[ad_1]

Business Email Compromise (BEC) is a growing threat to businesses of all sizes. As the BEC attacks almost doubled over the entire Verizon DBIR incident dataset and represent more than 50% of incidents in the social engineering model.
Attackers use various tactics to gain access to sensitive information, such as compromising the email account and using a legitimate email address to launch the attack.
BEC attacks can occur in different ways, using a variety of methods. But what makes them different and arguably more dangerous is that they are driven by intent. BED attacks target specific individuals within organizations and have messages that are often personalized for the intended victim.
These strategies include spoofing an existing email or website, or spear phishing (using emails from trusted sources). Read on to learn how these attacks work and how protect yourself against them.
Recognizing a Business Email Compromise Attack
Running a business is complex, and with so many moving parts, attackers can try different angles, targeting C-level executives, shipping departments, billing, or IT.
Internal and external threats can arise, but 83% of offenses involved external actors with financial motivations. With this, it is best to explore several real-world attacks to learn from them.
CEO Fraud
This type of attack involves a threat actor impersonating a C-suite individual, such as the CEO or CFO of a company. The attacker would then send an email to someone in the finance department requesting a transfer of funds.
The transferred funds would be directed to an account controlled by the attacker.
To make the attack more effective, the threat actor may have researched their targets and attempted to match their language, terminology, style, and email address as closely as possible.
If the target is not careful, they can fall into the trap and transfer the funds.
Account Compromise
In a more insidious attack, an attacker can compromise an existing employee’s email account from the inside. With access to this compromised account, the attacker can then request payments from vendors who are accounts controlled by the attacker.
For example, Joe in the purchasing department could have his account compromised. His email could then send many billing requests that look like standard payment requests to suppliers, usually for smaller amounts.
Since the request is from a trusted account, billing may not take a close look at it and pay the provider. Additionally, larger companies may need more resources to audit each request, leading to many missed requests.
False invoice system
An attacker can send an email to a company demanding payment of an invoice, insisting that they are overdue for services rendered.
An overwhelmed billing department may not hesitate to pay it, especially if the email and invoice look legitimate and mimic those of previous providers.
Additionally, an attached PDF may contain malware, allowing an account compromise attack.
Lawyer impersonation
While most attacks in this area have focused on the supplier supply chain, this attack targets the natural unease many people face with legal issues.
An alleged lawyer contacts the target and demands payment of a settlement or threatens legal action if payment is not received.
Rather than risk being on the wrong side of the law or getting embroiled in a lawsuit, some employees can pay the requested funds to avoid trouble. Business can be extremely expensive, so paying the lowest amount can be an attractive option to make the problem go away without hiring expensive corporate lawyers.
Data theft
A typical attack targeting human resources employees involves data theft. The goal is to collect personal and sensitive information about people in positions of power for reconnaissance purposes.
With this information, an attacker can launch more sophisticated schemes, such as CEO Fraud, leveraging the intimate details they have acquired to make their emails more credible.
Compromising business email
BEC attacks are a type of social engineering attack that takes place via email. The attacker forges an email to trick the victim into performing an action.
In these situations, the goal is not only for the target to perform the requested task, but also to compromise their computer for future attacks against the company. A compromised computer can quickly reveal private employee and company information.
For example, with a compromised email account, an attacker could see that a company is working with a specific provider. The attacker could then create an email from the compromised account and send it to the billing department, requesting payment from the same vendor but to an account controlled by the attacker.
So what can a business do to protect against this type of theft? In addition to providing in-depth training on the types of attacks and social engineering needed to perform this theft, a business needs a robust security infrastructure if an account is compromised. This includes implementing strong password policies to prevent the use of compromised credentials in attacks.
Protect User Accounts with Specops Password Policy
BEC (Business Email Compromise) attacks can have a devastating impact on a business and it is essential to take steps to mitigate the risk.
Passwords remain a crucial factor, because 49% of offenses by external actors involved the use of stolen credentials, so it is important to enforce strong password policies.
Specops password policy with Breached Password Protection, helps you increase password security in your Microsoft Active Directory environment while blocking over three billion known compromised passwords.
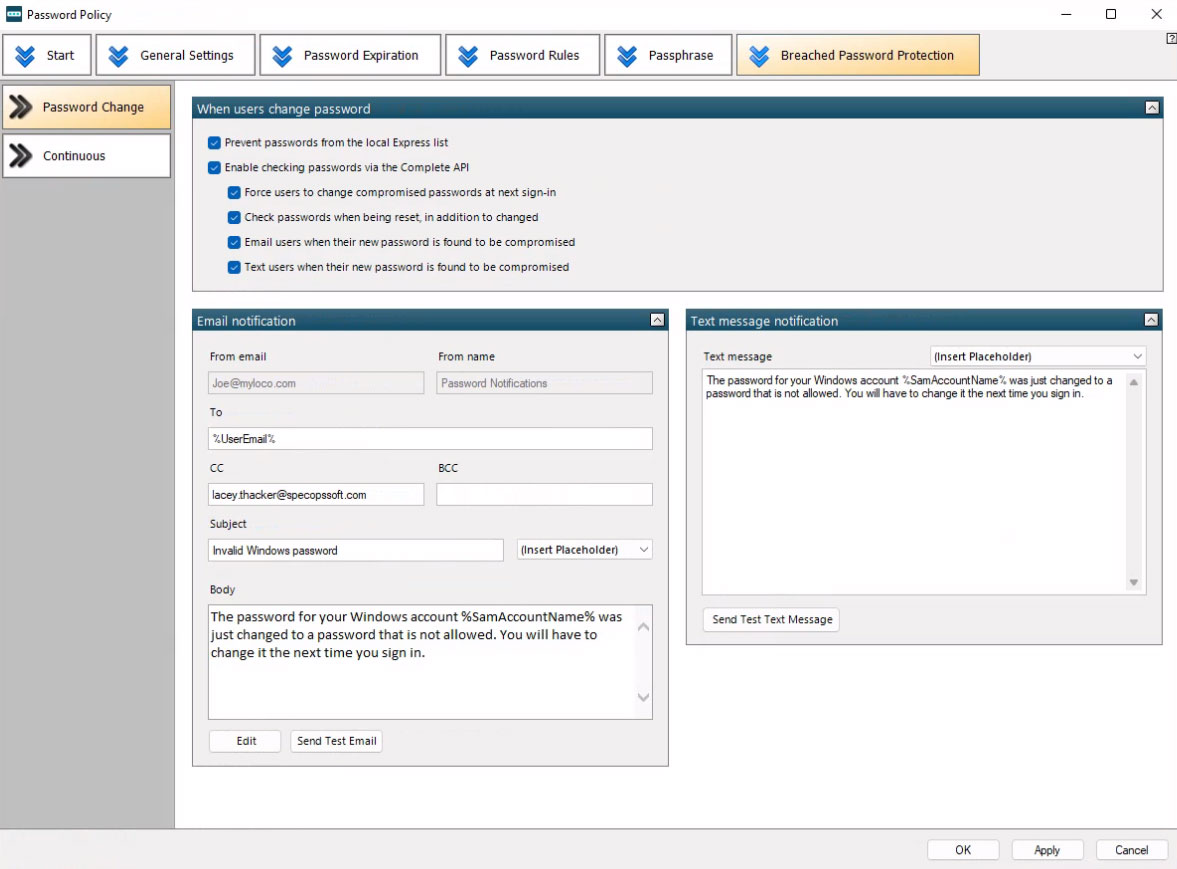
The tool extends Group Policy functionality and simplifies fine-grained password policy management while providing real-time dynamic feedback to the end user during password creation.
The Danger of Business Email Compromise Attacks
As more businesses move online, business email compromise (BEC) attacks will become more common and difficult to detect.
But, with proper education and vigilance on the part of employees, coupled with a robust password policy such as that offered by Specops password policythese attacks can be mitigated.
Organizations want to avoid being the victims of such an attack, especially one that can result in huge financial loss, because 95% of all offenses are financially motivated.
By learning about the types of attacks and taking preventive measures, you can ensure that your business is better protected.
Sponsored and written by Specops software
[ad_2]
Source link
