[ad_1]

The US Department of Health and Human Services (HHS) today issued a new warning to healthcare organizations nationwide regarding ongoing attacks by a relatively new operation, the Royal ransomware gang.
The Healthcare Sector’s Cybersecurity Coordination Center (HC3) – HHS’ security team – revealed in a new analyst note released Wednesday that the ransomware group was behind several attacks on American health organizations.
“Since emerging, HC3 has been aware of attacks on the health and public health (HPH) sector,” the council said. said.
“Due to the historic nature of ransomware victimizing the healthcare community, Royal should be considered a threat to the HPS industry.”
This ransomware group focuses on targeting US healthcare organizations based on past successful attacks.
So far, Royal has also claimed following each healthcare breach that they leaked all data allegedly stolen from the victims’ networks online.
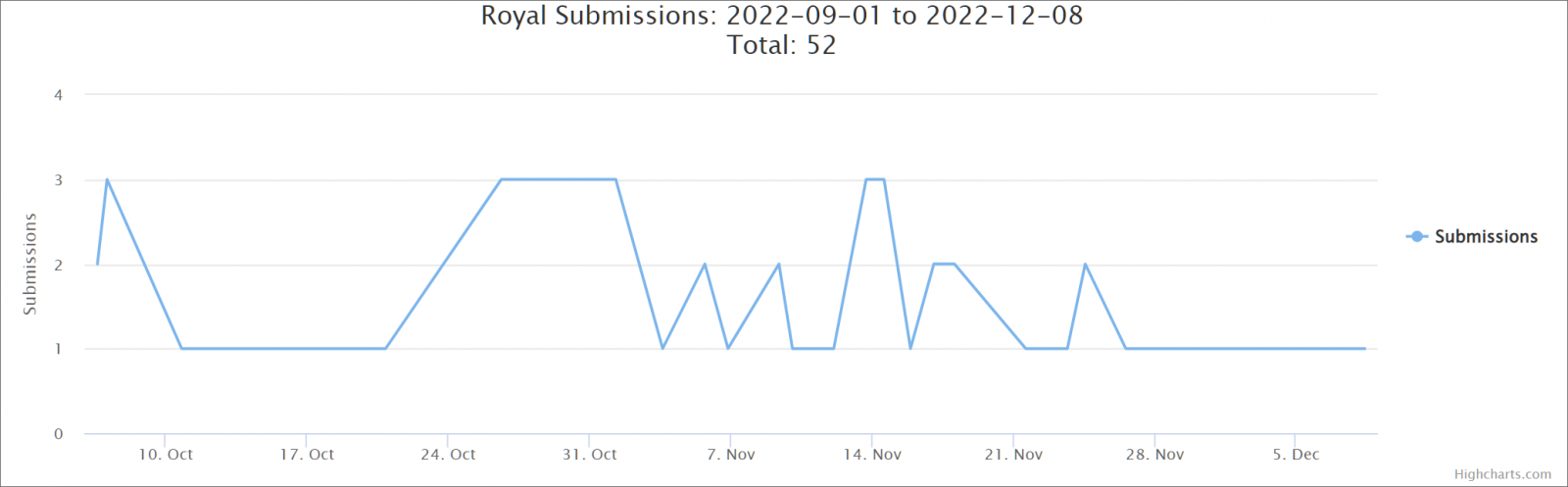
Strong increase in activity since September
The Royal Ransomware gang is a private operation with no affiliates and made up of experienced threat actors who have worked for other groups.
As of September 2022, Royal operators are rapidly escalating malicious activitiesmonths after it was first spotted in January 2022.
While initially they used ciphers from other gangs like BlackCat, they quickly switched to using their own encryptorsthe first being Zeon which generated Conti-like ransom notes.
Starting in mid-September, the ransomware gang was again rebranded as “Royal” and uses a new cipher that generates ransom notes with the same name.
Unusually for a ransomware gang, the group also uses social engineering to trick victimized companies into installing remote access software after callback phishing attacks where attackers impersonate software providers and food delivery services.
After infecting their targets and encrypting their corporate network systems, Royal will demand ransom payments ranging from $250,000 to $2 million.
Another uncommon tactic by Royal is to use hacked Twitter accounts to tweet information about compromised targets to journalists so that the attack gets media coverage and puts additional pressure on their victims.
These tweets will be tweeted to journalists and business owners, containing a link to the leaked data that was allegedly stolen from the victims’ networks before deploying the encryptor.
health under attack
The federal government has also warned of other ransomware operations known to actively target healthcare organizations across the United States.
For example, last month, HHS warned that Venus ransomware was impacting the nation’s health care, with at least one entity known to have fallen victim to its attacks.
Previous alerts have notified health and public health (HPH) organizations of the deployment of malicious actors maui and Zeppelin ransomware payloads.
A joint advisory issued by CISA, FBI and HHS warned in October that cybercrime group Daixin Team was also targeting the HPS sector in ongoing ransomware attacks.
Finally, Professional Finance Company Inc (PFC), a Colorado-based full-service customer account management company, shared a data breach notification in July regarding a Quantum ransomware attack in late February that led to a data breach affecting 657 healthcare organizations.
However, the attack could have had a much greater impact given that PFC helps thousands of US healthcare, government and utility organizations ensure customers pay their bills on time.
[ad_2]
Source link
