[ad_1]

Cybersecurity company Trellix has fixed an incompatibility issue that caused Endpoint Security Agent’s Exploit Guard module to block certain Microsoft Office and third-party applications from opening after installing the June 2023 Cumulative Updates.
Microsoft says this known issue could also be triggered by exploit monitoring modules of other antivirus, antimalware, or security software.
Affected Windows versions include Windows 11 21H2/22H2, Windows 10 21H2/22H2, and Windows Server 2022.
“This issue only occurs with 32-bit applications running on 64-bit Windows with a version of Trellix Endpoint Security earlier than 35.31.25. Some known affected applications are Microsoft Outlook and other Microsoft Office applications”, Microsoft said.
“When trying to open an affected application, the event log shows an access violation with the error “module is unknown”.
“If you experience this issue with other security software installed or after installing the latest version of Trellix Endpoint Security Agent, please contact customer support for the security software you are using.”
Notably, this issue primarily affects non-consumer settings and is unlikely to affect customers using Windows devices within their home networks.
Google Chrome also impacted after June 2023 updates
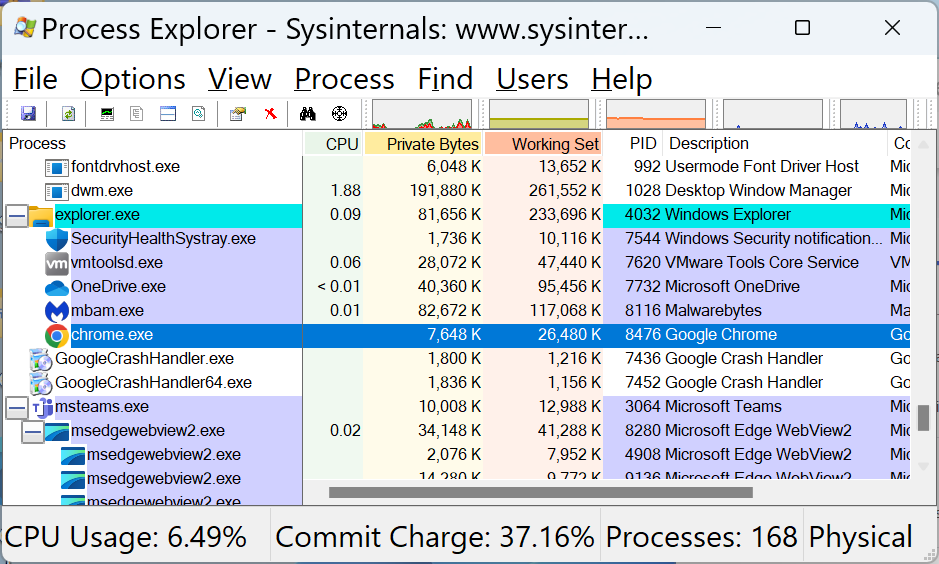
While Microsoft has only named Microsoft Outlook and other Microsoft Office apps as potentially impacting this known issue, the anti-exploit module of other security software also breaks Google Chrome after installation. this month’s cumulative Patch Tuesday updates.
Other security solutions incompatible with Windows June 2023 Updates include EDR and antivirus solutions from Malwarebytes, Cisco, and WatchGuard.
As confirmed by Malwarebytesthe problem is cause by Malwarebytes anti-exploit module prevents Chrome from fully loading after installing the Update KB5027231.
The same cumulative update would also break Google Chrome on Windows 11 systems protected by Cisco exploit prevention engines and WatchGuard.
Microsoft has not yet acknowledged that security software other than Trellix causes problems after the latest Windows updates.
As BleepingComputer previously reported, the Google Chrome process launches and runs on affected Windows systems, but is prevented from fully loading the UI due to the conflict.
While Trellix and Malwarebytes have now resolved this known issue, Cisco and WatchGuard customers are advised to disable Exploit Protection in their security software settings or set Google Chrome as their default web browser through the System Settings menu until a fix is available.
Microsoft spokespersons were unavailable for comment when repeatedly contacted by BleepingComputer for further details regarding this issue.
[ad_2]
Source link
