[ad_1]

The Treasury Department’s Office of Foreign Assets Control (OFAC) today announced sanctions against ten individuals and two entities affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC) for their involvement in ransomware attacks.
Over the past two years, these threat actors have been linked to ransomware incidents where they have compromised networks belonging to organizations in the United States and around the world.
Their malicious activity overlaps that of state-sponsored hacking groups tracked by cybersecurity vendors under various names, including APT35, Charming Kitten, Phosphorus, DEV-0270, Tunnel Vision and Nemesis Kitten.
“Several cybersecurity firms determined that these sets of intrusions were associated with the Iranian government and identified them as having conducted a diverse range of malicious cyber activities, including ransomware and cyber espionage,” the Treasury Department said. said.
“This group has launched extensive campaigns against organizations and officials around the world, targeting in particular defense, diplomatic and government personnel in the United States and the Middle East, as well as private industries, including media, energy, business services and telecommunications”.
The IRGC Affiliate Group consists of employees and associates of Najee Technology Hooshmand Fater LLC (Najee Technology) and Afkar System Yazd Company (Afkar System), based in Iran:
- Mansour Ahmadi: Owner, Managing Director and Chairman of the Board of Najee Technology
- Ahmad Khatibi Aghda: Managing Director and Board Member of Afkar System
- Additional employees and associates: Ali Agha-Ahmadi, Mohammad Agha Ahmadi, Mo’in Mahdavi, Aliakbar Rashidi-Barjini, Amir Hossein Nikaeen Ravari, Mostafa Haji Hosseini, Mojtaba Haji Hosseini and Mohammad Shakeri-Ashtijeh.
The US Treasury Department also sanctioned people linked to Net Peygard Samavat for working with the IRGC and Iran’s Ministry of Intelligence and Security (MOIS) in 2019.
A year later, the US Treasury sanctioned Rana Intelligence Computing Company and some of its employees for acting as a front company that coordinated cyber attackers on behalf of MOIS.
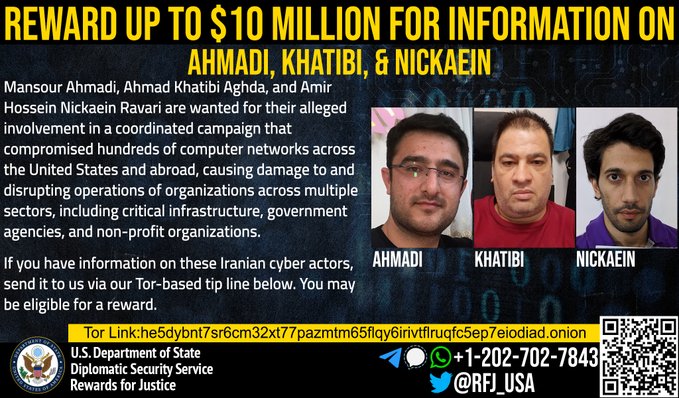
The US State Department has also offer 10 million dollars for information on Mansour Ahmadi, Ahmad Khatibi Aghda and Hossein Nikaeen Ravari, three of the sanctioned Iranians who have also been charged (indictment here) by the Department of Justice today for their involvement in ransomware attacks against American critical infrastructure organizations.
The malicious activity of this group of threats has also been described with additional technical details in a joint notice issued earlier today by cybersecurity agencies in the United States, Canada, United Kingdom and Australia.
Cybersecurity firm Secureworks also released a report today confirming information released today by the U.S. Treasury.
Secureworks said it successfully linked the Nemesis Kitten group (tracked as Cobalt Mirage) to Iranian companies Najee Technology, Afkar System and a third entity named Secnerd after taking advantage of several OPSEC errors made during a ransomware incident in June 2022.
Similar malicious activity related to Cobalt Mirage (whose elements overlap with the Phosphorus APT group) has been reported by SecureWorks’ Counter Threat Unit (CTU). in May.
Last week, Microsoft said the same group of threats (tracked as DEV-0270) has been moonlighting “for the generation of personal or business-specific income such as a subgroup of the Iranian-backed Phosphorus cyber-espionage group (aka Charming Kitten and APT35).
Redmond has also linked him to several Iranian companies, including Najee Technology, Secnerd and Lifeweb.
“The group is generally opportunistic in its targeting: the actor scans the Internet to find vulnerable servers and devices, which makes organizations with vulnerable and detectable servers and devices vulnerable to these attacks,” Microsoft added.
[ad_2]
Source link
