[ad_1]

Trojanized Signal and Telegram apps containing the BadBazaar spyware were uploaded onto Google Play and Samsung Galaxy Store by a Chinese APT hacking group known as GREF.
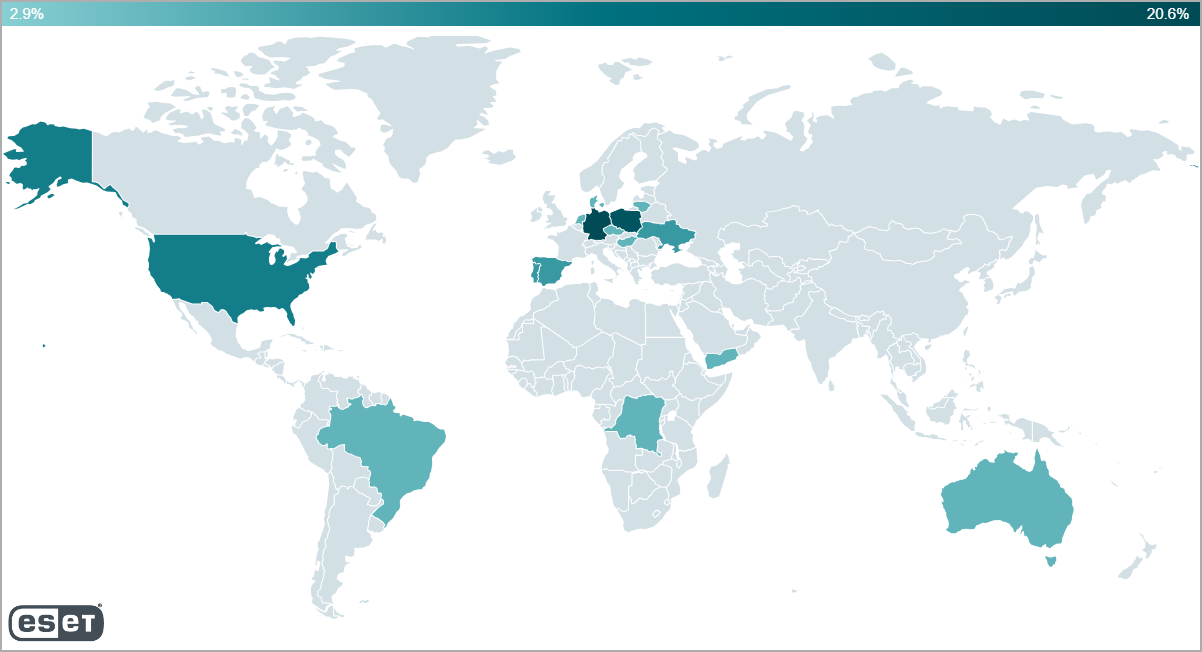
This malware was previously used to target ethnic minorities in China, but ESET’s telemetry shows that this time, the attackers target users in Ukraine, Poland, the Netherlands, Spain, Portugal, Germany, Hong Kong, and the United States.
BadBazaar’s capabilities include tracking the device’s precise location, stealing call logs and SMS, recording phone calls, taking pictures using the camera, exfiltrating contact lists, and stealing files or databases.
The trojanized apps containing BadBazaar code were discovered by ESET’s researcher, Lukas Stefanko.
Trojanized IM apps
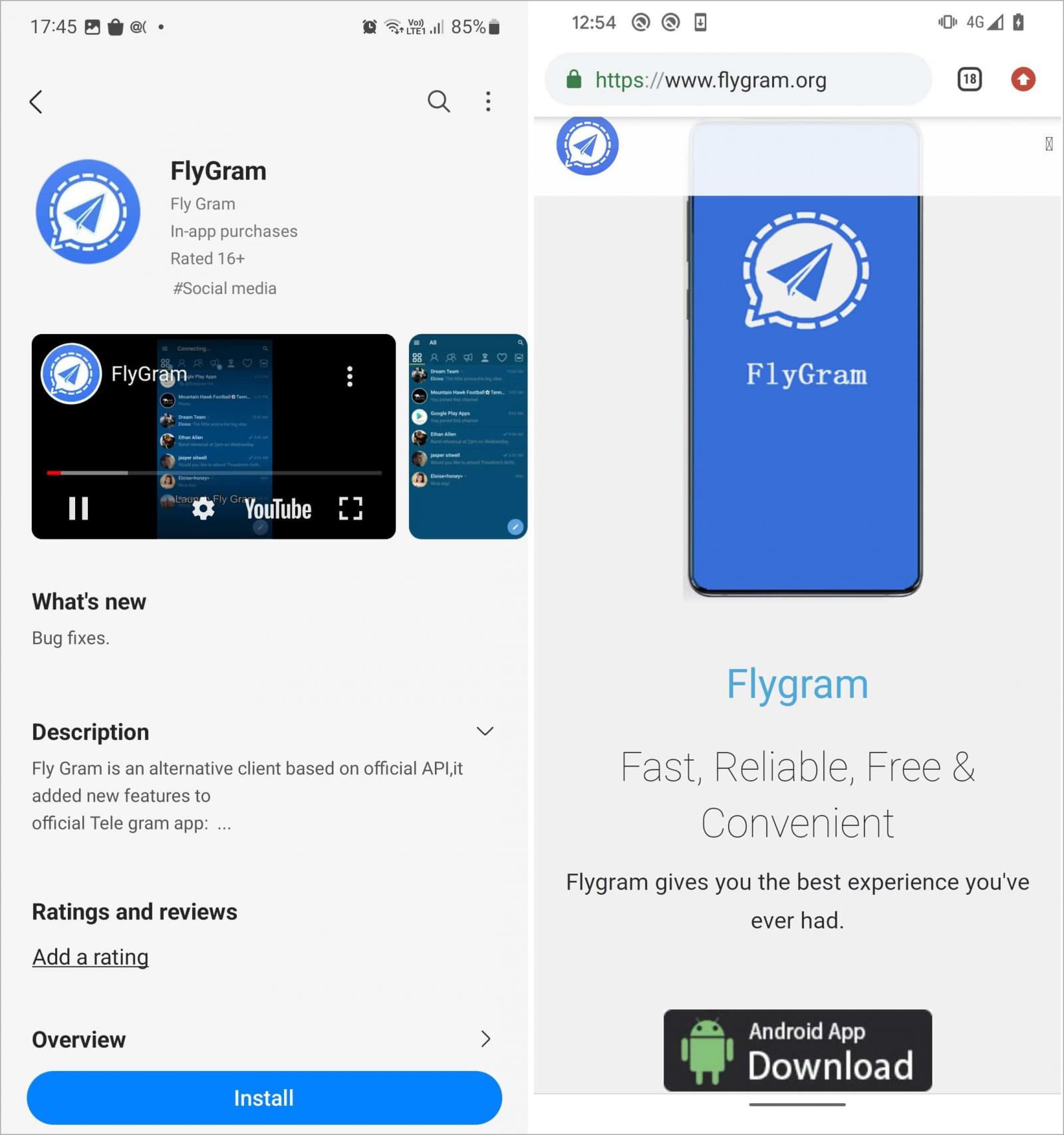
The two apps GREF used in its campaign are named ‘Signal Plus Messenger’ and ‘FlyGram,’ both being patched versions of the popular open-source IM apps Signal and Telegram.
The threat actors also set up dedicated websites at “signalplus[.]org” and “flygram[.]org” to add legitimacy to the malware campaign, offering links to install the app from Google Play or directly from the site.
ESET reports that FlyGram targets sensitive data like contact lists, call logs, Google Accounts, and WiFi data and also offers a dangerous backup feature that sends Telegram communication data to an attacker-controlled server.
Analysis of the available data shows that at least 13,953 FlyGram users enabled this backup feature, but the total number of users of the spyware app is undefined.
The Signal clone collects similar information but focuses more on extracting Signal-specific information like the victim’s communications and the PIN that protects their account from unauthorized access.
However, the fake Signal app includes a feature that makes the attack more interesting, as it allows the attacker to link a victim’s Signal accounts to attacker-controlled devices so the attackers can see future chat messages.
Signal includes a QR-code-based feature that allows you to link multiple devices to a single account so that chat messages can be seen from all of them.
The malicious Signal Plus Messenger abuses this feature by bypassing the QR-code linking process and automatically linking their own devices to victims’ Signal accounts without the victim knowing. This lets the attackers monitor all future messages sent from the Signal account.
“BadBazaar, the malware responsible for the spying, bypasses the usual QR code scan and user click process by receiving the necessary URI from its C&C server, and directly triggering the necessary action when the Link device button is clicked,” explains ESET.
“This enables the malware to secretly link the victim’s smartphone to the attacker’s device, allowing them to spy on Signal communications without the victim’s knowledge, as illustrated in Figure 12.”
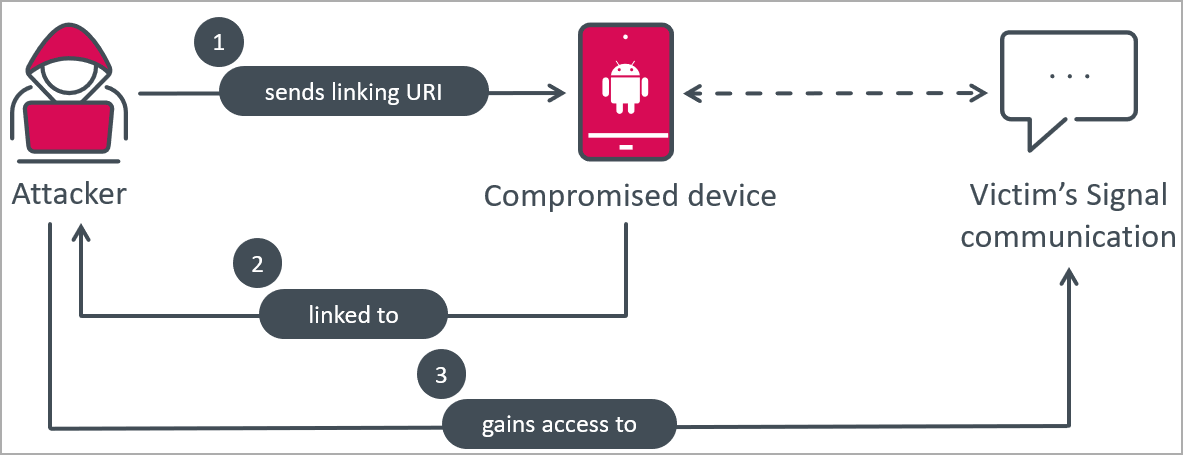
ESET says this method of spying on Signal has been used before as it’s the only way to obtain the content of Signal messages.
To figure out if rogue devices are linked to your Signal account, launch the real Signal app, go to Settings, and tap the “Linked Devices” option to view and manage all connected devices.
FlyGram was uploaded on Google Play in July 2020, and it was removed on January 6, 2021, having amassed a total of 5,000 installations through that channel.
Signal Plus Messenger was uploaded on Google Play and Samsung Galaxy store in July 2022, and Google removed it on May 23, 2023.
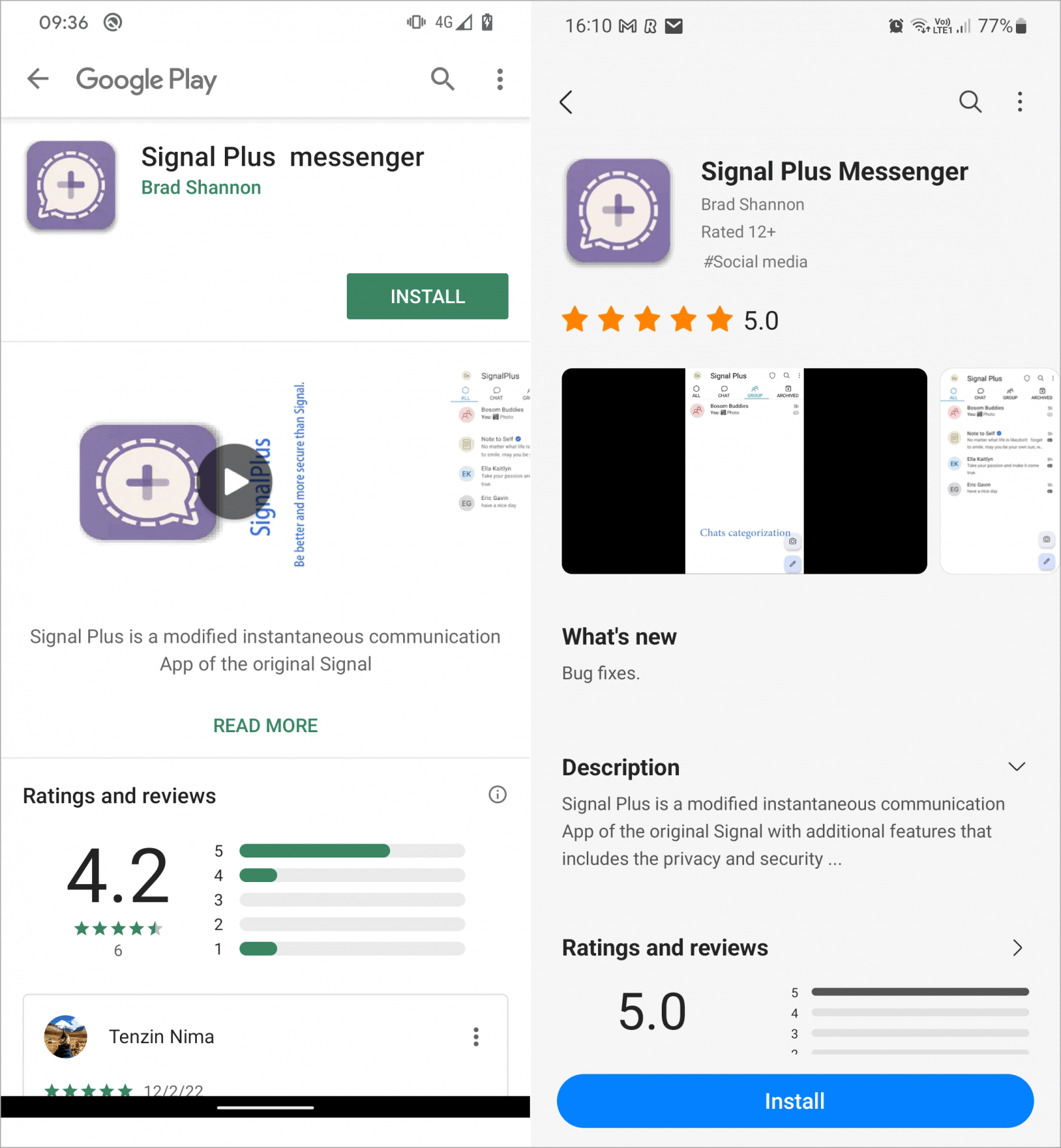
At the time of writing this, BleepingComputer confirmed that both apps were still available on the Samsung Galaxy Store.
Android users are recommended to use the original versions of Signal and Telegram and avoid downloading fork apps that promise enhanced privacy or additional features, even if those are available on official app stores.
[ad_2]
Source link
