[ad_1]

Researchers from RWTH University of Aachen in Germany have published a study revealing that tens of thousands of container images hosted on Docker Hub contain confidential secrets, exposing software, online platforms and users with a massive attack surface.
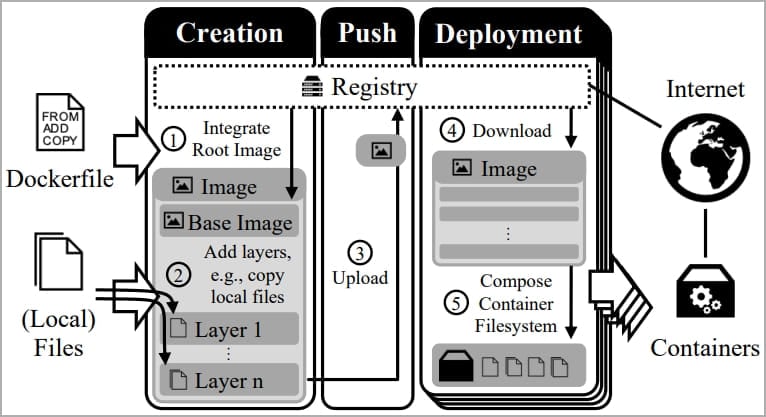
Docker Hub is a cloud-based repository for the Docker community to store, share, and distribute Docker images. These container building templates include all the software code, runtime environment, libraries, environment variables, and configuration files needed to easily deploy an application in Docker.
German researchers analyzed 337,171 Docker Hub images and thousands of private registries and found that around 8.5% contain sensitive data such as private keys and API secrets.
THE paper shows furthermore that many exposed keys are actively used, compromising the security of items that depend on them, such as hundreds of certificates.
Exposing (inadvertently) secrets
The study gathered a massive dataset of 1,647,300 layers from 337,171 Docker images, sourcing the latest versions of images from each repository when possible.
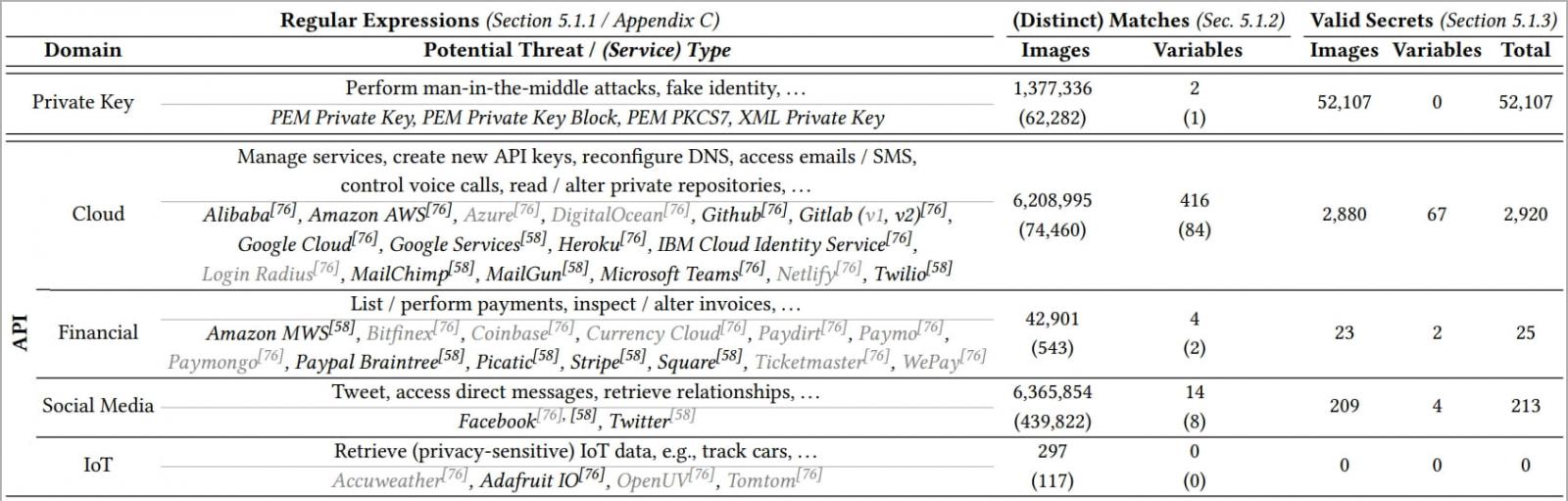
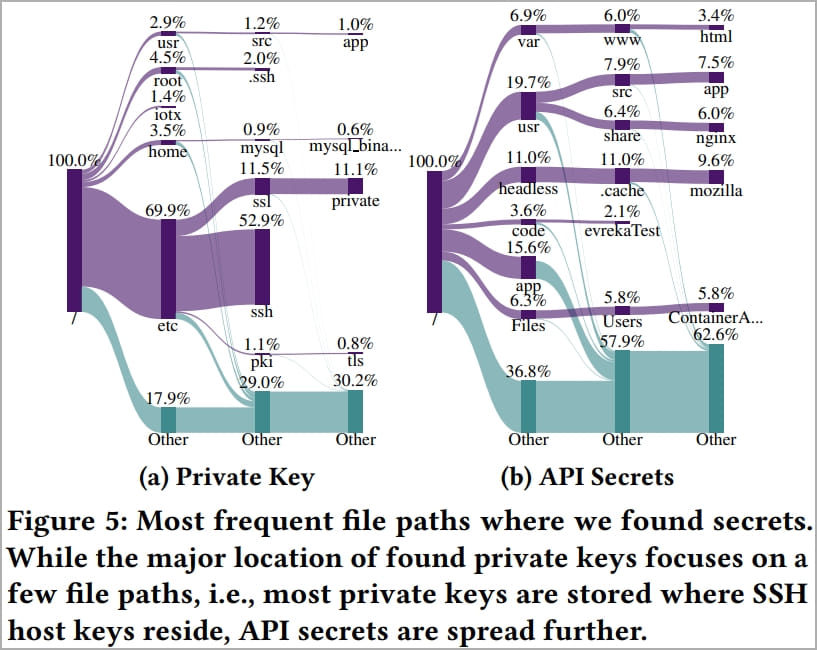
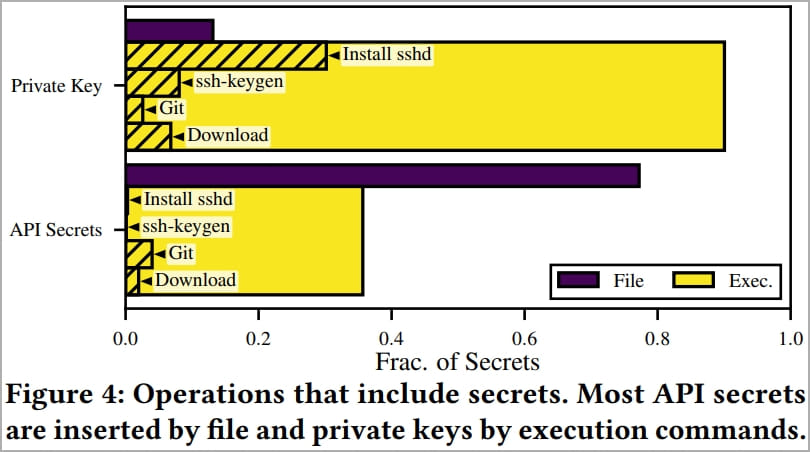
Data analysis using regular expressions to search for specific secrets revealed the exposure of 52,107 valid private keys and 3,158 distinct API secrets in 28,621 Docker images.
The numbers above have been validated by the researchers by excluding test keys, sample API secrets, and invalid matches.
Most of the exposed secrets, 95% for private keys and 90% for API secrets, resided in single-user images, indicating that they were likely leaked inadvertently.
The highest impact was on Docker Hub, which had a secret exposure percentage of 9.0%, while images from private registries exposed secrets at a rate of 6.3%.
This difference may indicate that Docker Hub users generally have a poorer understanding of container security than those setting up private repositories.
Using Exposed Keys
Next, the researchers needed to determine the actual use of the exposed secrets to gauge the size of the attack surface.
Alarmingly, 22,082 compromised certificates based on the exposed private keys were found, including 7,546 certificates signed by a private CA and 1,060 certificates signed by a public CA.
One thousand certificates signed by a CA are of particular concern because these certificates are generally used by a large number of users and are universally accepted.
At the time of the study, 141 CA-signed certificates were still valid, which somewhat mitigates the risk.
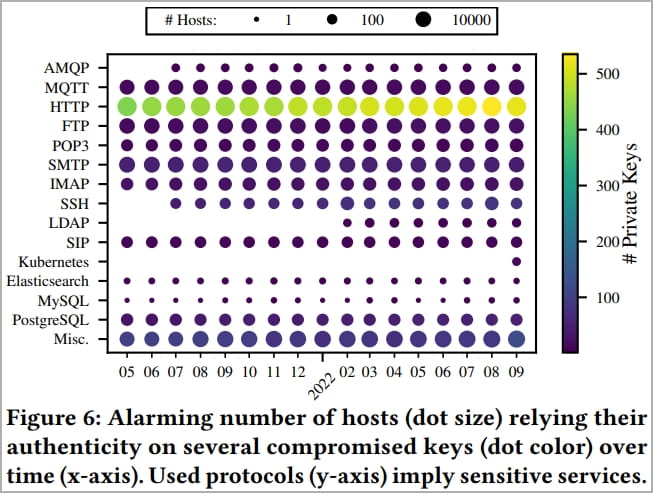
To further determine the use of exposed secrets in the wild, researchers used 15 months of Internet-wide measurements provided by the Censys database and found 275,269 hosts that rely on the keys. compromised.
These include:
- 8,674 MQTT And 19 AMQP hosts that potentially transfer privacy-sensitive Internet of Things (IoT) data.
- 6,672 FTPs, 426 PostgreSQL, 3 Elastic searchAnd 3 MySQL instances that serve potentially confidential data.
- 216 SIP hosts used for telephony.
- 8,165 SMTPs, 1,516 POP3And 1,798 IMAP servers used for email.
- 240 SSH servers And 24 Kubernetes instances that use leaked keys that can lead to remote shell access, the extension of botnets, or additional data access.
This level of exposure highlights a huge container security problem and a negligence in creating images without first sanitizing them of their secrets.
When it comes to API exposure, the analysis found that most containers (2,920) belong to cloud providers like Amazon AWS, but some were from financial services like Stripe.
However, the researchers cited ethical limitations in validating exposed API secrets against their service endpoints, so their use in the wild is unknown.
[ad_2]
Source link
