[ad_1]

A Chinese APT hacking group known as “Evasive Panda” is linked to a mysterious attack that distributed the MsgBot malware as part of an automatic update to the Tencent QQ messaging app.
Evasive Panda is a cyber espionage group active since at least 2012 that previously targeted organizations and individuals in mainland China, Hong Kong, Macau, Nigeria, and various countries in Southeast and East Asia.
The threat actor’s latest campaign was uncovered by ESET security researchers in January 2022, who report seeing signs that the operation began in 2020.
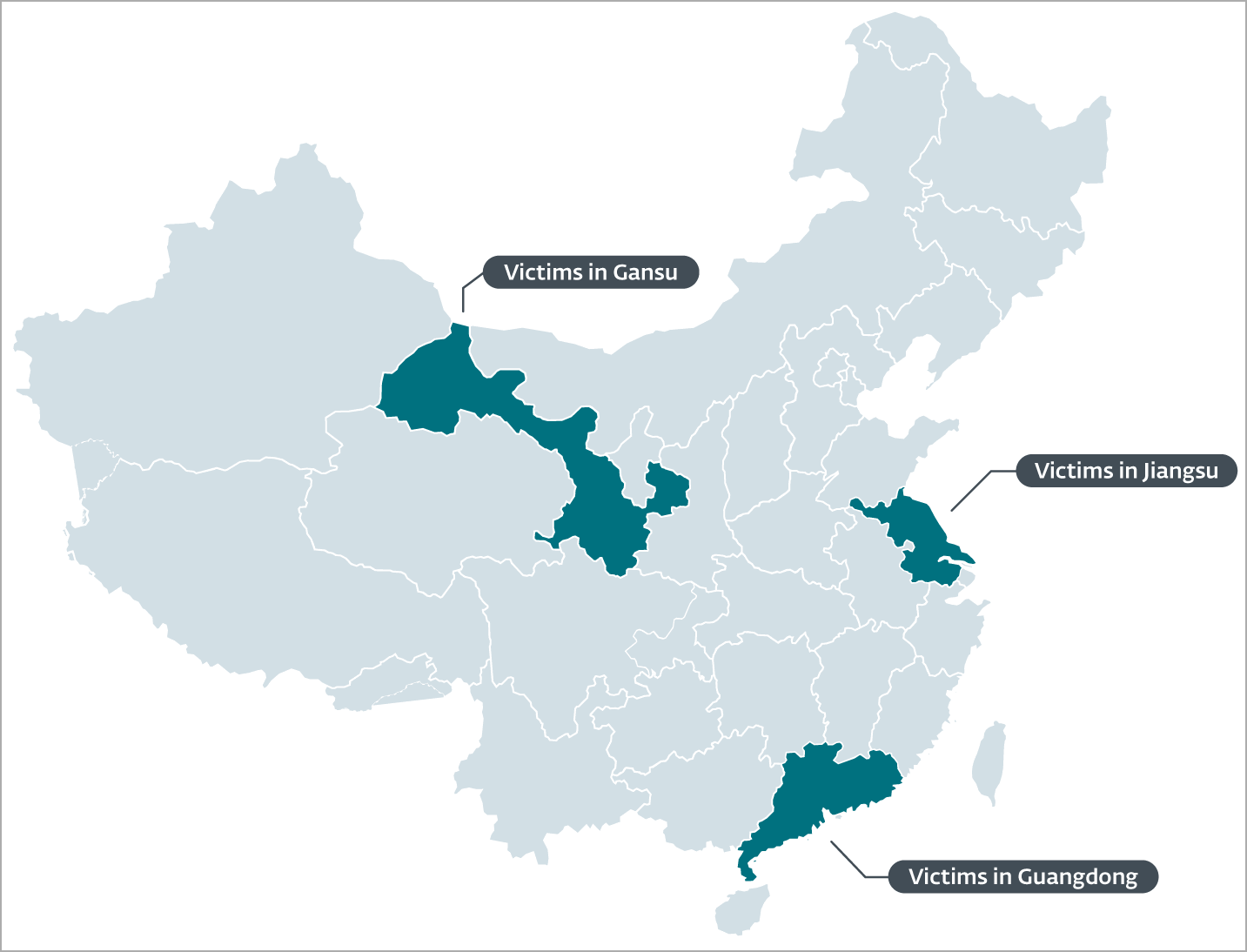
Most of the victims of the campaign are members of an international NGO (non-governmental organization) and are located in the provinces of Gansu, Guangdong and Jiangsu, indicating rather specific and targeted targeting.
Supply chain or AITM?
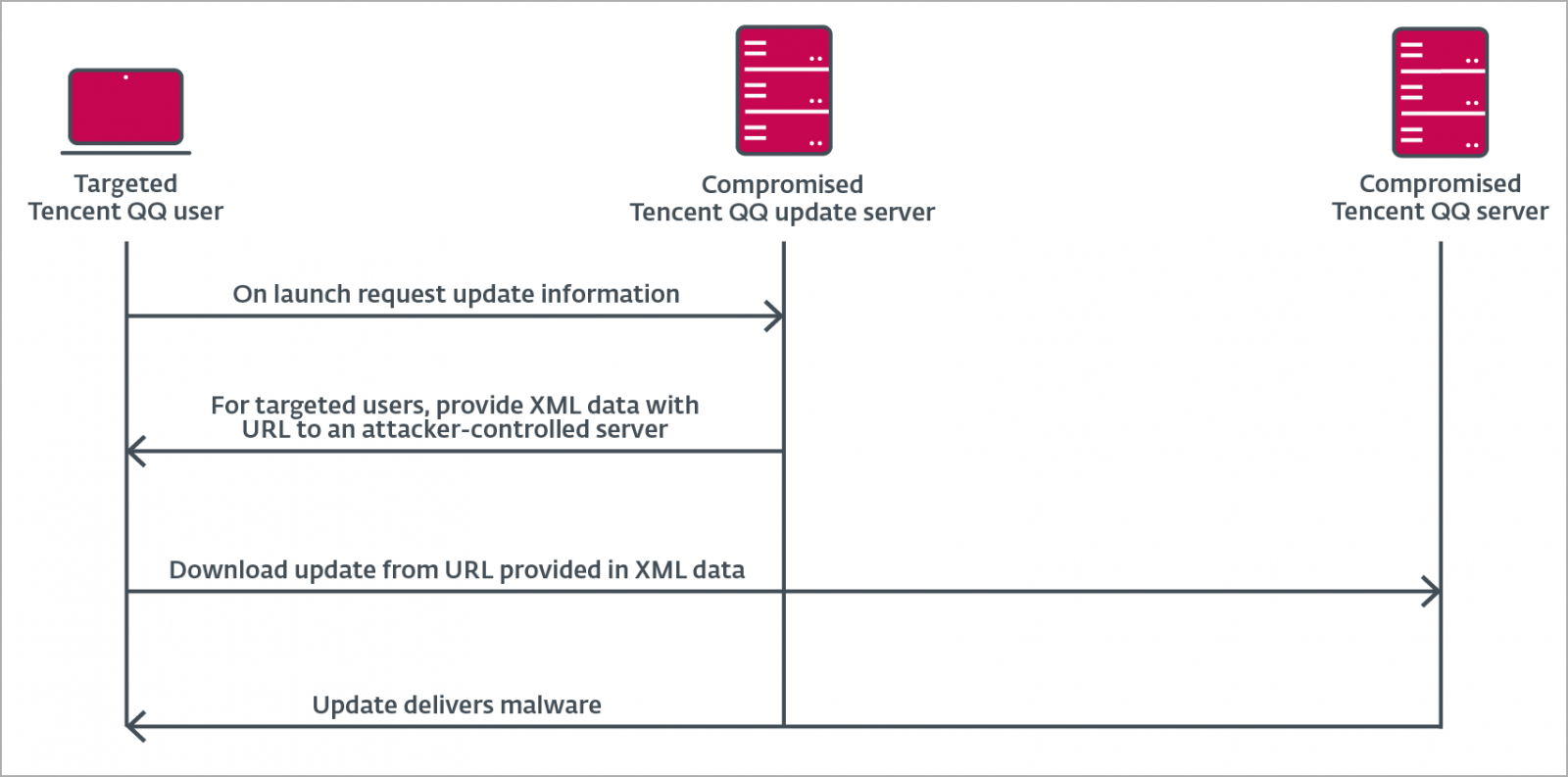
ESET reports that the malicious payload of the MsgBot malware was delivered to victims as a Tencent QQ software update from legitimate URLs and IP addresses belonging to the software developer.
This means that there can be two possible scenarios for the attack – a supply chain attack or an adversary in the middle (AITM) attack.
In the first scenario, Evasive Panda would have to break into Tencent QQ’s update distribution servers to trojanize the “QQUrlMgr.exe” file delivered to victims under the guise of a legitimate software update.
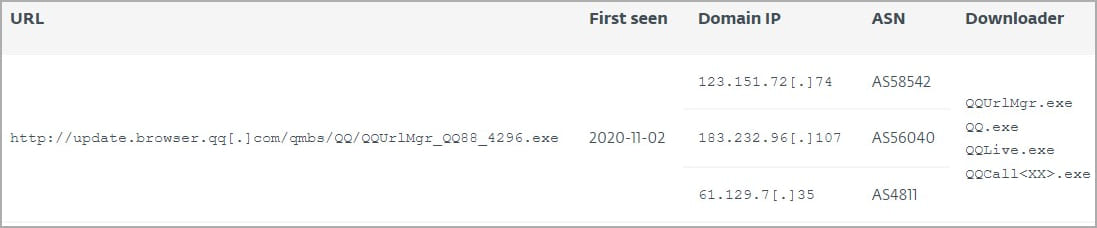
ESET has noticed that Trojan-containing versions of the update file fetch malware from a hard-coded URL (“update.browser.qq[.]com”) and use a hard-coded decryption key that matches the correct MD5 hash provided by the server. However, the legitimacy of this URL has not yet been validated and Tencent did not respond to ESET’s question.
Additionally, analysts were unable to retrieve a sample of XML update data from the server, which would reveal the malware distribution mechanism.
In an AiTM scenario, ESET noticed striking similarities to previous campaigns using this tactic, including one of the LuoYu APTs that Kaspersky highlighted in a 2022 report.
This older campaign used “WinDealer” malware which generated random China Telecom IP addresses to perform AITM or interception of the attacker on the side. These IP addresses appear to be on the same ranges that delivered the MgBot malware in the Evasive Panda campaign.
Although both scenarios are plausible based on observed coincidences and possible explanations, ESET could not find evidence pointing to a clear direction, and many questions remain unanswered.
BleepingComputer contacted ESET and Tencent with further questions about the attack.
The MgBot Malware
The MgBot payload delivered in this campaign is a C++ Windows backdoor that Evasive Panda has been using since it began operations in 2012.
ESET reports that the malware’s installer, backdoor, functionality and execution chain have remained largely unchanged since Malwarebytes analyzed them in 2020.
MgBot uses a modular architecture to extend its functionality, receiving DLL plugins from C2 that perform specialized functions, including:
- Keylogging on specific Tencent apps
- Steal files from hard drives and USB drives
- Capturing copied text to clipboard
- Capture input and output audio streams
- Theft of Outlook and Foxmail email client credentials
- Stealing credentials from Chrome, Opera, Firefox, Foxmail, QQBrowser, FileZilla, WinSCP, etc.
- Steal content from Tencent QQ database which stores user’s message history
- Steal information from Tencent WeChat
- Steal cookies from Firefox, Chrome and Edge
In conclusion, the Evasive Panda APT was found targeting users in China, aiming to steal data primarily from Chinese apps, exploiting an unclear method to perform a supply chain attack on Tencent software QQ.
This is a hallmark example of the group’s high-level capabilities that go beyond standard infection methods like social engineering, phishing, SEO poisoning, etc., and call for greater vigilance potential targets.
[ad_2]
Source link
