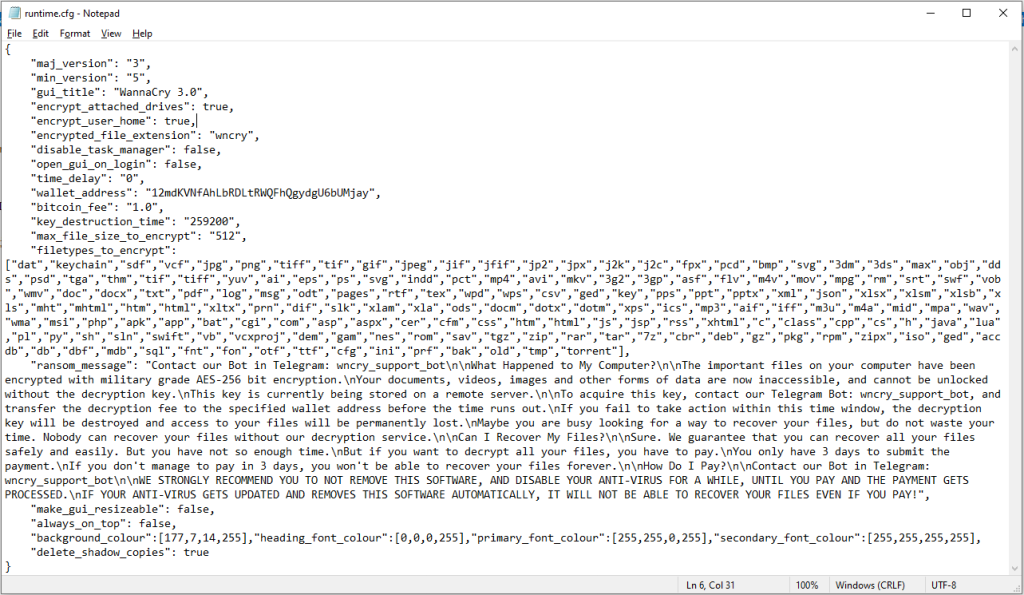
Next, the Crypter ransomware scans the working directory for a “key.txt” file to use in the encryption step, and if there isn’t one, it generates it.
Encryption uses the AES-256 algorithm and all locked files are given the “.wncry” filename extension.
Interestingly, the ransomware does not attempt to terminate processes or stop services, which is common practice in modern lockers.
However, it follows the common Windows shadow copy deletion policy to prevent easy data restoration.
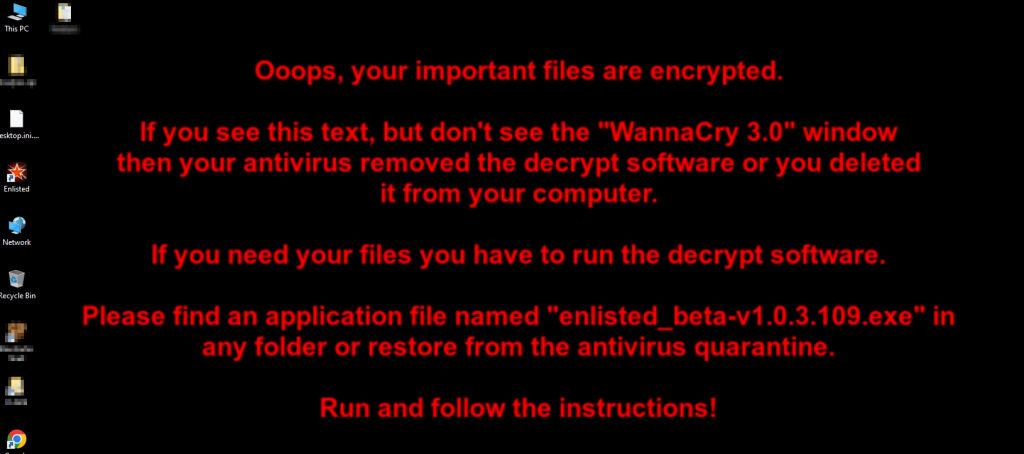
Once the encryption process is completed, the ransomware displays the ransom note on a dedicated GUI application, giving the victim three days to respond to the demands.
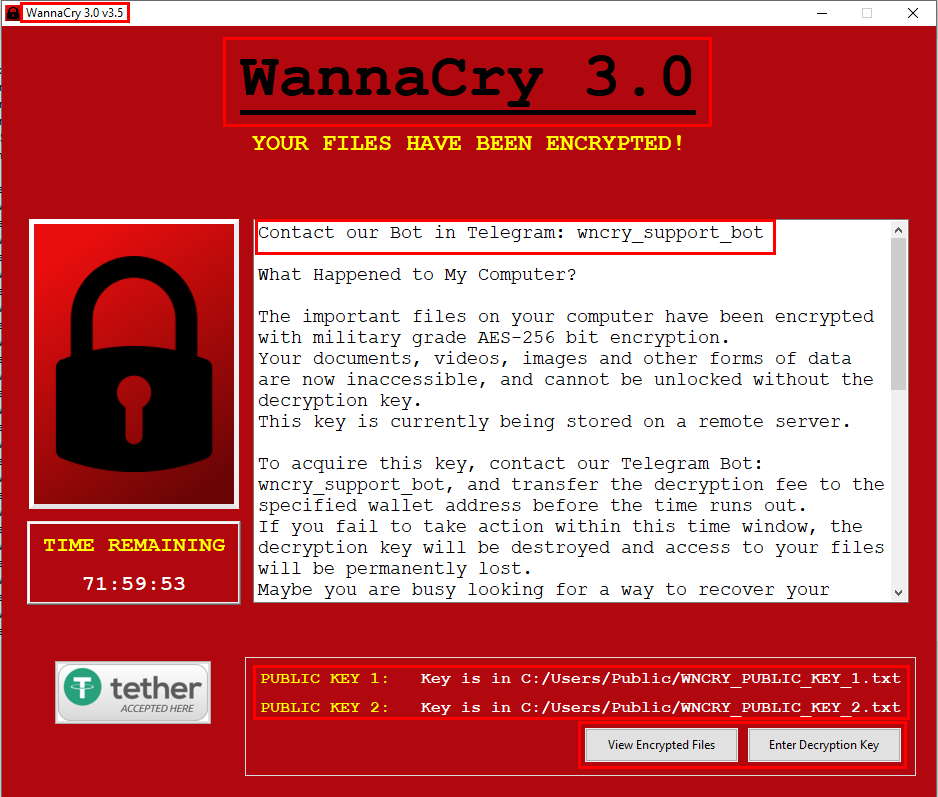
Threat actors also change the victim’s background image to ensure that their message gets through even if the victim’s antivirus blocks the launch of the GUI-based ransom note.
The attackers do not use a Tor site or provide a secure chat link to the victims, but instead use a Telegram bot for communications.
Nationwide bans on popular FPS titles in Russia have forced local gamers to look elsewhere for entertainment, and Enlisted is one of the alternatives being explored.
It seems that threat actors have jumped on this opportunity, and it is not unlikely that they are creating other fake sites for similar games with Russian localization.
[ad_2]
Source link
