[ad_1]

The National Institute of Standards and Technology (NIST) has announced that ASCON is the winning bid for the “Lightweight Cryptography” program to find the best algorithm to protect small IoT (Internet of Things) devices with limited material resources.
Small IoT devices are becoming increasingly popular and ubiquitous, used in wearable technology, “smart home” applications, and more. However, they are still used to store and manage sensitive personal information, such as health data, financial details, etc.
That said, having a data encryption standard in place is crucial to keeping people’s data secure. However, the weak chips inside these devices require an algorithm capable of providing strong encryption with very little computing power.
“The world is moving towards using small devices for many tasks ranging from detection to identification to machine control, and since these small devices have limited resources, they need security which has a compact implementation”, said Kerry McKaycomputer scientist at NIST.
“These algorithms should cover most devices that have these kinds of resource constraints.”
ASCON was selected as the best of 57 proposals submitted to NIST, multiple rounds of security analysis by leading cryptographers, implementation and benchmarking results, and feedback received at workshops. The entire program spanned four years, starting in 2019.
NIST says it all ten finalists exhibited outstanding performance that exceeded established standards without raising safety concerns, which made final selection very difficult.
ASCON was ultimately chosen as the winner for its flexibility, encompassing seven families, power efficiency, speed on weak hardware, and low overhead for short messages.
NIST also considered the algorithm to have stood the test of time, having been developed in 2014 by a team of cryptographers from Graz University of Technology, Infineon Technologies, Lamarr Security Research and the Radboud University, and winning the “light cipher” of the CAESAR cryptographic competition. category in 2019.
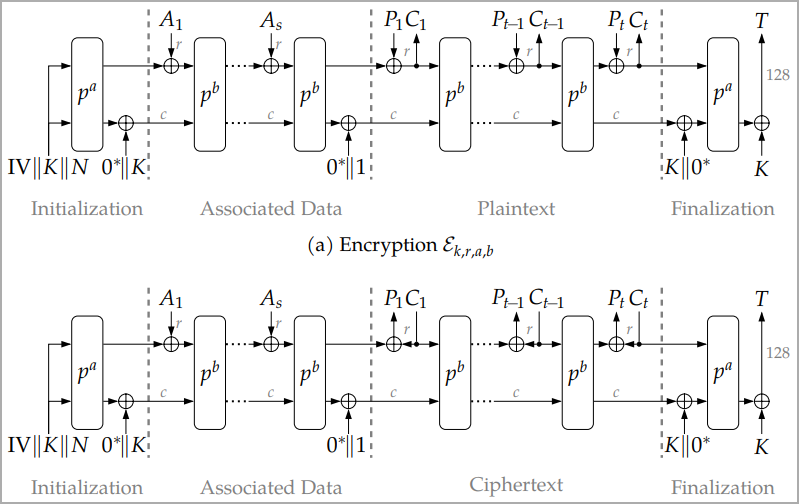
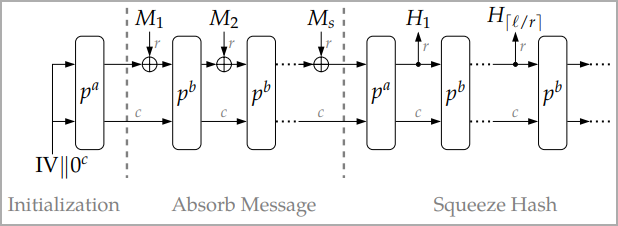
Two of ASCON’s native features highlighted in the NIST announcement are AEAD (authenticated encryption with associated data) and hashing.
AEAD is an encryption mode that ensures confidentiality and authenticity of transmitted or stored data, combining symmetric encryption and MAC (Message Authentication Code) to prevent unauthorized access or tampering.
Hashing is a data integrity verification mechanism that creates a string of characters (hash) from unique inputs, allowing two data exchange points to validate that the encrypted message has not been tampered with .
NIST still recommends the AES technique for AEAD and SHA-256 for hashing; however, these are not suitable for smaller and weaker devices.
Despite ASCON’s lightweight nature, NIST claims the scheme is powerful enough to offer some resistance to attacks from powerful quantum computers at its standard 128-bit nonce. However, that is not the goal or purpose of this standard, and lightweight cryptographic algorithms should only be used to protect ephemeral secrets.
NIST treats post-quantum cryptography as a separate challenge, running a different agenda to develop quantum-resistant standards, and the effort has already yielded its first results.
For more details on ASCON see Algorithms websiteor read the technical document submitted to NIST in May 2021.
[ad_2]
Source link
