[ad_1]
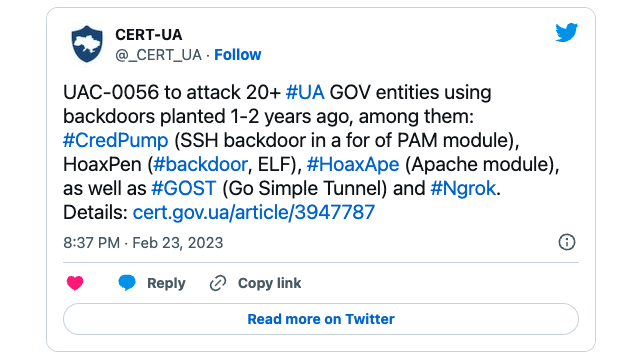
The Computer Emergency Response Team of Ukraine (CERT-UA) claims that Russian state hackers hacked into several government websites this week using backdoors planted as early as December 2021.
CERT-UA spotted the attacks after discovering a web shell Thursday morning on one of the hacked websites that threat actors (tracked as UAC-0056, Ember Bear or Lorec53) used to install additional malware .
This web shell was created in December 2021 and was used to deploy the CredPump, HoaxPen and HoaxApe backdoors a year ago, in February 2022, according to CERT-UA.
The threat actors also used GOST (Go Simple Tunnel) and Ngrok tools early in their attack to deploy the HoaxPen backdoor.
“Today, February 23, an attack was detected on a number of Ukrainian central and local government websites, leading to changes in the content of some of their web pages,” said the Ukrainian Defense Agency and SSSCIP Cybersecurity Security Policy. said THURSDAY.
“Currently, as part of the National Cyber Security Coordination Center United Response Team, experts from SSSCIP, the Ukrainian Security Service and Cyber Police are working together to isolate and investigate the cyber incident.
The SSSCIP added that the incident did not cause “essential system failures or disruptions” that would affect the functioning of Ukrainian public authorities.
Ember Bearthe group behind this week’s incident, has been active since at least March 2021 and is focused on targeting Ukrainian entities with backdoors, information thievesAnd fake ransomware mostly delivered via phishing emails.
However, its operators are also suspected of orchestrating attacks against North American and Western European organizations.
APT Group spotted stepping up phishing campaigns and network compromise efforts in Ukraine from December 2021.
They have also been spotted targeting Georgian government bodies with phishing emails, and their attacks demonstrated coordination and alignment with Russian state interests.
Last month, CERT-UA revealed another cyberattack linked to Russian military hacking group Sandworm against the country’s national news agency (Ukrinform) with the CaddyWiper data-wiping malware, which did not impact its operations.
The same group used CaddyWiper malware in another failed attack from April 2022 against a major Ukrainian energy supplier.
[ad_2]
Source link